Source: thehackernews.com – Author: . Jun 21, 2023Ravie LakshmananNetwork Security / Botnet A new malware called Condi has been observed exploiting a security vulnerability in TP-Link...
Author: admin
Alert! Hackers Exploiting Critical Vulnerability in VMware’s Aria Operations Networks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 21, 2023Ravie LakshmananVulnerability / Network Security VMware has flagged that a recently patched critical command injection vulnerability in Aria Operations...
Why CISOs should be concerned about space-based attacks – Source: www.csoonline.com
Source: www.csoonline.com – Author: Space-based data communications are reliable and useful links for users, but they’re also tempting targets for hackers and other hostile actors. CSOs...
BrandPost: 5 key steps to push back against business email compromise – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | When you have comprehensive security, the future is yours to build. Learn about the strategies and solutions to secure your...
BrandPost: How to secure workloads in the multicloud era – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | Security resilience for the unpredictable to connect and protect every part of your business. Withstand the unforeseen and emerge stronger...
Western Digital blocks unpatched My Cloud devices – Source: www.csoonline.com
Source: www.csoonline.com – Author: My Cloud devices running older firmware have been blocked from accessing Western Digital’s cloud services until they are updated to the latest...
eSentire’s AI Investigator Chatbot Aids Human Response to Security Incidents – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Managed detection and response (MDR) provider eSentire has announced a machine learning-powered tool, eSentire AI Investigator, for...
100K+ Infected Devices Leak ChatGPT Accounts to the Dark Web – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading In the last year, at least 100,000 devices infected by various infostealer malwares have leaked ChatGPT...
Jordanian Cyber Leaders Kick Off Cybersecurity Framework Development – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The National Cybersecurity Center of Jordan has issued a proposed draft for a national cybersecurity framework. With...
Fresh Ransomware Gangs Emerge As Market Leaders Decline – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading There was a rise in the number of ransomware victims in May compared to the previous...
Schneider Power Meter Vulnerability Opens Door to Power Outages – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading INFOSEC23 – London – A security vulnerability in the Schneider Electric ION and PowerLogic power meters...
Mysterious Mystic Stealer Spreads Like Wildfire in Mere Months – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A stealthy stealer that can lift credentials from scores of Web browsers and extensions, and steal cryptocurrency,...
Researchers Expose New Severe Flaws in Wago and Schneider Electric OT Products – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 20, 2023Ravie LakshmananOperational Technology Three security vulnerabilities have been disclosed in operational technology (OT) products from Wago and Schneider Electric....
Zyxel Releases Urgent Security Updates for Critical Vulnerability in NAS Devices – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 20, 2023Ravie LakshmananVulnerability / Data Security Zyxel has rolled out security updates to address a critical security flaw in its...
Security budget hikes are missing the mark, CISOs say – Source: www.csoonline.com
Source: www.csoonline.com – Author: Knee-jerk security budget reactions and impractical expectations are hampering the ability of CISOs to make business-critical security investments. wutzkohphoto / Shutterstock Misguided...
Why assessing third parties for security risk is still an unsolved problem – Source: www.csoonline.com
Source: www.csoonline.com – Author: A recent ranking of the most cyber-secure companies reveals weaknesses in current third-party risk management practices. By Andy Ellis Advisory CISO, Orca...
Romanian cybercrime gang Diicot builds DDoS botnet with Mirai variant – Source: www.csoonline.com
Source: www.csoonline.com – Author: The main focus of Diicot’s attacks appears to support cryptojacking efforts but the group is also employing botnets and brute-force tactics for...
Trend Micro adds generative AI to Vision One for enhanced XDR – Source: www.csoonline.com
Source: www.csoonline.com – Author: New generative artificial intelligence tool Companion is designed to amplify security operations, improve accessibility and efficiency, and quicken threat hunting speeds for...
Team Cymru launches threat-hunting tool aims to fast-forward analysis – Source: www.csoonline.com
Source: www.csoonline.com – Author: The new scouting tool for threat hunting and malicious infrastructure analysis promises to level up users’ security operation centers. By Samira Sarraf...
US feds stress urgent MOVEit platform patching after attacks hit agencies – Source: www.csoonline.com
Source: www.csoonline.com – Author: The Clop ransomware gang has hit at least three US government agencies by exploiting MOVEit file transfer flaws. The State Department offered...
SaaS in the Real World: How Global Food Chains Can Secure Their Digital Dish – Source:thehackernews.com
Source: thehackernews.com – Author: . The Quick Serve Restaurant (QSR) industry is built on consistency and shared resources. National chains like McDonald’s and regional ones like...
Experts Uncover Year-Long Cyber Attack on IT Firm Utilizing Custom Malware RDStealer – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 20, 2023Ravie Lakshmanan A highly targeted cyber attack against an East Asian IT company involved the deployment of a custom...
ASUS Releases Patches to Fix Critical Security Bugs Impacting Multiple Router Models – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 20, 2023Ravie LakshmananNetwork Security / Vulnerability Taiwanese company ASUS on Monday released firmware updates to address, among other issues, nine...
Over 100,000 Stolen ChatGPT Account Credentials Sold on Dark Web Marketplaces – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 20, 2023Ravie LakshmananEndpoint Security / Password Over 101,100 compromised OpenAI ChatGPT account credentials have found their way on illicit dark...
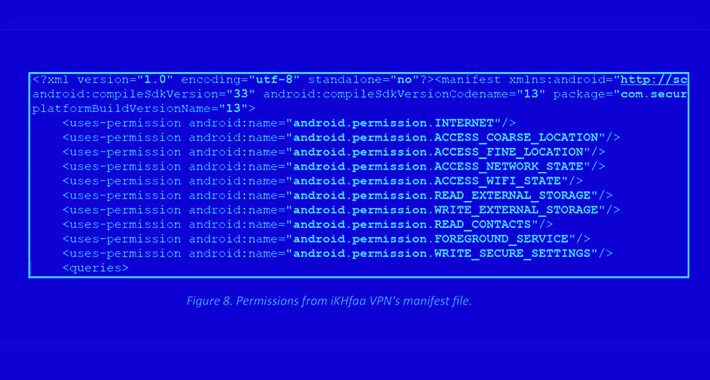
Rogue Android Apps Target Pakistani Individuals in Sophisticated Espionage Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 20, 2023Ravie LakshmananCyber Espionage / Mobile Security Individuals in the Pakistan region have been targeted using two rogue Android apps...
New Mystic Stealer Malware Targets 40 Web Browsers and 70 Browser Extensions – Source:thehackernews.com
Source: thehackernews.com – Author: . A new information-stealing malware called Mystic Stealer has been found to steal data from about 40 different web browsers and over...
Researchers Discover New Sophisticated Toolkit Targeting Apple macOS Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 19, 2023Ravie LakshmananEndpoint Security / Hacking Cybersecurity researchers have uncovered a set of malicious artifacts that they say is part...
Name That Toon: Time to Spare? – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Have a few minutes to spare? Come up with a clever cybersecurity-related caption for the cartoon above. If it...
US Investors Sniffing Around Blacklisted NSO Group Assets – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading NSO Group is facing a number of existential crises at the moment, and it appears there’s a...
Generative AI Has Its Risks, But the Sky Isn’t Falling – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Generative artificial intelligence (GenAI) and large language models (LLMs) are the disruptive technologies du jour, redefining how enterprises...