Source: securityboulevard.com – Author: Sarah Hunter-Lascoskie In 2022, the FBI received 800,944 reported complaints that exceeded $10.3 billion in fraud losses for businesses’ critical infrastructure and...
Author: admin
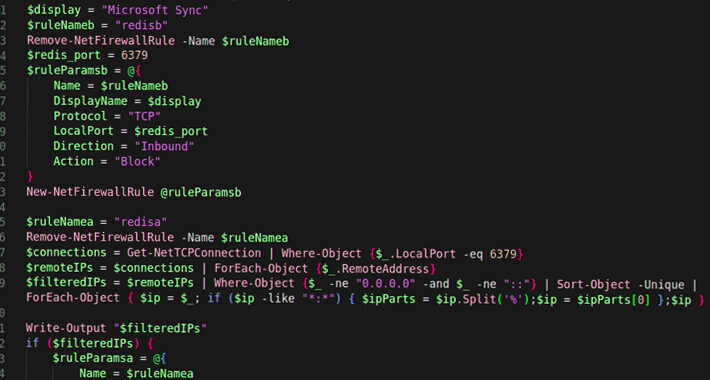
New P2P Worm Puts Windows and Linux Redis Servers in its Sights – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt A new peer-to-peer (P2P) worm is spreading across instances of the Redis open source database software in the cloud. It...
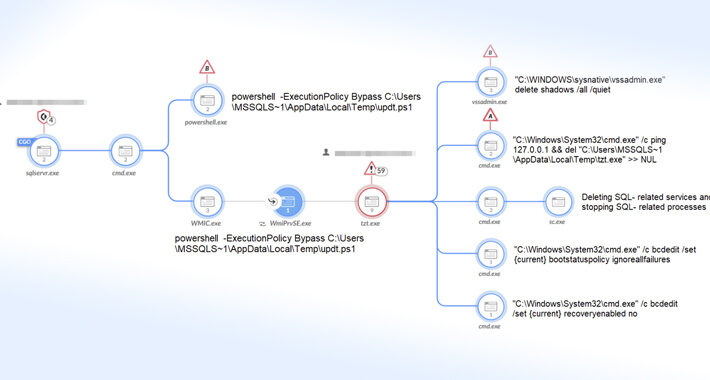
Mallox Ransomware Exploits Weak MS-SQL Servers to Breach Networks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 20, 2023THNEndpoint Security / Data Safety Mallox ransomware activities in 2023 have witnessed a 174% increase when compared to the...
Critical Flaws in AMI MegaRAC BMC Software Expose Servers to Remote Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 20, 2023THNHardware Security / SysAdmin Two more security flaws have been disclosed in AMI MegaRAC Baseboard Management Controller (BMC) software...
Apache OpenMeetings Web Conferencing Tool Exposed to Critical Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 20, 2023THNVulnerability / Software Security Multiple security flaws have been disclosed in Apache OpenMeetings, a web conferencing solution, that could...
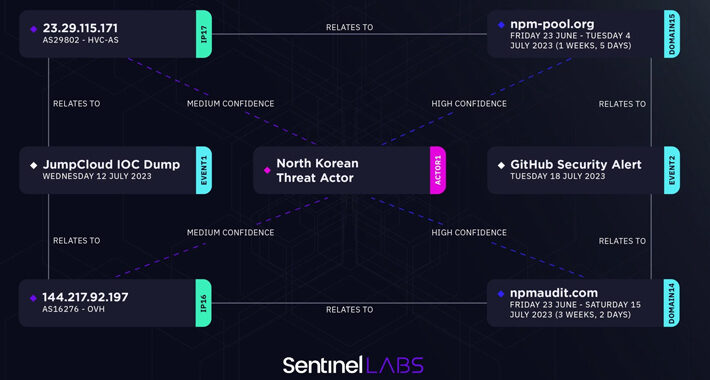
North Korean State-Sponsored Hackers Suspected in JumpCloud Supply Chain Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 20, 2023THNCyber Attack / Supply Chain An analysis of the indicators of compromise (IoCs) associated with the JumpCloud hack has...
A Few More Reasons Why RDP is Insecure (Surprise!) – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 20, 2023The Hacker News If it seems like Remote Desktop Protocol (RDP) has been around forever, it’s because it has...
Enterprise Choices in Measuring Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Curtis Franklin, Senior Analyst, Omdia Risk can be tricky to measure. As in so much of life, the devil is in the...
Attackers Exploit Citrix Zero-Day Bug to Pwn NetScaler ADC, Gateway – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Cyberattackers are actively exploiting a critical remote code execution (RCE) bug in several versions of Citrix’s...
Black Hat Offers Pen-Testing Certification Exam – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Black Hat is partnering with The SecOps Group to launch an independent exam track at next month’s...
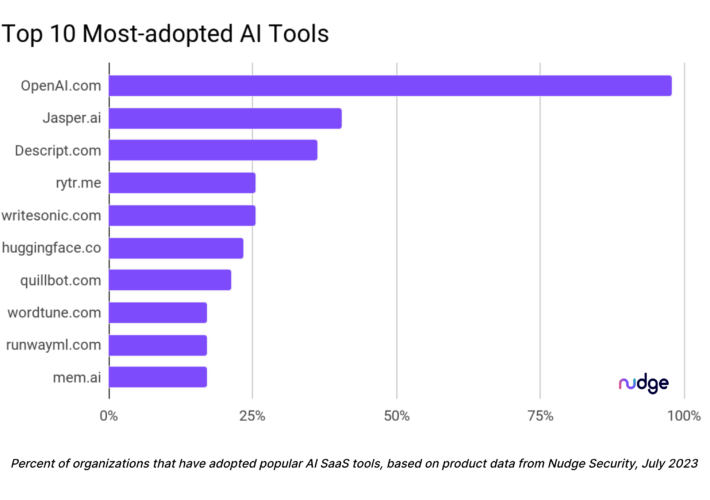
Infosec Doesn’t Know What AI Tools Orgs Are Using – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading With the marketplace awash in new artificial intelligence (AI) tools and sparkling new AI features being added...
Turla’s New DeliveryCheck Backdoor Breaches Ukrainian Defense Sector – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 20, 2023THNCyber Attack / Malware The defense sector in Ukraine and Eastern Europe has been targeted by a novel .NET-based...
New P2PInfect Worm Targeting Redis Servers on Linux and Windows Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 20, 2023THNMalware / Cyber Threat Cybersecurity researchers have uncovered a new cloud targeting, peer-to-peer (P2P) worm called P2PInfect that targets...
Microsoft Expands Cloud Logging to Counter Rising Nation-State Cyber Threats – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 20, 2023THNCloud Security / Cyber Espionage Microsoft on Wednesday announced that it’s expanding cloud logging capabilities to help organizations investigate...
Adobe Rolls Out New Patches for Actively Exploited ColdFusion Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 20, 2023THNSoftware Security / Vulnerability Adobe has released a fresh round of updates to address an incomplete fix for a...
Attacker ID’ed After Infecting Own Computer With Malware – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt A threat actor that goes by the name of “La_Citrix” had a reputation for hacking into companies’ computer systems and...
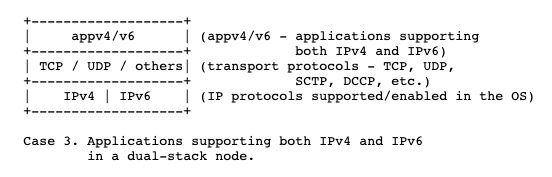
‘::ffff’ only…Tips for identifying unusual network activity – Source: securityboulevard.com
Source: securityboulevard.com – Author: IronNet Threat Research Team Every now and then, a security team uncovers something only the Internet Engineering Task Force (IETF) can fully...
An ‘Alarming Escalation’ of Sophistication in DDoS Attacks, Cloudflare Says – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Distributed denial-of-service (DDoS) attacks are becoming increasingly sophisticated and complex, making what is already an expanding threat landscape even more...
Rockwell Automation ControlLogix Bugs Expose Industrial Systems to Remote Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 13, 2023THNOT/ICS, SCADA Cybersecurity The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has alerted of two security flaws impacting Rockwell...
U.S. Government Agencies’ Emails Compromised in China-Backed Cyber Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 13, 2023THNCyber Espionage / Email Security An unnamed Federal Civilian Executive Branch (FCEB) agency in the U.S. detected anomalous email...
New Vulnerabilities Disclosed in SonicWall and Fortinet Network Security Products – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 13, 2023THNNetwork Security / Vulnerability SonicWall on Wednesday urged customers of Global Management System (GMS) firewall management and Analytics network...
Provide Secure Remote Access for Your Employees with an SSL VPN – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Premium TechRepublic Premium 7 Steps for Onboarding Remote Employees It’s easy to bungle a new employee’s introduction to a company. But...
Secure Business-Critical Resources with a Web Application Firewall – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Premium TechRepublic Premium 7 Steps for Onboarding Remote Employees It’s easy to bungle a new employee’s introduction to a company. But...
Optimize Your Applications & Data Centers with Load Balancing – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Premium TechRepublic Premium 7 Steps for Onboarding Remote Employees It’s easy to bungle a new employee’s introduction to a company. But...
Microsoft Relents, Offers Free Key Logging to All 365 Customers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Microsoft dropped the fees associated with expanded logging access for all levels of 365 license holders, after...
P2P Self-Replicating Cloud Worm Targets Redis – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Researchers have identified a cross-platform, Rust-based, peer-to-peer (P2) worm that’s targeting the Redis open-source database application; specifically, containers in...
China’s APT41 Linked to WyrmSpy, DragonEgg Mobile Spyware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Researchers have attributed two known Android surveillanceware programs — WyrmSpy and DragonEgg — to China’s APT41....
Seed Group Brings Resecurity Options to UAE Region – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The United Arab Emirates-based Seed Group has announced a strategic partnership with American cybersecurity company Resecurity. According...
Reducing Security Debt in the Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: Terence Harper, CISSP, Senior Sales Engineer, Ermetic Debt is a big topic of discussion these days — household debt in inflationary times,...
Leverage Threat Intelligence, AI, and Data at Scale to Boost Cyber Defenses – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft As security tooling grows more sophisticated and insight into cybercriminal activity becomes more comprehensive, our collective ability to detect...