Source: www.infosecurity-magazine.com – Author: Several countries are “relentlessly” seeking information about Australia’s military capabilities, including the country’s submarine partnership with the UK and the US, warned...
Author: CISO2CISO Editor 2
Cyber Investor Insight Partners Suffers Security Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: New York-based venture capital firm Insight Partners has confirmed it was hit by a cyber-attack in January 2025. In a public statement...
Hackers gain root access to Palo Alto firewalls through chained bugs – Source: www.csoonline.com
Source: www.csoonline.com – Author: A recently disclosed medium-severity bug was chained with critical, older bugs to gain root-level access to PAN firewall systems. A high-severity authentication...
Mehrheit der Deutschen fürchtet sich vor Cyberangriffen – Source: www.csoonline.com
Source: www.csoonline.com – Author: Hacker-Attacken aus dem Ausland, zerstörte Strom- und Datenkabel in der Ostsee, Angriffe auf die kritische Infrastruktur. Eine Reihe von Vorfällen dieser Art...
Think being CISO of a cybersecurity vendor is easy? Think again – Source: www.csoonline.com
Source: www.csoonline.com – Author: Making the shift from a security product developer to the same role at an enterprise taught made one CISO more prepared, more...
Customer Identity & Access Management: Die besten CIAM-Tools – Source: www.csoonline.com
Source: www.csoonline.com – Author: Customer Identity and Access Management liefert die Grundlage, um den Zugriff Dritter auf das Unternehmensnetz besser zu managen und zu kontrollieren. Das...
OpenSSH fixes flaws that enable man-in-the-middle, DoS attacks – Source: www.csoonline.com
Source: www.csoonline.com – Author: Researchers from Qualys found two vulnerabilities that can be combined to bypass the server key verification in OpenSSH clients when the VerifyHostKeyDNS...
Ransomware-Banden geben Opfern immer weniger Zeit – Source: www.csoonline.com
Source: www.csoonline.com – Author: Ransomware-Banden agieren viel schneller als früher. Dadurch bleibt Unternehmen weniger Zeit, Ransomware-Attacken zu erkennen. Ransomware-Gruppen haben den Zeitraum bis zur Lösegeldübergabe immer...
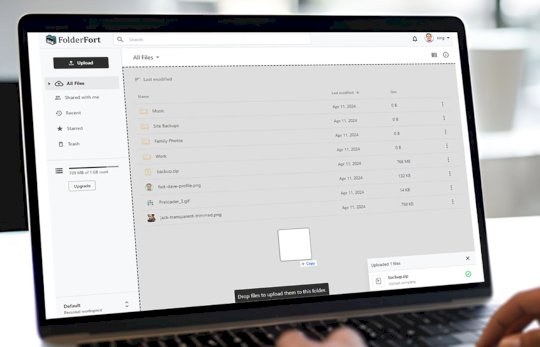
Get a Lifetime of 1TB Cloud Storage for Only $60 With FolderFort – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published February 18, 2025 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...
How to Fix the Four Biggest Problems with Failed VPN Connections – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Erik Eckel Virtual private networks have risen from obscurity to become the frequently preferred method of linking private networks. Although VPNs became...
New Mac Malware Poses as Browser Updates – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse A new macOS malware called FrigidStealer is spreading through fake browser update alerts, allowing attackers to steal sensitive data, according...
US Military, Defense Contractors Infected with Infostealers: Hudson Rock – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Hundreds of computers in the U.S. Army and Navy and high-profile defense are infected with information-stealing malware that can lead...
PCI DSS 4: 6.4.3/11.6.1 – A Guide to SAQ A-EP Compliance using Feroot PaymentGuard AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: mykola myroniuk In this article Introduction: Payment Security Made Simple For SAQ A-EP merchants, securing payment pages requires sophisticated monitoring and compliance...
Randall Munroe’s XKCD ‘Hardwood’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
Leveraging AI to Stay Ahead in Cybersecurity: A Conversation with Chandra Pandey and Joshua Skeens, CEO of Logically – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maggie MacAlpine At Seceon’s 2025 Q1 Innovation and Certification Days, Seceon CEO Chandra Pandey and Joshua Skeens, CEO of Seceon’s partner Logically...
DEF CON 32 – Manufacturing Lessons Learned, Lessons Taught – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Tuesday, February 18, 2025 Home » Security Bloggers Network » DEF CON 32 – Manufacturing Lessons Learned, Lessons Taught Authors/Presenters:...
Learn & Avoid Social Engineering Scams in 2025 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kayla Kinney In the past decade, social engineering attacks have become more sophisticated and prevalent than ever. From AI voice impersonation to...
Intruder Enhances Free Vulnerability Intelligence Platform ‘Intel’ with AI-Generated CVE Descriptions – Source: securityboulevard.com
Source: securityboulevard.com – Author: cybernewswire Intel by Intruder now uses AI to contextualize NVD descriptions, helping security teams assess risk faster. Intruder, a leader in attack...
Cybersecurity in 2025: AI, Attack Surfaces and the Shift to Cyber Resilience – Source: securityboulevard.com
Source: securityboulevard.com – Author: Krista Case Hello, I’m Krista Case, research director on the team here at The Futurum Group. I’m here today to walk you...
Cybersecurity Predictions for 2025: Platforms, Convergence and the Future of Risk Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Fernando Montenegro Hello, I’m Fernando Montenegro and I recently joined Futurum Research as Vice President and Practice Lead for Cybersecurity Research. You...
Pangea Launches AI Guard and Prompt Guard to Combat Gen-AI Security Risks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend AI security specialist Pangea has added to its existing suite of corporate gen-AI security products with AI Guard and Prompt...
MirrorTab Raises $8.5M Seed Round to Take on Browser-Based Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine MirrorTab, a San Francisco startup building technology to neutralize malicious attacks at the browser layer, has secured $8.5 million in...
Finastra Starts Notifying People Impacted by Recent Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire British fintech giant Finastra last week started sending written notifications to individuals who had their personal information stolen in a...
Critical Vulnerability Patched in Juniper Session Smart Router – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Juniper Networks last week published an out-of-cycle security bulletin to inform customers about the availability of patches for a critical...
Singulr Launches With $10M in Funding for AI Security and Governance Platform – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Singulr AI launched on Tuesday, announcing the general availability of its enterprise AI security and governance platform. With offices in...
Golang Backdoor Abuses Telegram for C&C Communication – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A recently discovered backdoor written in the Go programming language is abusing Telegram for command-and-control (C&C) communication, cybersecurity firm Netskope...
Microsoft Warns of Improved XCSSET macOS Malware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A new variant of the sophisticated XCSSET malware has been observed in recent, limited attacks against macOS users, Microsoft reports....
Palo Alto Networks Confirms Exploitation of Firewall Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Palo Alto Networks has confirmed for SecurityWeek that a recently patched firewall vulnerability tracked as CVE-2025-0108 is being actively exploited....
Xerox Printer Vulnerabilities Enable Credential Capture – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Soure: T. Schneider via Shutterstock A popular small to midrange Xerox business printer contains two now-patched vulnerabilities in...
China-Linked Threat Group Targets Japanese Orgs’ Servers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: KB Photodesign via Shutterstock NEWS BRIEF Winnti, a China-affiliated threat actor, has been linked to...