Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Exploit code will soon become available for a critical vulnerability in the Linux kernel that a...
Author: admin
Patchless Cisco Flaw Breaks Cloud Encryption for ACI Traffic – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Cisco has announced that a high-severity flaw in its data center switching gear could allow threat actors...
Shell Becomes Latest Cl0p MOVEit Victim – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Shell, the multinational oil and gas company, has confirmed that it is the victim of a MOVEit hack, revealing...
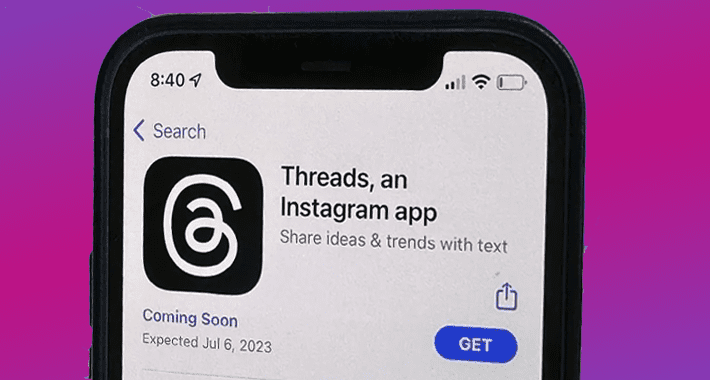
Privacy Woes Hold Up Global Instagram Threads Launch – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A full 20 million people (and counting) had signed up for Meta’s Twitter competitor within...
CISOs Find ‘Business as Usual’ Shows the Harsh Realities of Cyber-Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ryan Kalember, Executive Vice President of Cybersecurity Strategy, Proofpoint With the chaos of the pandemic now in the rearview mirror, we are...
Botnets Send Exploits Within Days to Weeks After Published PoC – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Attackers quickly turn around real-world attacks using proof-of-concept code, taking only days to weeks to create...
6 Steps To Outsmart Business Email Compromise Scammers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Last year the FBI registered over 21,000 complaints about business email fraud, with adjusted losses of over $2.7 billion. Today...
Surviving the 800 Gbps Storm: Gain Insights from Gcore’s 2023 DDoS Attack Statistics – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023The Hacker News Gcore Radar is a quarterly report prepared by Gcore that provides insights into the current state...
Researchers Uncover New Linux Kernel ‘StackRot’ Privilege Escalation Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023Ravie LakshmananLinux / Endpoint Security Details have emerged about a newly identified security flaw in the Linux kernel that...
How Pen Testing can Soften the Blow on Rising Costs of Cyber Insurance – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023The Hacker NewsPenetration Testing / VAPT As technology advances and organizations become more reliant on data, the risks associated...
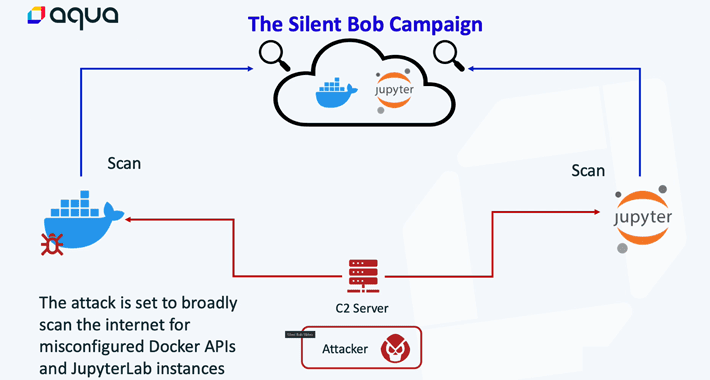
Silentbob Campaign: Cloud-Native Environments Under Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023Ravie LakshmananCloud Security / Server Hacking Cybersecurity researchers have unearthed an attack infrastructure that’s being used as part of...
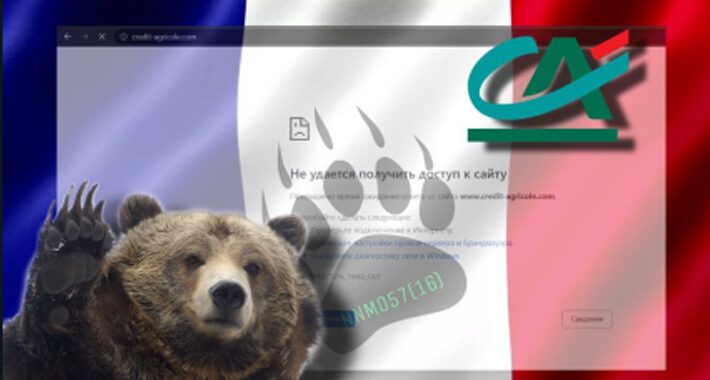
INTERPOL Nabs Hacking Crew OPERA1ER’s Leader Behind $11 Million Cybercrime – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023Ravie LakshmananCyber Crime / Hacking A suspected senior member of a French-speaking hacking crew known as OPERA1ER has been...
Startup Spotlight: Gomboc.ai Balances Cloud Infrastructure Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor Cloud misconfigurations are a leading cause of breaches that lead to data loss for the enterprise, especially with...
3 Critical RCE Bugs Threaten Industrial Solar Panels, Endangering Grid Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Hundreds of solar power monitoring systems are vulnerable to a trio of critical remote code execution...
Microsoft Teams Exploit Tool Auto-Delivers Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A new tool is available on GitHub that gives attackers a way to leverage a recently...
OPERA1ER Cybercrime Group’s Leader Arrested by Interpol – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The suspected top member of the cybercrime group OPERA1ER has been arrested for playing a part in...
Ransomware Halts Operations at Japan’s Port of Nagoya – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Cargo containers filled with imports and exports from all over the world have been stuck at the...
Cl0p’s MOVEit Campaign Represents a New Era in Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading The MOVEit file transfer zero-day vulnerability, first discovered on June 1, was used to breach at least...
China’s Mustang Panda Linked to SmugX Attacks on European Governments – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A Chinese threat group has adopted a sneak HTML technique long-used by its counterparts to target European...
RedEnergy Stealer-as-a-Ransomware Threat Targeting Energy and Telecom Sectors – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 05, 2023Ravie LakshmananCritical Infrastructure Security A sophisticated stealer-as-a-ransomware threat dubbed RedEnergy has been spotted in the wild targeting energy utilities,...
Password Management Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: This policy from TechRepublic Premium provides guidelines for the consistent and secure management of passwords for employees and system and service accounts....
Secrets, Secrets Are No Fun. Secrets, Secrets (Stored in Plain Text Files) Hurt Someone – Source:thehackernews.com
Source: thehackernews.com – Author: . Secrets are meant to be hidden or, at the very least, only known to a specific and limited set of individuals...
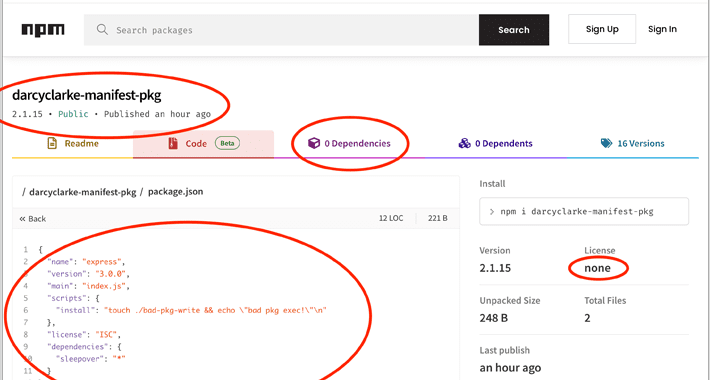
Node.js Users Beware: Manifest Confusion Attack Opens Door to Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 05, 2023Ravie LakshmananSupply Chain / Software Security The npm registry for the Node.js JavaScript runtime environment is susceptible to what’s...
Instagram’s Twitter Alternative ‘Threads’ Launch Halted in Europe Over Privacy Concerns – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 05, 2023Ravie LakshmananPrivacy / Social Media Instagram Threads, the upcoming Twitter competitor from Meta, will not be launched in the...
Swedish Data Protection Authority Warns Companies Against Google Analytics Use – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 04, 2023Ravie LakshmananPrivacy / Online Security The Swedish data protection watchdog has warned companies against using Google Analytics due to...
Verifiable Credentials: Revolutionizing Digital Identity Verification – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author The digital age has transformed numerous aspects of everyday life, from shopping and banking to...
Information Security Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: This policy from TechRepublic Premium provides guidelines to safeguard company information, reduce business and legal risks and protect company investments and reputation....
The State of Security 2023 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cyberattacks continue to grow in quantity and sophistication at the same time that organizations’ systems become increasingly complex. Security teams, as always,...
Fortanix Builds Hardware Security Wall Around Plaintext Search – Source: www.darkreading.com
Source: www.darkreading.com – Author: Agam Shah, Contributing Writer Fortanix is bringing hardware security technology to database search with Confidential Data Search, with the goal to help...
DDoSia Attack Tool Evolves with Encryption, Targeting Multiple Sectors – Source:thehackernews.com
Source: thehackernews.com – Author: . The threat actors behind the DDoSia attack tool have come up with a new version that incorporates a new mechanism to...