Source: www.csoonline.com – Author: Most CISOs have observed improved security culture in their organizations over the last 12 months despite slowing budgets, competing priorities, and insufficient...
Author: admin
New Research: 6% of Employees Paste Sensitive Data into GenAI tools as ChatGPT – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 15, 2023The Hacker NewsBrowser Security / Data Security The revolutionary technology of GenAI tools, such as ChatGPT, has brought significant...
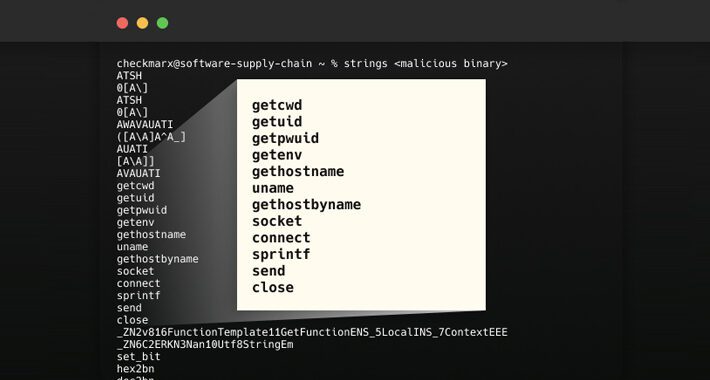
New Supply Chain Attack Exploits Abandoned S3 Buckets to Distribute Malicious Binaries – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 15, 2023Ravie LakshmananSoftware Supply Chain In what’s a new kind of software supply chain attack aimed at open source projects,...
New Report Reveals Shuckworm’s Long-Running Intrusions on Ukrainian Organizations – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 15, 2023Ravie LakshmananCyber War / Threat Intel The Russian threat actor known as Shuckworm has continued its cyber assault spree...
Microsoft Warns of New Russian State-Sponsored Hacker Group with Destructive Intent – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 15, 2023Ravie Lakshmanan Microsoft on Wednesday took the lid off a “novel and distinct Russian threat actor,” which it said...
LockBit Ransomware Extorts $91 Million from U.S. Companies – Source:thehackernews.com
Source: thehackernews.com – Author: . The threat actors behind the LockBit ransomware-as-a-service (RaaS) scheme have extorted $91 million following hundreds of attacks against numerous U.S. organizations...
Network-Security Testing Standard Nears Prime Time – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Despite slow progress, NetSecOpen — a group of network-security companies and hardware testing organizations — aims...
Russian APT ‘Cadet Blizzard’ Behind Ukraine Wiper Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A threat actor that played a key role in the leadup to the Russian invasion of...
Illinois Hospital Closure Showcases Ransomware’s Existential Threat – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading An Illinois hospital’s decision to cease operations later this week at least partly because of a...
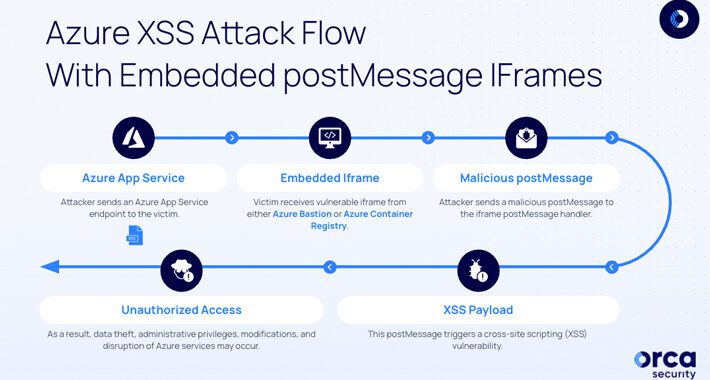
XSS Vulnerabilities Found in Microsoft Azure Cloud Services – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Two cloud security vulnerabilities — in Azure Bastion and Azure Container Registry — were found in Microsoft Azure’s...
Fortinet: Patched Critical Flaw May Have Been Exploited – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers may have exploited a flaw in Fortinet’s FortiOS SSL-VPN in “a limited number of cases” that...
Insights Into Nation-State Tactics: Lessons From Russia’s Hybrid War In Ukraine – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft As the war in Ukraine extends into its second year, Russian threat actors have expanded the scope of their...
How Popular Messaging Tools Instill a False Sense of Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tobias Pischl, Head of Product, Information, and Email Security, Symantec Enterprise Division, Broadcom Today, an increasing number of large enterprises, from financial...
BrandPost: Microsoft special report: Iran’s adoption of cyber-enabled influence operations – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | When you have comprehensive security, the future is yours to build. Learn about the strategies and solutions to secure your...
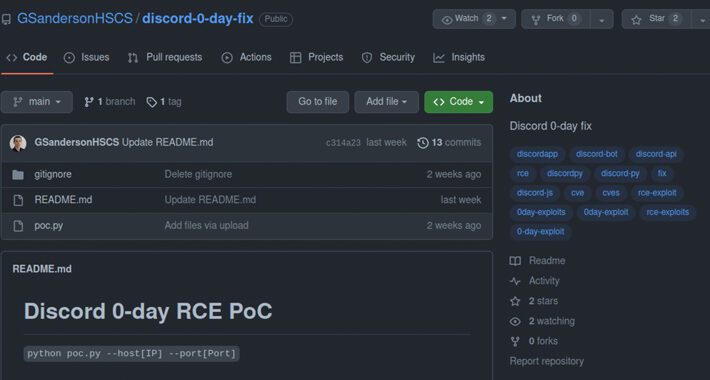
Attackers set up rogue GitHub repos with malware posing as zero-day exploits – Source: www.csoonline.com
Source: www.csoonline.com – Author: The threat actor created fake personas on Twitter for researchers at a non-existent security firm. In an unusual attack campaign, a hacker...
Microsoft Office 365 AitM phishing reveals signs of much larger BEC campaign – Source: www.csoonline.com
Source: www.csoonline.com – Author: This newly discovered, global campaign indicates growing popularity for multi-stage adversary-in-the-middle tactics among threat actors.
Rezilion releases agentless runtime software vulnerability management solution – Source: www.csoonline.com
Source: www.csoonline.com – Author: Software supply chain security vendor claims to have discovered that true, non-agent-based runtime vulnerability analysis is possible by harnessing cloud APIs. Roman...
Cyber liability insurance vs. data breach insurance: What’s the difference? – Source: www.csoonline.com
Source: www.csoonline.com – Author: Cyber insurance is increasingly becoming a compulsory element in business relationships. Knowing what coverage meets a company’s specific needs can provide better...
Chinese Hackers Exploit VMware Zero-Day to Backdoor Windows and Linux Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 14, 2023Ravie LakshmananZero-Day / Network Security The Chinese state-sponsored group known as UNC3886 has been found to exploit a zero-day...
Severe Vulnerabilities Reported in Microsoft Azure Bastion and Container Registry – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 14, 2023Ravie LakshmananCloud Security / Vulnerability Two “dangerous” security vulnerabilities have been disclosed in Microsoft Azure Bastion and Azure Container...
Hiring kit: Cryptographer – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: A cryptographer uses their expertise in mathematics and computer science to develop algorithms, ciphers and other encryption systems to protect sensitive data....
New Golang-based Skuld Malware Stealing Discord and Browser Data from Windows PCs – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 14, 2023Ravie LakshmananCyber Threat / Malware A new Golang-based information stealer called Skuld has compromised Windows systems across Europe, Southeast...
Where from, Where to — The Evolution of Network Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 14, 2023The Hacker NewsThreat Intel / Network Security For the better part of the 90s and early aughts, the sysadmin...
Fake Researcher Profiles Spread Malware through GitHub Repositories as PoC Exploits – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 14, 2023Ravie LakshmananMalware / Zero-Day At least half of dozen GitHub accounts from fake researchers associated with a fraudulent cybersecurity...
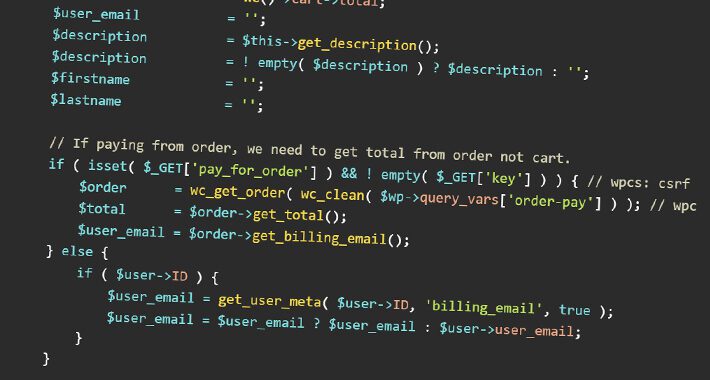
Critical Security Vulnerability Discovered in WooCommerce Stripe Gateway Plugin – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 14, 2023Ravie LakshmananWebsite Security / Hacking A security flaw has been uncovered in the WooCommerce Stripe Gateway WordPress plugin that...
Microsoft Releases Updates to Patch Critical Flaws in Windows and Other Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 14, 2023Ravie LakshmananPatch Tuesday / Vulnerability Microsoft has rolled out fixes for its Windows operating system and other software components...
Analysis: Social Engineering Drives BEC Losses to $50B Globally – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Business email compromise (BEC) continues to evolve on the back of sophisticated targeting and social engineering, costing...
Chinese Threat Actor Abused ESXi Zero-Day to Pilfer Files From Guest VMs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A Chinese cyber-espionage group that researchers previously have spotted targeting VMware ESXi hosts has quietly been...
Popular Apparel, Clothing Brands Being Used in Massive Phishing Scam – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Threat actors have been impersonating more than 100 apparel, clothing, and footwear brands such as Nike, New...
How Security Leaders Should Approach Cybersecurity Startups – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ross Haleliuk , Product Leader and Head of Product, LimaCharlie Security leaders are tired of aggressive sales tactics, and cybersecurity companies must...