Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...
Author: CISO2CISO Editor 2
Forget the Stack; Focus on Control – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jonathan Meler Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
DoJ Data Security Program Highlights Data Sharing Challenges – Source: www.darkreading.com
Source: www.darkreading.com – Author: Arielle Waldman Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
Reporting lines: Could separating from IT help CISOs? – Source: www.csoonline.com
Source: www.csoonline.com – Author: CISOs who report to the CFO find that the shift away from IT can improve their ability to translate risk into business...
IT-Security ist keine Vertrauenssache – Source: www.csoonline.com
Source: www.csoonline.com – Author: Eine aktuelle Studie warnt davor, IT-Kompetenz mit echter Sicherheitskompetenz zu verwechseln. G Data warnt davor, die Komplexität heutiger Bedrohungsszenarien zu unterschätzen. Pictrider...
Creating Impenetrable Cloud Compliance Practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Mack Are Your Cloud Compliance Practices Truly Impenetrable? Non-Human Identities (NHIs) and Secrets Management have emerged as critical components of an...
Delivering Value with Advanced IAM – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Mack Why is Advanced Identity and Access Management Necessary? Have you ever imagined the chaos that would ensue if all the...
Optimistic About Your Cybersecurity Strategy? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why should Cybersecurity Strategy Spark Optimism? Why is there a growing wave of optimism surrounding cybersecurity strategies, especially with the...
Are You Capable of Managing NHIDs Efficiently? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are You Understanding the Complexities of Managing NHIDs? When it comes to reinforcing cybersecurity, how confident are you in providing...
New geolocus-cli For ONYPHE’s Geolocus Database – Source: securityboulevard.com
Source: securityboulevard.com – Author: hrbrmstr ONYPHE has made available a free API and free MMDB download of their new Geolocus database. It provided IP address metadata...
BSidesLV24 – Ground Truth – Seek Out New Protocols, And Boldly Go Where No One Has Gone Before – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » BSidesLV24 – Ground Truth – Seek Out New Protocols, And Boldly Go Where No...
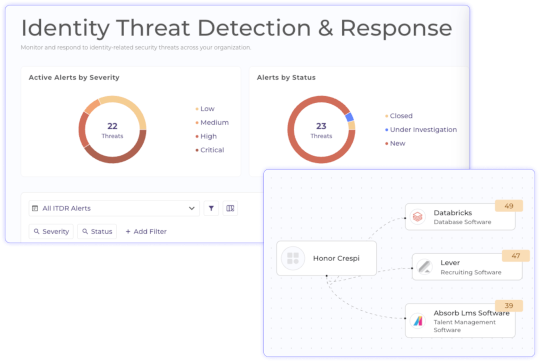
Grip Security Defines the Identity-Driven Future of SecOps – Source: securityboulevard.com
Source: securityboulevard.com – Author: Grip Security Blog Security operations are entering a new era—one where identities, not endpoints, determine risk and response—and Grip is at the...
Identity is the New Perimeter: CybeReady’s Analysis of IBM’s X-Force 2025 Threat Intelligence Index – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mike Polatsek The New Dawn Returns – Horizon Shifts in Cyberattack Trends Following our in-depth analysis of IBM’s 2025 Threat Intelligence Index,...
NSFOCUS APT Monthly Briefing – March 2025 – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS Regional APT Threat Situation Overview In March 2025, the global threat hunting system of NSFOCUS Fuying Laboratory discovered a total of...
GDPR Data Breach Notification Template With Examples [Download] – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amit Kumar The GDPR is a law developed by the European Union (EU) to protect individuals’ personal data. Although it originated in...
Key Cybersecurity Considerations for 2025 – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team As we usher in a new year, it’s crucial to focus on key areas in cybersecurity that demand our attention....
Make the Most of Your Holiday Cybersecurity Awareness Efforts – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team The holiday season is a time for joy, celebration, and, unfortunately, an uptick in cyber threats. From phishing scams that...
MY TAKE: Notes on how GenAI is shifting tension lines in cybersecurity on the eve of RSAC 2025 – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido SAN FRANCISCO — The first rule of reporting is to follow the tension lines—the places where old...
Access Uncoder AI Functionality via API – Source: socprime.com
Source: socprime.com – Author: Steven Edwards How It Works The Uncoder AI API provides access to the platform’s core functionality, enabling integration into your existing CI/CD...
RSAC 2025 Preview: What’s The Buzz To Know Before the Show? – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: With over 41,000 cybersecurity leaders descending on San Francisco, RSAC Conference 2025 promises an epic week for the cybersecurity industry. There’s no...
Proofpoint unveils unified platforms to combat data & cyber risks – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: Proofpoint has introduced two new cybersecurity solutions aimed at unifying threat protection and data security across multiple digital channels and organisational environments....
State-sponsored hackers embrace ClickFix social engineering tactic – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: ClickFix attacks are gaining traction among threat actors, with multiple advanced persistent threat (APT) groups from North Korea, Iran, and Russia adopting...
2025 Cyber Security Predictions: Navigating the Ever-Evolving Threat Landscape – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team As we look ahead to 2025, the world of cyber security is set to undergo significant changes. Attackers are becoming...
Measuring success in dataops, data governance, and data security – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: What metrics do business and tech leaders trust for measuring ROI on dataops, data governance, and data security? We asked the experts....
Not Just Another List of Top 10 Metrics You Should Measure – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team In the world of cybersecurity, we’ve all encountered those articles: lists that tell us the top ten metrics to track to...
In Other News: Prison for Disney Hacker, MITRE ATT&CK v17, Massive DDoS Botnet – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek’s cybersecurity news roundup provides a concise compilation of noteworthy stories that might have slipped under the radar. We provide...
South Korean Companies Targeted by Lazarus via Watering Hole Attacks, Zero-Days – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire At least six South Korean organizations in the financial, IT, semiconductor, software, and telecommunications sectors have been targeted in a...
Secure Your Secrets with Effective Rotation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Mack Why Does Secrets Rotation Matter in Cybersecurity? Secrets rotation, a cybersecurity best practice, is a procedure to refresh and modify...
Feel Supported by Robust PAM – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Can Robust PAM Systems Make a Difference? We delve into the intricacies of Non-Human Identities (NHIs) and Secrets Security Management....
Adapting to Modern Threats in Cloud Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are You Effectively Managing Your Non-Human Identities? For quite a while, organizations have been grappling with numerous cybersecurity challenges. However,...












![gdpr-data-breach-notification-template-with-examples-[download]-–-source:-securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2025/04/169674-gdpr-data-breach-notification-template-with-examples-download-source-securityboulevard-com.jpg)










