Source: www.csoonline.com – Author: GenAI simplifies work – for companies as well as for attackers and malicious insiders. CISOs need to be prepared. It’s every company’s...
Author: CISO2CISO Editor 2
News alert: INE Security’s focus on practical security training enhances career stability in tech – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cybernewswire Cary, NC, Feb. 19, 2025, CyberNewswire — 2025 marks a time of unprecedented volatility in the technology job market. On one...
Darktrace: 96% of Phishing Attacks in 2024 Exploited Trusted Domains Including SharePoint & Zoom Docs – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson Threat actors are increasingly targeting trusted business platforms such as Dropbox, SharePoint, and QuickBooks in their phishing email campaigns and...
Duo vs Microsoft Authenticator: Which Tool Is Better? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
DEF CON 32 – Dysfunctional Unity: The Road To Nowhere – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, February 19, 2025 Home » Security Bloggers Network » DEF CON 32 – Dysfunctional Unity: The Road To Nowhere...
Migrating from kOps to EKS: A Technical Guide for When & Why to Switch – Source: securityboulevard.com
Source: securityboulevard.com – Author: Abdul Akhter As Kubernetes continues to mature, so do the tools we use to manage it. In this blog post, we’ll explore...
Randall Munroe’s XKCD ‘Archive Request’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
From Defense to Offense: Inside-Out Data Security Strategies for CISOs in 2025 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anuj Jaiswal As organizations continue to generate and store colossal volumes of data — everything from customer records to intellectual property —...
Your Social Security Number is on the Dark Web: What Do You Do? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bogdan Botezatu If you’re worried about your Social Security number being shopped on the dark web, where cybercriminals go to buy and...
News alert: INE Security’s focus on practical security training enhances career stability in tech – Source: securityboulevard.com
Source: securityboulevard.com – Author: cybernewswire Cary, NC, Feb. 19, 2025, CyberNewswire — 2025 marks a time of unprecedented volatility in the technology job market. On one...
DEF CON 32 – MoWireless MoProblems: Modular Wireless Survey Sys. & Data Analytics – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, February 19, 2025 Home » Security Bloggers Network » DEF CON 32 – MoWireless MoProblems: Modular Wireless Survey Sys....
CaaS Surges in 2025, Along With RATs, Ransomware – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy Cybercrime-as-a-Service (CaaS) now accounts for 57% of all cyberthreats, marking a 17% increase from the first half of 2024, according...
Securing multi-environment deployments: Cloud, on-premise, and air-gapped – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aaron Linskens Modern software delivery makes use of many different deployment environments, from public cloud to private cloud and traditional on-premise data...
Flaws in Xerox VersaLink MFPs Spotlight Printer Security Concerns – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Security flaws found in Xerox VersaLink C7025 multifunction printers (MFPs) could allow attackers to grab authentication credentials, which would pave...
How Hackers Manipulate Agentic AI with Prompt Engineering – Source: www.securityweek.com
Source: www.securityweek.com – Author: Etay Maor The era of “agentic” artificial intelligence has arrived, and businesses can no longer afford to overlook its transformative potential. AI...
CISO Conversations: Kevin Winter at Deloitte and Richard Marcus at AuditBoard – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Deloitte is one of the largest professional services firms in the world, providing services in audit, consulting, financial advisory, risk...
Blockaid Raises $50 Million to Secure Blockchain Applications – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Blockchain application security startup Blockaid on Tuesday announced raising $50 million in a Series B funding round that brings the...
OpenSSH Patches Vulnerabilities Allowing MitM, DoS Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire On Tuesday, the developers of OpenSSH, the popular open source implementation of the Secure Shell (SSH) protocol, rolled out patches...
VC Firm Insight Partners Hacked – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Private equity and venture capital company Insight Partners revealed on Tuesday that it was recently targeted in a cyberattack that...
Chrome 133, Firefox 135 Updates Patch High-Severity Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Google and Mozilla on Tuesday announced fresh security updates for Chrome 133 and Firefox 135 to address high-severity memory safety...
New FrigidStealer macOS Malware Distributed as Fake Browser Update – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A newly identified information stealer malware targeting macOS users is being distributed through a compromised website as a browser update,...
Free Diagram Tool Aids Management of Complex ICS/OT Cybersecurity Decisions – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Admeritia has announced the availability of a new tool designed to help organizations manage complex cybersecurity decisions related to industrial...
Device Code Phishing – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier This isn’t new, but it’s increasingly popular: The technique is known as device code phishing. It exploits “device code flow,”...
The AI Fix #37: DeepSeek is a security dumpster fire, and quicksand for AI – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Skip to content In episode 37 of “The AI Fix”, Google Gemini gets the munchies, the wettest country in the...
Spam and phishing in 2024 – Source: securelist.com
Source: securelist.com – Author: Tatyana Kulikova, Olga Svistunova, Roman Dedenok, Andrey Kovtun, Irina Shimko, Anna Lazaricheva The year in figures 27% of all emails sent worldwide...
Patch Now: CISA Warns of Palo Alto Flaw Exploited in the Wild – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Chiew via Shutterstock Attackers are actively exploiting an authentication bypass flaw found in the Palo Alto Networks...
What Is the Board’s Role in Cyber-Risk Management in OT Environments? – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Cusimano John Cusimano, Vice President, OT Security, Armexa February 19, 2025 4 Min Read Source: Lev Dolgachov via Alamy Stock Photo...
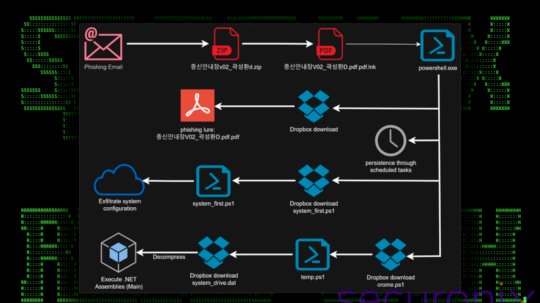
North Korea’s Kimsuky Taps Trusted Platforms to Attack South Korea – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer North Korea-linked threat groups are increasingly using living-off-the-land (LotL) techniques and trusted services to evade detection, with a...
Deepwatch Acquires Dassana to Boost Cyber-Resilience With AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Gajus via Adobe Stock Photo NEWS BRIEF Deepwatch, an artificial intelligence (AI) and human cyber-resilience platform provider, has...
CVE-2025-26465 & CVE-2025-26466 Vulnerabilities Expose Systems to Man-in-the-Middle and DoS Attacks – Source: socprime.com
Source: socprime.com – Author: Veronika Telychko Two newly uncovered security flaws in the open-source OpenSSH suite tracked as CVE-2025-26465 and CVE-2025-26466 could enable adversaries to launch...