Source: securityboulevard.com – Author: Ahona Rudra Email addressed can be compromised to initiate major data breaches that can lead to the loss of your assets and...
Author: admin
What we told the CFTC about crypto threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Trail of Bits Dan Guido, CEO In March, I joined the Commodity Futures Trading Commission’s Technology Advisory Committee (TAC), helping the regulatory...
CycloneDX 1.5: The next big step for SBOMs and software transparency – Source: securityboulevard.com
Source: securityboulevard.com – Author: John P. Mello Jr. CycloneDX is one of the most popular standards for describing the components of an application, including source code,...
The Risks and Preventions of AI in Business: Safeguarding Against Potential Pitfalls – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023The Hacker NewsDNS Filtering / Network Security Artificial intelligence (AI) holds immense potential for optimizing internal processes within businesses....
Microsoft Thwarts Chinese Cyber Attack Targeting Western European Governments – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023THNThreat Intel / Cyber Espionage Microsoft on Tuesday revealed that it repelled a cyber attack staged by a Chinese...
Chinese Hackers Deploy Microsoft-Signed Rootkit to Target Gaming Sector – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023THNCyber Threat / Gaming Cybersecurity researchers have unearthed a novel rootkit signed by Microsoft that’s engineered to communicate with...
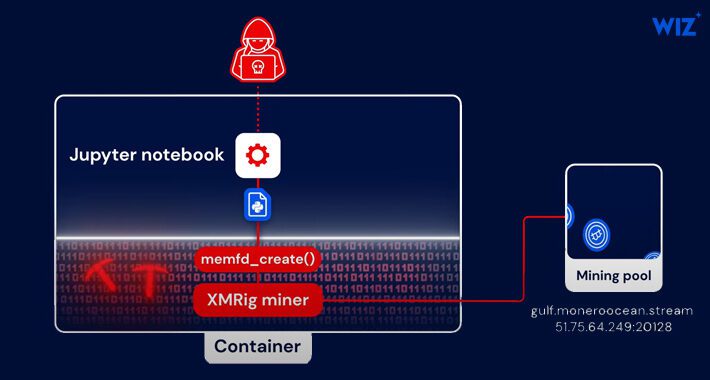
Python-Based PyLoose Fileless Attack Targets Cloud Workloads for Cryptocurrency Mining – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023The Hacker NewsCloud Security / Cryptocurrency A new fileless attack dubbed PyLoose has been observed striking cloud workloads with...
Microsoft Releases Patches for 132 Vulnerabilities, Including 6 Under Active Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023The Hacker NewsVulnerability / Software Security Microsoft on Tuesday released updates to address a total of 132 new security...
Microsoft Discloses 5 Zero-Days in Voluminous July Security Update – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Microsoft’s July security update contains fixes for a whopping 130 unique vulnerabilities, five of which attackers...
Mastodon Patches 4 Bugs, but Is the Twitter Killer Safe to Use? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Four vulnerabilities in the microblogging platform Mastodon were patched late last week, sparking new questions about...
11M HCA Healthcare Patients Impacted by Data Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading HCA Healthcare, operator of a massive hospital and healthcare services network in the US and UK that...
Microsoft Expands Entra Into Secure Service Edge – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor In response to an expanding threat landscape, Microsoft today released a new set of products that expands its...
Bangladesh Government Website Leaks Personal Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The personal details of Bangladeshi citizens have been accidentally disclosed by the website of the Office of...
Cyberattacks Are a War We’ll Never Win, but We Can Defend Ourselves – Source: www.darkreading.com
Source: www.darkreading.com – Author: Steve Preston, Vice President, Metallic Security Services, Commvault Dish Network. Uber. The data networks of several major US airports. These are only...
Apple’s Rapid Zero-Day Patch Causes Safari Issues, Users Say – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Less than 24 hours after issuing an urgent fix for a zero-day security vulnerability under...
Hiring Kit: Security Analyst – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: In general, security analysts are tasked with identifying weaknesses in current security systems and developing solutions to close security vulnerabilities. To perform...
Hackers Exploit Windows Policy Loophole to Forge Kernel-Mode Driver Signatures – Source:thehackernews.com
Source: thehackernews.com – Author: . A Microsoft Windows policy loophole has been observed being exploited primarily by native Chinese-speaking threat actors to forge signatures on kernel-mode...
In the News | Why cybersecurity is a priority this summer for these K12 schools – Source: securityboulevard.com
Source: securityboulevard.com – Author: Katie Fritchen This article was originally published in District Administration on 6.28.23 by Micah Ward, Staff Writer at District Administration After a...
Why Hosting by Country Makes Sense – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Williams A Little Privacy, Please? There are voluminous discussions around General Data Protection Regulation (GDPR) in the European Union and the...
The Impact of Culture & Morale on Security ROI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Katie Bykowski The Security Operations Center (SOC) plays a critical role in protecting an organization’s assets, data and reputation from cyber threats....
AI’s Impact on Security, Risk and Governance in a Hybrid Cloud World – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kaus Phaltankar AI is a transformative technology that is reshaping the landscape of security, risk management, compliance and governance in hybrid cloud...
How to Apply MITRE ATT&CK to Your Organization – Source:thehackernews.com
Source: thehackernews.com – Author: . Discover all the ways MITRE ATT&CK can help you defend your organization. Build your security strategy and policies by making the...
SCARLETEEL Cryptojacking Campaign Exploiting AWS Fargate in Ongoing Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 11, 2023THNCryptocurrency / Cloud Security Cloud environments continue to be at the receiving end of an ongoing advanced attack campaign...
Beware of Big Head Ransomware: Spreading Through Fake Windows Updates – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 11, 2023THNRansomware / Windows Security A developing piece of ransomware called Big Head is being distributed as part of a...
Apple Issues Urgent Patch for Zero-Day Flaw Targeting iOS, iPadOS, macOS, and Safari – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 11, 2023THNZero-Day / Endpoint Security Apple has released Rapid Security Response updates for iOS, iPadOS, macOS, and Safari web browser...
‘ScarletEel’ Hackers Worm Into AWS Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Researchers have observed the financially motivated threat actor ScarletEel infiltrating Amazon Web Services (AWS) to steal...
Analysts: Cybersecurity Funding Set for Rebound – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading In line with prior expectations, financing deals, and mergers and acquisition (M&A) activity in the cybersecurity...
NIST Launches Generative AI Working Group – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Even as security companies continue releasing products and features that leverage advanced artificial intelligence (AI), researchers continue...
Amazon Prime Day Draws Out Cyber Scammers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Amazon Prime Day runs from July 11-12, but scammers have already started to capitalize on the worldwide...
10 Features an API Security Service Needs to Offer – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joshua Goldfarb, Security and Fraud Architect, F5 Application programming interfaces (APIs) are a powerful technology that allow businesses to innovate faster and...