Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The Iran-linked advanced persistent threat (APT) known as APT35 (aka Charming Kitten, TA453, and Tortoiseshell) has developed specially crafted...
Author: admin
Deepfake Quantum AI Investment Scam Pops Up on Facebook – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Martin Lewis, a financial journalist and broadcaster, was recently seen promoting an investment scam on Facebook —...
What Are Mobile VPN Apps and Why You Should Be Using Them – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: When you think of VPNs, chances are pretty good your thoughts go to the tried and true virtual private networks of old,...
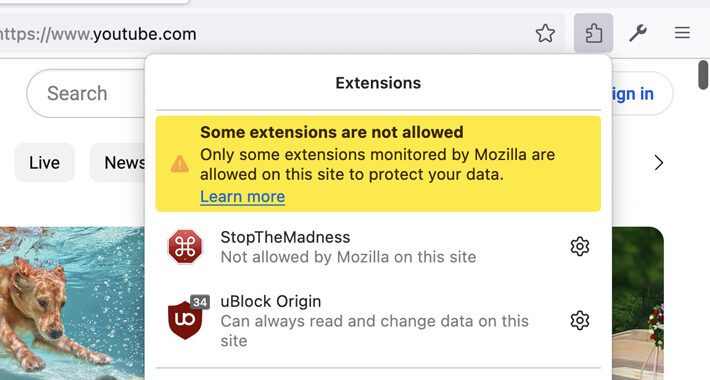
New Mozilla Feature Blocks Risky Add-Ons on Specific Websites to Safeguard User Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 10, 2023THNBrowser Security Mozilla has announced that some add-ons may be blocked from running on certain sites as part of...
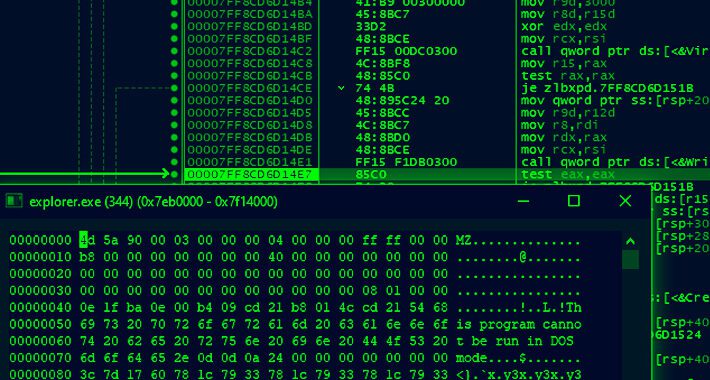
New TOITOIN Banking Trojan Targeting Latin American Businesses – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 10, 2023THNEnterprise Security / Malware Businesses operating in the Latin American (LATAM) region are the target of a new Windows-based...
Global Retailers Must Keep an Eye on Their SaaS Stack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 10, 2023The Hacker NewsSaaS Security Brick-and-mortar retailers and e-commerce sellers may be locked in a fierce battle for market share,...
RomCom RAT Targeting NATO and Ukraine Support Groups – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 10, 2023THNCyber Threat / Malware The threat actors behind the RomCom RAT have been suspected of phishing attacks targeting the...
Hackers Steal $20 Million by Exploiting Flaw in Revolut’s Payment Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Malicious actors exploited an unknown flaw in Revolut’s payment systems to steal more than $20 million of the company’s funds in...
Navigating the Digital Landscape: A Guide for Young People on Managing Their Online Identities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author As the digital world continues to flourish, it is becoming increasingly crucial for young people...
Employee Spotlight – Joseph Pike – Source: securityboulevard.com
Source: securityboulevard.com – Author: Janice Sheridan We spoke to Security Analyst, Joseph Pike For this month’s employee spotlight piece, we spoke to Security Analyst and heavy...
Enhancing Financial Sector Security: IBM Cloud Security & Compliance Center and CyberSaint Collaborate to Streamline 3rd and 4th Party Risk Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Vivek Kinra and Jerry Layden We are thrilled to announce a strategic integration between IBM Cloud Security & Compliance Center and CyberSaint,...
Third-party risk management survey: Prioritize end-to-end software supply chain security — or fail – Source: securityboulevard.com
Source: securityboulevard.com – Author: John P. Mello Jr. Awareness of the risks posed by third-party vendors is high among organizations across industries, but visibility into those...
Banking Firms Under Attack by Sophisticated ‘Toitoin’ Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A sophisticated and evasive malware campaign is targeting businesses in Latin America with a multi-stage attack that...
Cloud Chronicles: Unlocking the Secrets of Solvo – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dishant Patel Unlocking the Potential: For organizations leveraging cloud services to facilitate business growth, it is vital to have a comprehensive and...
MalCare Releases Plugin Update with Improved Authentication Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Editorial Team Recently, a vulnerability in the MalCare plugin was disclosed to our team by a security researcher. We responded to the...
Two Spyware Apps on Google Play with 1.5 Million Users Sending Data to China – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 08, 2023Swati KhandelwalMobile Security / Spyware Two file management apps on the Google Play Store have been discovered to be...
How to Safely Architect AI in Your Cybersecurity Programs – Source: www.darkreading.com
Source: www.darkreading.com – Author: David Randleman, Field CISO — Application Security & Pentest, Coalfire At the end of June, cybersecurity firm Group-IB revealed a notable security...
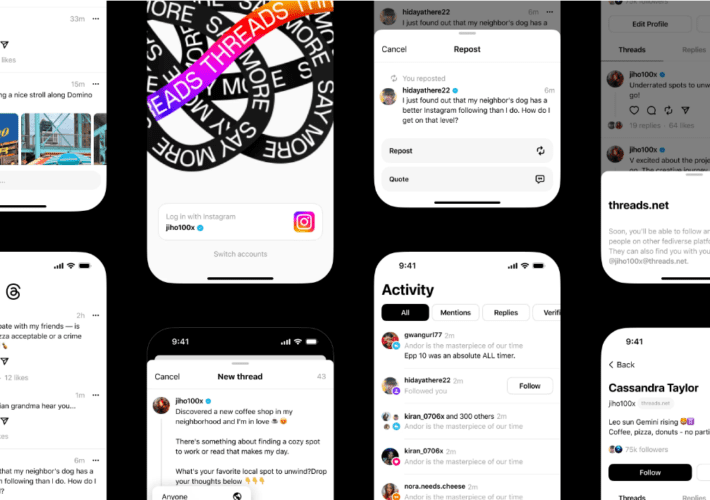
Meta’s Rush to Topple Twitter Sets Up Looming Privacy Debate – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Upcoming data privacy regulations are preventing Meta’s new microblogging app “Threads” from launching in European Union...
Truebot Malware Variants Abound, According to CISA Advisory – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading An advisory from the Cybersecurity and Infrastructure Security Agency (CISA), several US organizations, and the Canadian Center...
Spyware Gamed 1.5M Users of Google Play Store – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Two separate malicious apps loaded with spyware were found lurking in the Google Play store, loaded with...
MOVEit Transfer Faces Another Critical Data-Theft Bug – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Yet another critical SQL injection vulnerability has been disclosed and patched in Progress Software’s MOVEit Transfer software...
Vishing Goes High-Tech: New ‘Letscall’ Malware Employs Voice Traffic Routing – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 07, 2023Swati KhandelwalMobile Security / Malware Researchers have issued a warning about an emerging and advanced form of voice phishing...
Another Critical Unauthenticated SQLi Flaw Discovered in MOVEit Transfer Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 07, 2023Swati KhandelwalVulnerability / Cyber Threat Progress Software has announced the discovery and patching of a critical SQL injection vulnerability...
Mastodon Social Network Patches Critical Flaws Allowing Server Takeover – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 07, 2023Swati KhandelwalVulnerability / Social Media Mastodon, a popular decentralized social network, has released a security update to fix critical...
Startup Spotlight: Endor Labs Focuses on Reachability – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor As the Log4j vulnerability demonstrated in a visceral way, open source code is inextricable from modern software. Developers...
BlackByte 2.0 Ransomware: Infiltrate, Encrypt, and Extort in Just 5 Days – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 07, 2023Swati KhandelwalEndpoint Security / Ransomware Ransomware attacks are a major problem for organizations everywhere, and the severity of this...
Google Releases Android Patch Update for 3 Actively Exploited Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 07, 2023Swati KhandelwalZero-Day Vulnerability Google has released its monthly security updates for the Android operating system, addressing 46 new software...
JumpCloud Resets API Keys Amid Ongoing Cybersecurity Incident – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 07, 2023Swati KhandelwalSecurity Incident / API Security JumpCloud, a provider of cloud-based identity and access management solutions, has swiftly reacted...
Cybersecurity Agencies Sound Alarm on Rising TrueBot Malware Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 07, 2023Swati KhandelwalCyber Attack / Malware Cybersecurity agencies have warned about the emergence of new variants of the TrueBot malware....
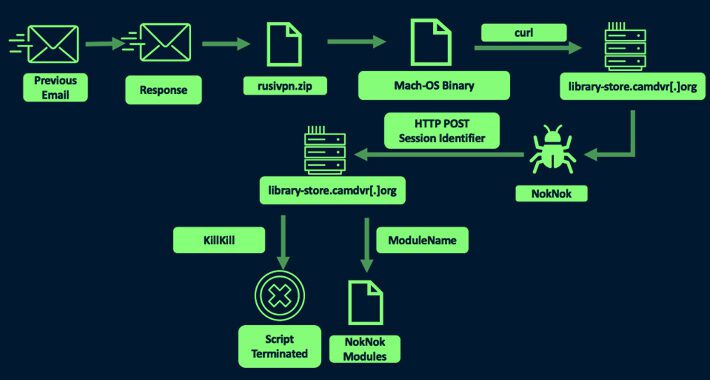
Iranian Hackers’ Sophisticated Malware Targets Windows and macOS Users – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 06, 2023Ravie LakshmananEndpoint Security / Malware The Iranian nation-state actor known as TA453 has been linked to a new set...