Source: securityboulevard.com – Author: Contrast Marketing Have you silenced WAF alerts in your SIEM or just stopped sending them altogether? You’re not alone. Many SOCs find...
Author: CISO2CISO Editor 2
Mozilla Revises Firefox Terms of Use After Inflaming Users Over Data Usage – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Esther Shein Image: iStock Mozilla wants to set the record straight: The company needs a license “to make some of the basic...
EU’s New Product Liability Directive & Its Cybersecurity Impact – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jatin Mannepalli Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Latin American Orgs Face 40% More Attacks Than Global Average – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Cisco’s SnapAttack Deal Expands Splunk’s Capabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
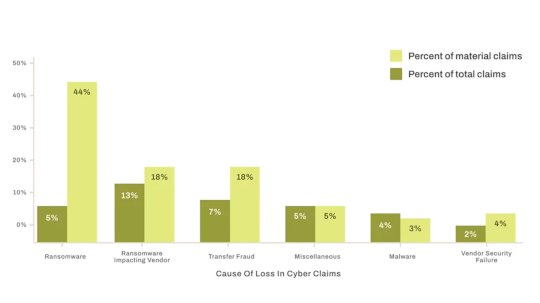
Third-Party Risk Top Cybersecurity Claims – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Stop targeting Russian hackers, Trump administration orders US Cyber Command – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley For years, the United States has joined with much of the rest of the world, in declaring that Russia poses...
Mobile malware evolution in 2024 – Source: securelist.com
Source: securelist.com – Author: Anton Kivva These statistics are based on detection alerts from Kaspersky products, collected from users who consented to provide statistical data to...
Black Basta Leak Offers Glimpse Into Group’s Inner Workings – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend A massive hoard of internal chats has been leaked from the Black Basta ransomware group, rivalling the Conti leaks of...
Ransomware access playbook: What Black Basta’s leaked logs reveal – Source: www.csoonline.com
Source: www.csoonline.com – Author: Analyzing leaked internal communication logs, security researchers are piecing together how one of the most notorious ransomware groups infiltrates its victims. Black...
Why cyber attackers are targeting your solar energy systems — and how to stop them – Source: www.csoonline.com
Source: www.csoonline.com – Author: Businesses that install and own solar distributed energy resources increase their attack surface and that of the electric grid. High energy costs...
Die besten XDR-Tools – Source: www.csoonline.com
Source: www.csoonline.com – Author: XDR-Tools bieten tiefergehende und automatisierte Möglichkeiten, Bedrohungen zu stoppen. Das sind die besten Lösungen im Bereich Extended Detection and Response. Lesen Sie,...
11 Application Security Testing Types – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cycode Team As organizations accelerate their release cycles and rely on complex software ecosystems, security vulnerabilities become harder to track—and easier for...
Justified Spending on Cybersecurity Technology? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn With digital becoming more complex, organizations are continually urged to increase their cybersecurity spending. But the crucial question that arises...
How Supported is Your NHIs Policy Enforcement? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Does Your Approach to NHI Policy Enforcement Make the Grade? One question that often arises is: “how effectively are we...
Freedom to Choose the Best Secrets Vault? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are You Making Informed Decisions About Your Secrets Vault? It’s a question that resonates deeply among cybersecurity professionals today. A...
When Your SaaS Vendor Goes Dark: A Guide to Protecting Your Business – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author The Software as a Service (SaaS) model has revolutionized how businesses operate, offering cost-effective, scalable...
DEF CON 32 – No Symbols When Reversing: No Problem Bring Your Own – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 – No Symbols When Reversing: No Problem Bring Your Own Author/Presenter:...
Certain About Your Data Privacy Measures? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are You Confident in Your Data Privacy Measures? Professionals in financial services in healthcare, travel, DevOps, and SOC teams that...
How Stable is Your Cloud Infrastructure Security? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are Your Machine Identities Protected Within Your Cloud Infrastructure? Let’s delve into a thought-provoking question: Within your seemingly secure systems,...
Independent Audit for Your Secrets Management? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why Should Organizations Focus on Independent Audit for Secrets Management? Are you overlooking an essential aspect of your organization’s cybersecurity...
Microsoft files lawsuit against LLMjacking gang that bypassed AI safeguards – Source: www.csoonline.com
Source: www.csoonline.com – Author: The civil suit against four members of Storm-2139 underscores an emerging trend that blends stolen LLM credentials and AI jailbreaking to reap...
Amnesty Reveals Cellebrite Zero-Day Android Exploit on Serbian Student Activist – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Amnesty International on Friday released technical details on zero-day vulnerabilities exploited by Cellebrite’s mobile forensic tools to spy on a...
Gabbard Decries Britain’s Reported Demand for Apple to Provide Backdoor Access to Users’ Cloud Data – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Director of National Intelligence Tulsi Gabbard says she has serious concerns about the British government’s reported demand that Apple provide...
Microsoft Busts Hackers Selling Illegal Azure AI Access – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
US Soldier Intends to Admit Hacking 15 Telecom Carriers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
$1.5B Bybit Hack is Linked to North Korea, FBI Says, in Potentially the Largest Crypto Heist Ever – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Staff Image: Envato/Weedezign_photo The U.S. Federal Bureau of Investigation has confirmed that North Korea was behind the theft of $1.5 billion...
Notorious Malware, Spam Host “Prospero” Moves to Kaspersky Lab – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs One of the most notorious providers of abuse-friendly “bulletproof” web hosting for cybercriminals has started routing its operations through networks run...
DEF CON 32 – Inside Dash Cam Custom Protocols And Discovered 0days – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Friday, February 28, 2025 Home » Security Bloggers Network » DEF CON 32 – Inside Dash Cam Custom Protocols And...
Mozilla’s Data Practices and Privacy Evolution: Recent Developments – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author Mozilla’s Stance on User Data Mozilla has long built its reputation on privacy, positioning Firefox...