Source: grahamcluley.com – Author: Graham Cluley Skip to content In episode 40 of the AI Fix, Graham meets a shape-shifting GOAT, a robot dog gets wet,...
Author: CISO2CISO Editor 2
CISA refutes claims it has been ordered to stop monitoring Russian cyber threats – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley It’s been a confusing few days in the world of American cybersecurity. At the end of last week, it was...
Name That Edge Toon: On the Precipice – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
TikTok’s Teen Data Use Probed by UK Regulators – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
Qilin Cybercrime Ring Claims Credit for Lee Newspaper Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have...
Phishers Wreak ‘Havoc,’ Disguising Attack Inside SharePoint – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
CISA: No Change on Defending Against Russian Cyber Threats – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine The US government’s cybersecurity agency CISA says there is no change to its stance detecting and disrupting Russian APTs ,...
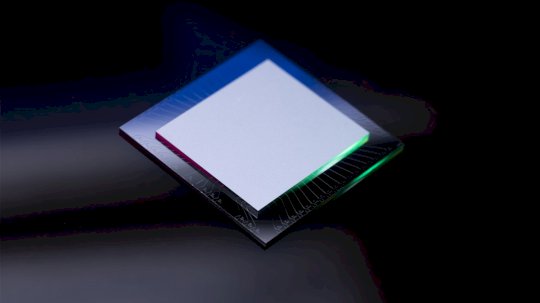
Quantum Wars: Google, Microsoft, and Amazon’s Competing Paths to Fault-Tolerant Qubits – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Following Google’s Willow in December 2024, we now have two additional new quantum chips announced in the final week of...
Mimic Raises $50 Million to Stop Ransomware Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Ransomware defense company Mimic has announced raising $50 million in a Series A funding round that brings the total raised...
US Seizes $31 Million Worth of Crypto Stolen in Uranium Finance Hack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US government last week announced that it has seized roughly $31 million worth of cryptocurrency stolen in April 2021...
Cybersecurity M&A Roundup: 28 Deals Announced in February 2025 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Twenty-eight cybersecurity-related merger and acquisition (M&A) deals were announced in February 2025. An analysis conducted by SecurityWeek shows that 405...
Vulnerable Paragon Driver Exploited in Ransomware Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Ransomware operators have been observed deploying a vulnerable Paragon Hard Disk Manager driver in attacks and exploiting it to elevate...
Indian Stock Broker Angel One Discloses Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Indian stock brokerage firm Angel One on Friday disclosed a data breach impacting client information stored in its Amazon Web...
Manufacturers still poorly prepared for cyberattacks as IT/OT converge – Source: www.csoonline.com
Source: www.csoonline.com – Author: A global survey shows that less than half of manufacturing companies are prepared for the rising onslaught of cyberattacks against them. As...
Bubba AI, Inc. is launching Comp AI to help 100,000 startups get SOC 2 compliant by 2032 – Source: www.csoonline.com
Source: www.csoonline.com – Author: With the growing importance of security compliance for startups, more companies are seeking to achieve and maintain compliance with frameworks like SOC...
SIEM-Kaufratgeber – Source: www.csoonline.com
Source: www.csoonline.com – Author: Security Information and Event Management ist in den meisten Unternehmen Kernbestandteil der IT-Sicherheit. So finden Sie zur richtigen SIEM-Lösung für Ihre Zwecke....
CISOs should address identity management ‘as fast as they can’ says CrowdStrike exec – Source: www.csoonline.com
Source: www.csoonline.com – Author: Threat actors increasingly using stolen credentials to compromise cloud assets, warns the company’s annual threat report. CISOs should be moving “as fast...
US Cybercom, CISA retreat in fight against Russian cyber threats: reports – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 03 Mar 20256 mins CyberattacksGovernment ITRansomware Press reports suggest that US Cybercom is standing down from tracking Russia’s offensive cyber operations,...
Download the AI Risk Management Enterprise Spotlight – Source: us.resources.csoonline.com
Source: us.resources.csoonline.com – Author: Register Download the March 2025 issue of the Enterprise Spotlight from the editors of CIO, Computerworld, CSO, InfoWorld, and Network World. See...
Download the UEM vendor comparison chart, 2025 edition – Source: us.resources.csoonline.com
Source: us.resources.csoonline.com – Author: Home Mobile Device Management Foundry Editorial Register From the editors of Computerworld, this enterprise buyer’s guide helps IT staff understand what the...
Forscher entdecken LLM-Sicherheitsrisiko – Source: www.csoonline.com
Source: www.csoonline.com – Author: Forscher haben Anmeldeinformationen in den Trainingsdaten von Large Language Models entdeckt. BOY ANTHONY – Shutterstock.com Beliebte LLMs wie DeepSeek werden mit Common...
7 Stages of Non-Human Identity Security Maturity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dan Kaplan With no centralized inventory or management system, organizations struggled to answer basic questions like ‘What secrets do we have?’, ‘Who...
Bubba AI, Inc. is launching Comp AI to help 100,000 startups get SOC 2 compliant by 2032. – Source: securityboulevard.com
Source: securityboulevard.com – Author: cybernewswire San Francisco, California, March 3rd, 2025, CyberNewsWire With the growing importance of security compliance for startups, more companies are seeking to...
DEF CON 32 – Differential Privacy Beyond Algorithm: Challenges For Deployment – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 – Differential Privacy Beyond Algorithm: Challenges For Deployment Author/Presenter: Rachel Cummings...
What Is Credential Management? Best Practices and Examples – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security Strong credentials safeguard your digital resources, but common mistakes like weak passwords, credential reuse, and exposed secrets give attackers an...
What Is Code Scanning? Approaches and Best Practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security Identifying security flaws early in the software development lifecycle (SDLC) prevents vulnerabilities from reaching production, where they become more complex...
6 Effective Secret Scanning Tools – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security Secret scanning tools identify and protect sensitive information that may be exposed within software assets. Developers often embed secrets like...
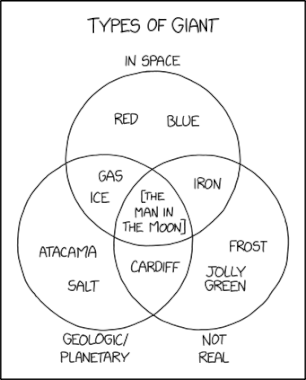
Randall Munroe’s XKCD ‘Giants’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Monday, March 3, 2025 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Security Pros Push Back as Trump Orders Halt to Cyber Ops vs. Russia – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The Trump Administration’s reported move to stop federal agencies from offensive cyber operations and investigations against Russia drew sharp rebuke...
DEF CON 32 – Cybersecurity Schoolhouse Rock – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » DEF CON 32 – Cybersecurity Schoolhouse Rock by Marc Handelman on...