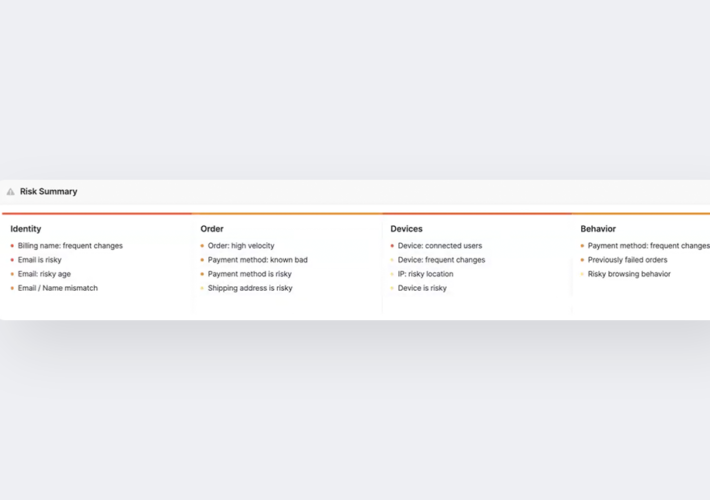
Source: securityboulevard.com – Author: Coby Montoya Machine learning-based fraud decision engines are sometimes viewed as mysterious black boxes that only provide minimal insight into why a...
Author: admin
Google Launches Red Team to Secure AI Systems Against Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Google is rolling out a red team charged with testing the security of AI systems by running simulated but realistic...
Netography Fusion Enhancements Give SOC, NOC, and AIOps Teams Faster Detection and Response to Anomalies and Threats, Automated Context Label Creation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Patrick Bedwell Netography Fusion Enhancements Give SOC, NOC, and AIOps Teams Faster Detection and Response to Anomalies and Threats, Automated Context Label...
How to Safeguard PHI From Healthcare SaaS Risks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Josh Smith, Strategic Alliance Manager @ AppOmni Five Critical Steps to Securing Healthcare SaaS 2. Identify which SaaS apps house your crown...
Auditing and Logging Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Many computer systems, network devices and other technological hardware used in the enterprise can audit and log various activities. These activities include...
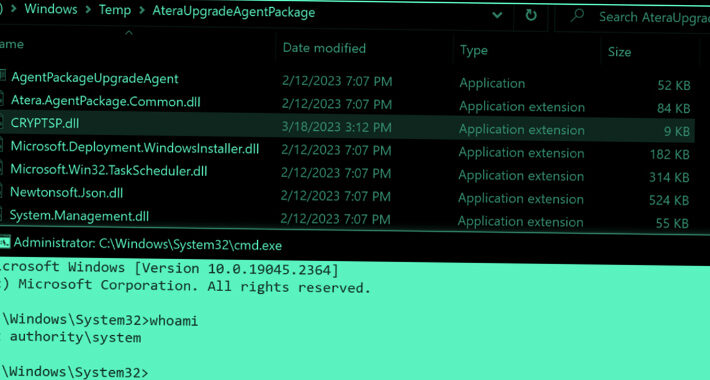
Critical Zero-Days in Atera Windows Installers Expose Users to Privilege Escalation Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 24, 2023THNWindows Security / Zero-Day Zero-day vulnerabilities in Windows Installers for the Atera remote monitoring and management software could act...
How to Protect Patients and Their Privacy in Your SaaS Apps – Source:thehackernews.com
Source: thehackernews.com – Author: . The healthcare industry is under a constant barrage of cyberattacks. It has traditionally been one of the most frequently targeted industries,...
New OpenSSH Vulnerability Exposes Linux Systems to Remote Command Injection – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 24, 2023THNLinux / Network Security Details have emerged about a now-patched flaw in OpenSSH that could be potentially exploited to...
Banking Sector Targeted in Open-Source Software Supply Chain Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity researchers said they have discovered what they say is the first open-source software supply chain attacks specifically targeting the banking...
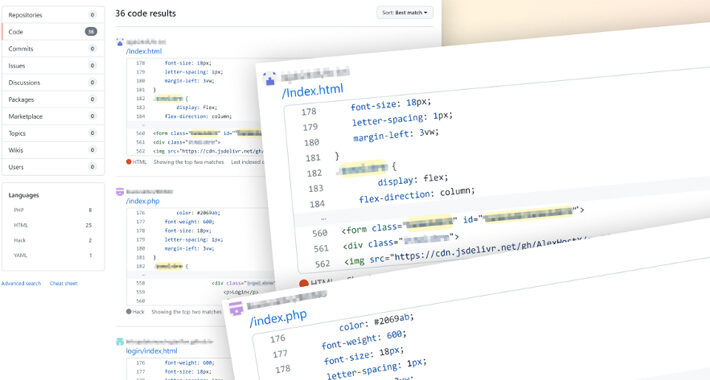
Linux Hacker Exploits Researchers With Fake PoCs Posted to GitHub – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A GitHub user managed to dupe security researchers by publishing fake proofs-of-concept (PoCs) containing Linux backdoors....
Crossing the road – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Palmer Last week I spoke for Jersey Cyber Security Centre ( CERT.JE) about the changing threats facing us — from the very active...
How Hackers Can Hijack a Satellite – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A computer flying hundreds or even thousands of kilometers in the sky, at a speed of...
Cisco Flags Critical SD-WAN Vulnerability – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A critical security vulnerability in Cisco’s SD-WAN vManage software could allow a remote, unauthenticated attacker to gain read and...
Rogue Azure AD Guests Can Steal Data via Power Apps – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading Guest accounts in Azure AD (AAD) are meant to provide limited access to corporate resources for...
Zimbra Zero-Day Demands Urgent Manual Update – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Teams running the Zimbra Collaboration Suite version 8.8.15 are urged to apply a manual fix against a...
Training’s New Understanding – Source: www.darkreading.com
Source: www.darkreading.com – Author: Curtis Franklin, Senior Analyst, Omdia Cybersecurity awareness training is a risky business. And the importance of measuring risk before and after training...
Electrical Grid Stability Relies on Balancing Digital Substation Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Steve Kunsman, Director of Product Management and Applications, Hitachi Energy With a central role in modern electrical systems, digital substations are of...
Brand Impersonation Scams in Middle East & Africa See Massive Growth – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The number of detected fake and scam websites pertaining to be reputable brands from the Middle...
White House Fills in Details of National Cybersecurity Strategy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Fresh from the federal policy mill, the Biden Administration’s 57-page National Cybersecurity Strategy Implementation Plan (NCSIP)...
Review: Can We Trust the Waterfox Browser? (Updated 2023) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avoid The Hack! Waterfox came into the browser scene in 2011, coming right out the box with official x64 support (a rarity...
How to use Repository Health Check 2.0 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sonatype Hot Topics GitHub Developers Targeted by North Korea’s Lazarus Group Few Fortune 100 Firms List Security Pros in Their Executive Ranks...
Google Categorizes 6 Real-World AI Attacks to Prepare for Now – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Google researchers have identified six specific attacks that can occur against real-world AI systems, finding that these common attack vectors...
Hacker-Turned-Security-Researcher Kevin Mitnick Dies Aged 59 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Noted hacker and security researcher Kevin Mitnick has died at the age of 59, following a 14-month...
Study: Africa Cybersecurity Improves but Lacks Cross-Border Frameworks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading While cybersecurity expenditures in Africa are projected to grow to $3.7 billion by 2025 (up nearly...
SophosEncrypt Ransomware Fools Security Researchers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The SophosEncrypt ransomware-as-a-service (RaaS) threat has emerged, after flying under the radar by impersonating cybersecurity vendor Sophos. The...
5 Major Takeaways From Microsoft’s July Patch Tuesday – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Keep up with the latest cybersecurity threats, newly-discovered vulnerabilities, data breach information, and emerging trends....
AWS Cloud Credential Stealing Campaign Spreads to Azure, Google Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A sophisticated cloud-credential stealing and cryptomining campaign targeting Amazon Web Services (AWS) environments for the past...
UAE and South African Hospitals Fail on DMARC Implementation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Around three-quarters of hospitals in the United Arab Emirates and South Africa have not adopted the...
If George Washington Had a TikTok, What Would His Password Be? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Gil Cohen, Head of Application Security and Secure-SDLC, CYE Have you ever thought of what George Washington’s hypothetical TikTok password might be?...