Source: www.csoonline.com – Author: Security teams must embrace the principle of least-privilege access to build an effective data control model based on an individual’s role, appropriate...
Author: admin
8 notable entry-level cybersecurity career and skills initiatives in 2023 – Source: www.csoonline.com
Source: www.csoonline.com – Author: Businesses must get better at attracting, supporting, and hiring new cybersecurity talent. Here are eight initiatives launched this year to facilitate entry-level...
Introducing AI-guided Remediation for IaC Security / KICS – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 19, 2023The Hacker NewsDevSecOps / AppSec While the use of Infrastructure as Code (IaC) has gained significant popularity as organizations...
State-Backed Hackers Employ Advanced Methods to Target Middle Eastern and African Governments – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 19, 2023Ravie LakshmananCyber Attack / Hacking Governmental entities in the Middle East and Africa have been at the receiving end...
Microsoft Blames Massive DDoS Attack for Azure, Outlook, and OneDrive Disruptions – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 19, 2023Ravie LakshmananNetwork and Cloud Security Microsoft on Friday attributed a string of service outages aimed at Azure, Outlook, and...
Cybersecurity Insights with Contrast CISO David Lindner | 6/16 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 ” Cyber insurance premiums have skyrocketed (50%) because of ransomware, and there is no end...
From Cryptojacking to DDoS Attacks: Diicot Expands Tactics with Cayosin Botnet – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 17, 2023Ravie LakshmananCryptojacking / Network Security Cybersecurity researchers have discovered previously undocumented payloads associated with a Romanian threat actor named...
Getting Over the DNS Security Awareness Gap – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading As a core backbone of the infrastructure, Domain Name Service (DNS) acts as the phone book...
Killnet Threatens Imminent SWIFT, World Banking Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The pro-Russian hacktivist collective known as Killnet claims to be working in concert with a...
Third MOVEit Transfer Vulnerability Disclosed by Progress Software – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Yet another MOVEit Transfer vulnerability, CVE-2023-35708, was discovered this week by Progress Software, the third that the...
Dodgy Microlending Apps Stalk MEA Users, Highlighting Cyber Maturity Gaps – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Research emerged this week showing that mobile users in the Middle East and Africa are the third...
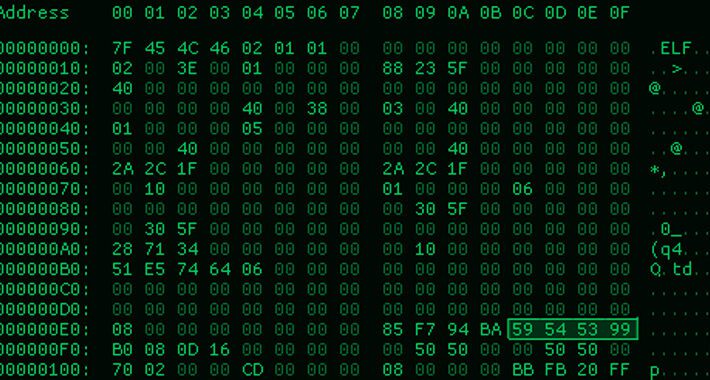
ChamelDoH: New Linux Backdoor Utilizing DNS-over-HTTPS Tunneling for Covert CnC – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 16, 2023Ravie LakshmananEndpoint Security / Network Security The threat actor known as ChamelGang has been observed using a previously undocumented...
Attackers Create Synthetic Security Researchers to Steal IP – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading During the month of May, an unknown threat group created a malicious GitHub repository that claimed...
Cybercrime Doesn’t Take a Vacation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joye Purser, CISSP, Ph.D., Global Lead of Field Cybersecurity, Veritas Technologies Summer is just around the corner, and every cybersecurity professional I...
HashiCorp Expands PAM, Secrets Management Capabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Hashi Corp expanded its identity-based security portfolio with new products for privileged access management and secrets management....
How Do I Protect My API Keys From Appearing in Search Results? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jonathan Care, Contributing Writer, Dark Reading Question: How do I keep my API keys from becoming part of someone else’s GitHub search?...
Microsoft Fixes 69 Bugs, but None Are Zero-Days – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fahmida Y. Rashid, Managing Editor, Features, Dark Reading Microsoft’s Patch Tuesday security update for June 2023 contains patches for 69 vulnerabilities across...
Activities in the Cybercrime Underground Require a New Approach to Cybersecurity – Source:thehackernews.com
Source: thehackernews.com – Author: . As Threat Actors Continuously Adapt their TTPs in Today’s Threat Landscape, So Must You Earlier this year, threat researchers at Cybersixgill...
20-Year-Old Russian LockBit Ransomware Affiliate Arrested in Arizona – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 16, 2023Ravie LakshmananRansomware / Cyber Crime The U.S. Department of Justice (DoJ) on Thursday unveiled charges against a Russian national...
Third Flaw Uncovered in MOVEit Transfer App Amidst Cl0p Ransomware Mass Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 16, 2023Ravie LakshmananCyber Attack / Ransomware Progress Software on Thursday disclosed a third vulnerability impacting its MOVEit Transfer application, as...
Ransomware Hackers and Scammers Utilizing Cloud Mining to Launder Cryptocurrency – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 15, 2023Ravie LakshmananCryptocurrency / Ransomware Ransomware actors and cryptocurrency scammers have joined nation-state actors in abusing cloud mining services to...
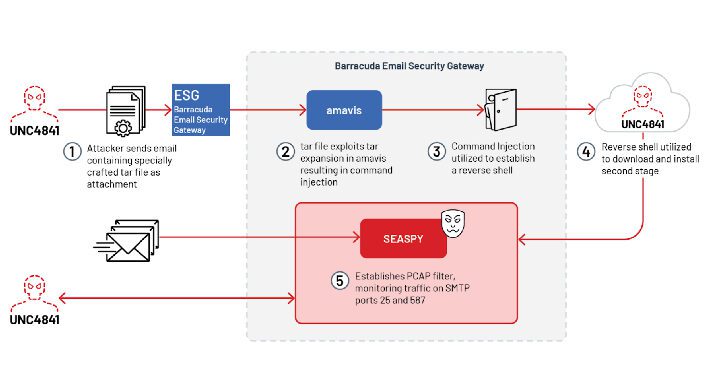
Chinese UNC4841 Group Exploits Zero-Day Flaw in Barracuda Email Security Gateway – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 15, 2023Ravie Lakshmanan A suspected China-nexus threat actor dubbed UNC4841 has been linked to the exploitation of a recently patched...
Vidar Malware Using New Tactics to Evade Detection and Anonymize Activities – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 15, 2023Ravie LakshmananMalware / Cyber Threat The threat actors behind the Vidar malware have made changes to their backend infrastructure,...
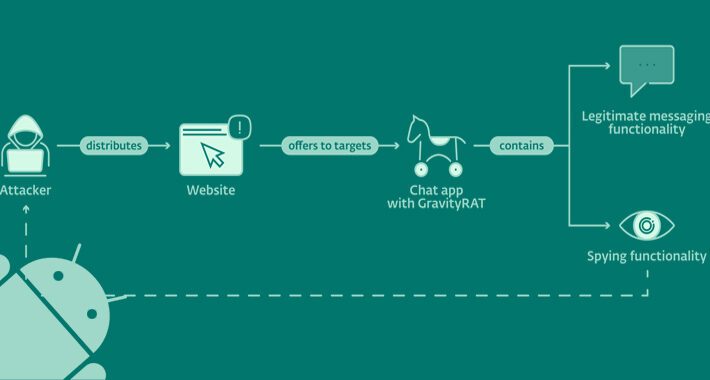
Warning: GravityRAT Android Trojan Steals WhatsApp Backups and Deletes Files – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 15, 2023Ravie LakshmananMobile Security / Privacy An updated version of an Android remote access trojan dubbed GravityRAT has been found...
LockBit Affiliate Arrested, as Extortion Totals Reach $91M Since 2020 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The US Department of Justice has arrested and charged a Russian national, Ruslan Magomedovich Astamirov, for his role...
Critical Barracuda ESG Zero-Day Linked to Novel Chinese APT – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Researchers say the recent compromise of Barracuda Networks email security gateways (ESGs) was carried out by...
Free Training’s Role in Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Curtis Franklin, Senior Analyst, Omdia How far can you go for free? It’s an interesting question if you’re traveling, but it can...
Angola Marks Technology Advancements With Cybersecurity Academy Plans – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Angola President João Lourenço announced plans to open a cybersecurity academy to better secure the nation’s telecommunications...
‘Shampoo’ ChromeLoader Variant Difficult to Wash Out – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Fake websites advertising pirated video games, films, and other wares are spreading a new variant of the...
5 best practices to ensure the security of third-party APIs – Source: www.csoonline.com
Source: www.csoonline.com – Author: The application programming interface (API) has become integral to setting up functionality and flexibility. But they’re also potential attack vectors that need...