Source: thehackernews.com – Author: . Jul 22, 2023THNEncryption / Privacy Apple has warned that it would rather stop offering iMessage and FaceTime services in the U.K....
Author: admin
BGP Software Vulnerabilities Under the Microscope in Black Hat Session – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading It’s hard to believe that despite so much manpower, time, and money dedicated to the cybersecurity...
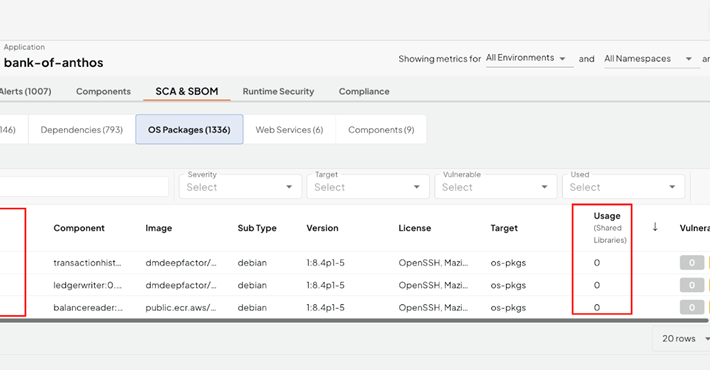
Banks In Attackers’ Crosshairs, Via Open Source Software Supply Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading In two separate incidents, threat actors recently tried to introduce malware into the software development environment...
Rootkit Attack Detections Increase at UAE Businesses – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Detections of attack attempts using rootkits against business targets in the United Arab Emirates (UAE) have significantly...
CVSS 4.0 Is Here, But Prioritizing Patches Still a Hard Problem – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading The soon-to-be-released Version 4.0 of the Common Vulnerability Scoring System (CVSS) promises to fix a number of...
Saudi Arabia’s Tuwaiq Academy Opens Cybersecurity Bootcamp – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Registration for a Cybersecurity Bootcamp has begun at the Tuwaiq Academy in Saudi Arabia. Coming on the...
Microsoft 365 Breach Risk Widens to Millions of Azure AD Apps – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The Storm-0558 breach that gave Chinese advanced persistent threat (APT) actors access to emails within...
White House, Big Tech Ink Commitments to Secure AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Seven leading tech companies — Google, Microsoft, Meta, Amazon, OpenAI, Anthropic, and Inflection — are meeting at...
Meet the Finalists for the 2023 Pwnie Awards – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor With Black Hat USA 2023 looming, it’s time to start thinking about the Oscars of cybersecurity, the Pwnie...
The Dark Side of AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Sam Crowther, Founder & CEO, Kasada New AI tools offer easier and faster ways for people to get their jobs done —...
GitHub Developers Targeted by North Korea’s Lazarus Group – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The notorious Lazarus Group is behind a social engineering campaign that uses repository invitations and malicious npm packages to target...
Cybersecurity Insights with Contrast CISO David Lindner | 7/21 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 WormGPT is a thing. The tool — being sold on hacker forums and considered “ChatGPT’s evil...
Digging Into An Interesting New CVE – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mike Larkin CVE-2023-38408, discovered by the Qualys Threat Research Unit (TRU), describes an RCE (remote code execution) vulnerability made possible by an...
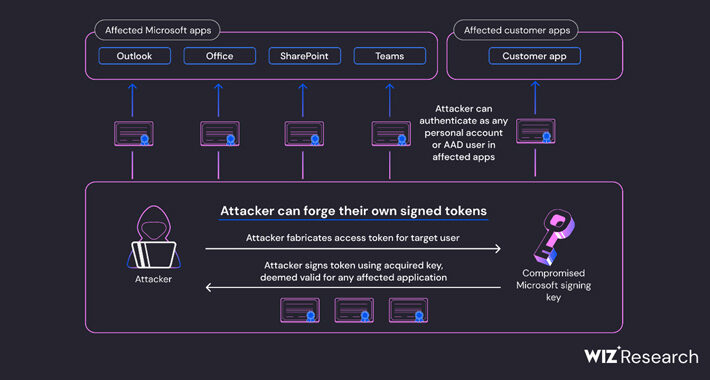
Azure AD Token Forging Technique in Microsoft Attack Extends Beyond Outlook, Wiz Reports – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 21, 2023THNEmail Security / Cyber Attack The recent attack against Microsoft’s email infrastructure by a Chinese nation-state actor referred to...
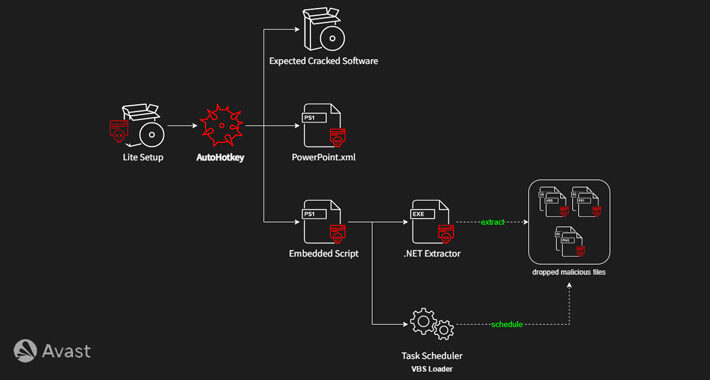
HotRat: New Variant of AsyncRAT Malware Spreading Through Pirated Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 21, 2023THNMalware / Software Security A new variant of AsyncRAT malware dubbed HotRat is being distributed via free, pirated versions...
Intrusion Detection Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: All modern enterprises must accept the fact that at some point their systems or networks will very likely experience an unauthorized intrusion...
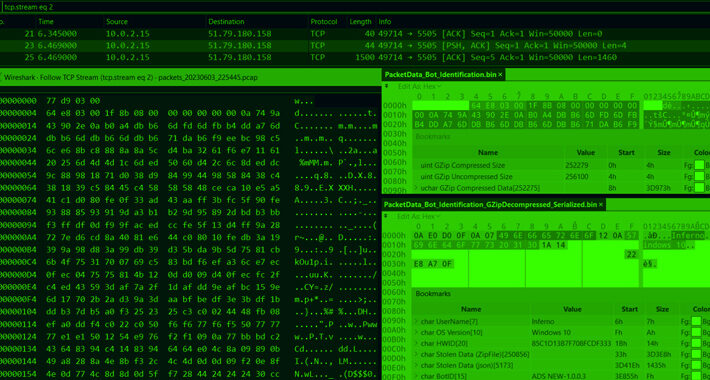
Sophisticated BundleBot Malware Disguised as Google AI Chatbot and Utilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 21, 2023THNCyber Threat / Malware A new malware strain known as BundleBot has been stealthily operating under the radar by...
Local Governments Targeted for Ransomware – How to Prevent Falling Victim – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 21, 2023The Hacker NewsPassword Security / Cybersecurity Regardless of the country, local government is essential in most citizens’ lives. It...
DDoS Botnets Hijacking Zyxel Devices to Launch Devastating Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 21, 2023THNVulnerability / Botnet Several distributed denial-of-service (DDoS) botnets have been observed exploiting a critical flaw in Zyxel devices that...
Citrix NetScaler ADC and Gateway Devices Under Attack: CISA Urges Immediate Action – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 21, 2023THNVulnerability / Cyber Threat The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory on Thursday warning that...
North Korean Attackers Targeted Crypto Companies in JumpCloud Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Researchers have attributed the recent JumpCloud breach to a branch of North Korea’s Lazarus Group. Early indications...
Mallox Ransomware Group Activity Shifts Into High Gear – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A ransomware actor with a penchant for breaking into target networks via vulnerable SQL servers has...
Critical Infrastructure Workers Better At Spotting Phishing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Phishing simulation training for employees appears to work better at critical infrastructure organizations than it does across...
Kevin Mandia Brings the HammerCon – Source: www.darkreading.com
Source: www.darkreading.com – Author: Edge Editors, Dark Reading HammerCon is a gathering of US military cyber professionals organized by the Military Cyber Professionals Association. One of...
Estée Lauder Breached in Twin MOVEit Hacks, by Different Ransom Groups – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Both the Cl0p and BlackCat ransomware gangs posted messages bragging about breaching Estée Lauder by way of the...
Apache OpenMeetings Wide Open to Account Takeover, Code Execution – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Three separate security vulnerabilities in the Apache OpenMeetings open source Web conferencing application can be strung together...
Docker Leaks API Secrets & Private Keys, as Cybercriminals Pounce – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Container images shared on Docker Hub are leaking sensitive data in the cloud, to the tune of tens...
Should You Be Using a Cybersecurity Careers Framework? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jamal Elmellas , Chief Operating Officer, Focus on Security One of the biggest issues within the cybersecurity sector is the way roles...
Is Artificial Intelligence Making People More Secure? Or Less? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alex Laurien Like anything, AI can be used maliciously. But when used for good, AI can be a game changer. In May...
The Week in Security: Google Cloud Build permissions can be poisoned, WormGPT weaponizes AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kate Tenerowicz Welcome to the latest edition of The Week in Security, which brings you the newest headlines from both the world...