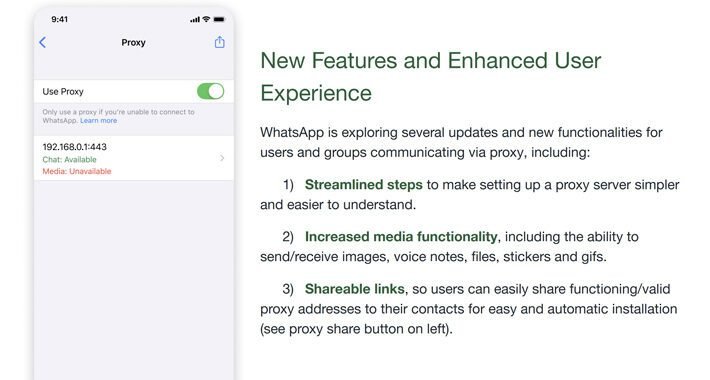
Source: thehackernews.com – Author: . Jun 30, 2023Ravie LakshmananPrivacy / Tech Meta’s WhatsApp has rolled out updates to its proxy feature, allowing more flexibility in the...
Author: admin
Cybercriminals Hijacking Vulnerable SSH Servers in New Proxyjacking Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 30, 2023Ravie LakshmananServer Security / Cyber Threat An active financially motivated campaign is targeting vulnerable SSH servers to covertly ensnare...
MITRE Unveils Top 25 Most Dangerous Software Weaknesses of 2023: Are You at Risk? – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 30, 2023Ravie LakshmananVulnerability / Software Security MITRE has released its annual list of the Top 25 “most dangerous software weaknesses”...
Pepper and Embedded Insurance Partner on Cyber Insurance For Consumers, SMBs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Consumers and small-to-midsize businesses (SMBs) that use Internet of Things (IoT) devices to manage smart homes and businesses...
CISA Wants Exposed Government Devices Remediated In 14 Days – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Researchers have discovered hundreds of devices running on government networks that expose remote management interfaces on...
Apple Objects to UK Bill That Would Break Encrypted Messaging – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Apple has joined more than 80 technology experts and organizations in an appeal to UK lawmakers to...
Researchers Detail 4 SAP Bugs, Including Flaw in ABAP Kernel – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Organizations running business-critical applications on SAP’s Application Server for ABAP platform technology may want to read...
Hiring Kit: IT Audit Director – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Security measures and other IT controls only work if they are implemented consistently, predictably and with integrity. The IT audit director develops...
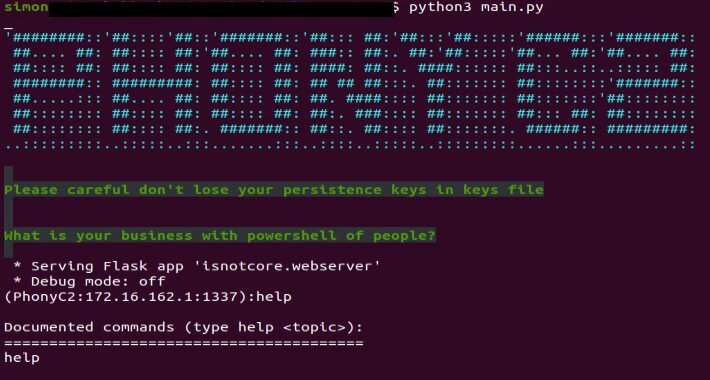
From MuddyC3 to PhonyC2: Iran’s MuddyWater Evolves with a New Cyber Weapon – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 29, 2023Ravie Lakshmanan The Iranian state-sponsored group dubbed MuddyWater has been attributed to a previously unseen command-and-control (C2) framework called...
Fluhorse: Flutter-Based Android Malware Targets Credit Cards and 2FA Codes – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 29, 2023Ravie LakshmananMobile Security / Malware Cybersecurity researchers have shared the inner workings of an Android malware family called Fluhorse....
The Right Way to Enhance CTI with AI (Hint: It’s the Data) – Source:thehackernews.com
Source: thehackernews.com – Author: . Cyber threat intelligence is an effective weapon in the ongoing battle to protect digital assets and infrastructure – especially when combined...
North Korean Hacker Group Andariel Strikes with New EarlyRat Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 29, 2023Ravie LakshmananVulnerability / Malware The North Korea-aligned threat actor known as Andariel leveraged a previously undocumented malware called EarlyRat...
Android Spy App LetMeSpy Suffers Major Data Breach, Exposing Users’ Personal Data – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 29, 2023Ravie LakshmananMobile Security / Privacy Android-based phone monitoring app LetMeSpy has disclosed a security breach that allowed an unauthorized...
Critical Security Flaw in Social Login Plugin for WordPress Exposes Users’ Accounts – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 29, 2023Ravie LakshmananWebsite Security / Vulnerability A critical security flaw has been disclosed in miniOrange’s Social Login and Register plugin...
Newly Uncovered ThirdEye Windows-Based Malware Steals Sensitive Data – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 29, 2023Ravie LakshmananCyber Threat / Hacking A previously undocumented Windows-based information stealer called ThirdEye has been discovered in the wild...
Russian Spies, War Ministers Reliant on Cybercrime in Pariah State – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Russia’s diminishing position on the world stage has limited its physical options on the ground both for...
6 Ways Cybersecurity Is Gut-Checking the ChatGPT Frenzy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Keep up with the latest cybersecurity threats, newly-discovered vulnerabilities, data breach information, and emerging trends....
NPM Plagued With ‘Manifest Confusion’ Malware-Hiding Weakness – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A weakness in Node Package Manager (npm) could allow anybody to hide malicious dependencies and scripts...
LetMeSpy Phone-Tracking App Hacked, Revealing User Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading LetMeSpy, an Android phone-tracking company that has been used to track more than 236,000 phones, was hacked...
Social Engineering Adds Depth to Red Team Exercises – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading When Alethe Denis conducts a social engineering attack as part of a red team exercise, the...
Alert: New Electromagnetic Attacks on Drones Could Let Attackers Take Control – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 28, 2023Ravie LakshmananFirmware Security / Tech Drones that don’t have any known security weaknesses could be the target of electromagnetic...
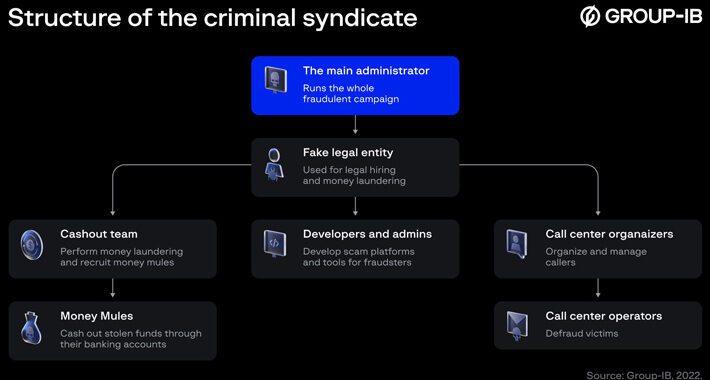
CryptosLabs Scam Ring Targets French-Speaking Investors, Rakes in €480 Million – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 28, 2023Ravie LakshmananCyber Crime / Cryptocurrency Cybersecurity researchers have exposed the workings of a scam ring called CryptosLabs that’s estimated...
The Complete Active Directory Security Handbook – Exploitation – Detection and Migitation Strategies by PICUS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Saudi Arabia’s Cyber Capabilities Ranked Second Globally – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The Kingdom of Saudi Arabia has secured second place in the Global Cybersecurity Index in the World...
Generative AI Projects Pose Major Cybersecurity Risk to Enterprises – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Organizations’ rush to embrace generative AI may be ignoring the significant security threats that large language model...
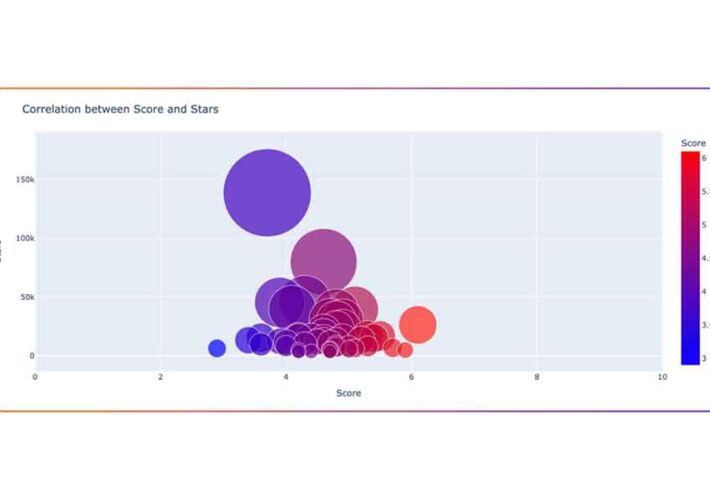
Open Source LLM Projects Likely Insecure, Risky to Use – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading There is a lot of interest in integrating generative AI and other artificial intelligence applications into existing...
Jscrambler Launches JavaScript Scanner for PCI DSS 4.0 Compliance – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Jscrambler has released a free tool to help companies check the JavaScript code running on their e-commerce...
Protecting Small Businesses From Ransomware on a Budget – Source: www.darkreading.com
Source: www.darkreading.com – Author: Sue Poremba, Contributing Writer If your organization is hit with a ransomware attack, it’s going to cost you. According to Verizon’s 2023...
Cequence Security Adds Generative AI to API Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading API security company Cequence Security has updated its API protection platform with generative AI and no-code security automation...
5 Things CISOs Need to Know About Securing OT Environments – Source:thehackernews.com
Source: thehackernews.com – Author: . For too long the cybersecurity world focused exclusively on information technology (IT), leaving operational technology (OT) to fend for itself. Traditionally,...