Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor The December discovery of moderate to severe vulnerabilities in the baseboard management controllers (BMCs) used by 15 different...
Author: admin
How AI-Augmented Threat Intelligence Solves Security Shortfalls – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Security-operations and threat-intelligence teams are chronically short-staffed, overwhelmed with data, and dealing with competing demands —...
Microsoft ‘Logging Tax’ Hinders Incident Response, Experts Warn – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading A human rights organization was alerted by Microsoft that it was compromised as part of a July...
How to Manage Your Attack Surface? – Source:thehackernews.com
Source: thehackernews.com – Author: . Attack surfaces are growing faster than security teams can keep up. To stay ahead, you need to know what’s exposed and...
CISA and NSA Issue New Guidance to Strengthen 5G Network Slicing Against Threats – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 19, 2023THNNetwork Security U.S. cybersecurity and intelligence agencies have released a set of recommendations to address security concerns with 5G...
Chinese APT41 Hackers Target Mobile Devices with New WyrmSpy and DragonEgg Spyware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 19, 2023THNSpyware / Mobile Security The prolific China-linked nation-state actor known as APT41 has been linked to two previously undocumented...
Exploring the Dark Side: OSINT Tools and Techniques for Unmasking Dark Web Operations – Source:thehackernews.com
Source: thehackernews.com – Author: . On April 5, 2023, the FBI and Dutch National Police announced the takedown of Genesis Market, one of the largest dark...
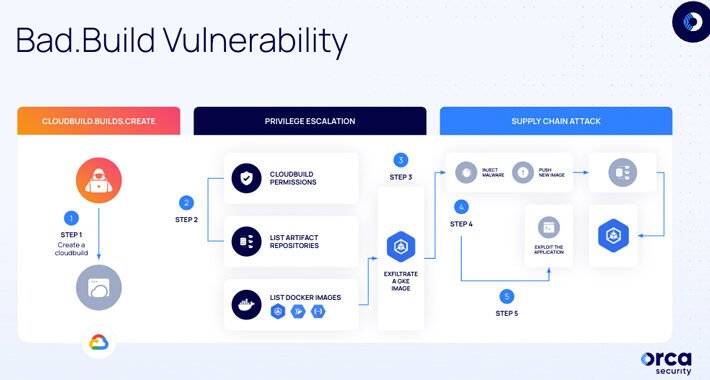
Bad.Build Flaw in Google Cloud Build Raises Concerns of Privilege Escalation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 19, 2023THNCloud Security / Vulnerability Cybersecurity researchers have uncovered a privilege escalation vulnerability in Google Cloud that could enable malicious...
U.S. Government Blacklists Cytrox and Intellexa Spyware Vendors for Cyber Espionage – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 19, 2023THNCyber Espionage / Spyware The U.S. government on Tuesday added two foreign commercial spyware vendors, Cytrox and Intellexa, to...
Zero-Day Attacks Exploited Critical Vulnerability in Citrix ADC and Gateway – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 19, 2023THNVulnerability / Cyber Threat Citrix is alerting users of a critical security flaw in NetScaler Application Delivery Controller (ADC)...
Defend Against Insider Threats: Join this Webinar on SaaS Security Posture Management – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 14, 2023The Hacker NewsSaaS Security / Cybersecurity As security practices continue to evolve, one primary concern persists in the minds...
AIOS WordPress Plugin Faces Backlash for Storing User Passwords in Plaintext – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 14, 2023THNPassword Security / WordPress All-In-One Security (AIOS), a WordPress plugin installed on over one million sites, has issued a...
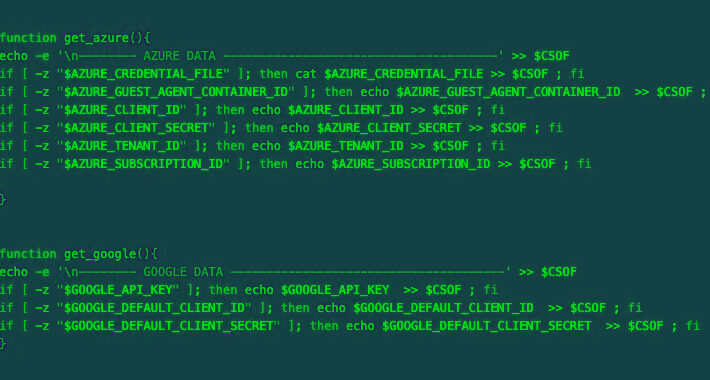
TeamTNT’s Cloud Credential Stealing Campaign Now Targets Azure and Google Cloud – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 14, 2023THNCyber Threat / Cloud Security A malicious actor has been linked to a cloud credential stealing campaign in June...
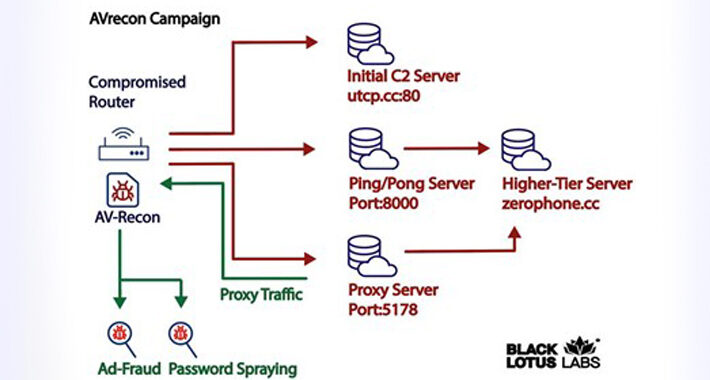
New SOHO Router Botnet AVrecon Spreads to 70,000 Devices Across 20 Countries – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 14, 2023THNNetwork Security / Malware A new malware strain has been found covertly targeting small office/home office (SOHO) routers for...
Zimbra Warns of Critical Zero-Day Flaw in Email Software Amid Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 14, 2023THNEmail Security / Vulnerability Zimbra has warned of a critical zero-day security flaw in its email software that has...
PicassoLoader Malware Used in Ongoing Attacks on Ukraine and Poland – Source:thehackernews.com
Source: thehackernews.com – Author: . Government entities, military organizations, and civilian users in Ukraine and Poland have been targeted as part of a series of campaigns...
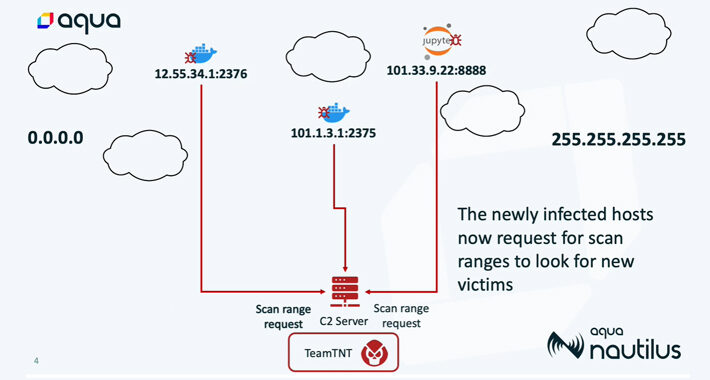
TeamTNT’s Silentbob Botnet Infecting 196 Hosts in Cloud Attack Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 13, 2023THNCloud Security / Cryptocurrency As many as 196 hosts have been infected as part of an aggressive cloud campaign...
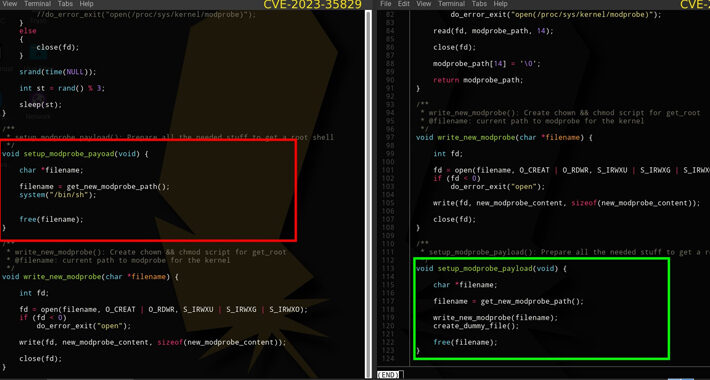
Fake PoC for Linux Kernel Vulnerability on GitHub Exposes Researchers to Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 13, 2023THNLinux / Vulnerability In a sign that cybersecurity researchers continue to be under the radar of malicious actors, a...
HWL Ebsworth hack: Queensland says its files were taken after criminals release Victorian documents – Source: www.theguardian.com
Source: www.theguardian.com – Author: Adeshola Ore and Eden Gillespie Highly sensitive legal documents from the Victorian government have been published on the dark web by cybercriminals,...
Google Cloud Build Flaw Enables Privilege Escalation, Code Tampering – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A newly discovered vulnerability in Google Cloud Build enables attackers to tamper with and inject malware...
Pernicious Rootkits Pose Growing Blight On Threat Landscape – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading In recent weeks, attackers have leveraged workarounds that let them sign malicious kernel drivers, dealing a...
Hacker Infected & Foiled by Own Infostealer – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Malicious actor “La_Citrix” built a reputation on gaining access to organizations’ Citrix remote desktop protocol (RDP) VPN...
Name That Toon: Shark Sighting – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Oh, the shark has pretty teeth, dear … Come up with a clever cybersecurity-related caption for the cartoon above....
FIN8 Modifies ‘Sardonic’ Backdoor to Deliver BlackCat Ransomware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The threat actor FIN8 has resurged after a lull, using a revised version of its Sardonic...
Attackers Pummel Millions of Websites via Critical WooCommerce Payments Flaw – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers have been exploiting a critical flaw in the WordPress WooCommerce Payments plug-in in a spate of...
Microsoft Takes Security Copilot AI Assistant to the Next Level – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading On Tuesday, Microsoft announced it will expand access to its Security Copilot service — an artificial...
Sogu, SnowyDrive Malware Spreads, USB-Based Cyberattacks Surge – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Two ongoing cyber-espionage campaigns targeting organizations across multiple industries and regions demonstrate the importance for security teams...
Linux Ransomware Poses Significant Threat to Critical Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jon Miller, CEO & Co-Founder, Halcyon Linux systems run many of the most critical operations behind the scenes, including a good deal...
How to Check If Someone Else Accessed Your Google Account – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Andy Wolber Illustration: Andy Wolber/TechRepublic Whenever a computer is out of your direct view and control, there’s always a chance that someone...
BlackCat Alphv Ransomware – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Adelina Deaconu The ransomware operation known as BlackCat, also referred to as Alphv ransomware, has been utilized by members of the Alphv...