Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading People could potentially lose more than just pounds by using a Peloton treadmill, as the Internet-connected fitness...
Author: admin
Decoy Dog: New Breed of Malware Posing Serious Threats to Enterprise Networks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNMalware / Cyber Threat A deeper analysis of a recently discovered malware called Decoy Dog has revealed that it’s...
The Alarming Rise of Infostealers: How to Detect this Silent Threat – Source:thehackernews.com
Source: thehackernews.com – Author: . A new study conducted by Uptycs has uncovered a stark increase in the distribution of information stealing (a.k.a. infostealer or stealer)...
Fenix Cybercrime Group Poses as Tax Authorities to Target Latin American Users – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNOnline Security / Malware Tax-paying individuals in Mexico and Chile have been targeted by a Mexico-based cybercrime group that...
New AI Tool ‘FraudGPT’ Emerges, Tailored for Sophisticated Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNCyber Crime / Artificial Intelligence Following the footsteps of WormGPT, threat actors are advertising yet another cybercrime generative artificial...
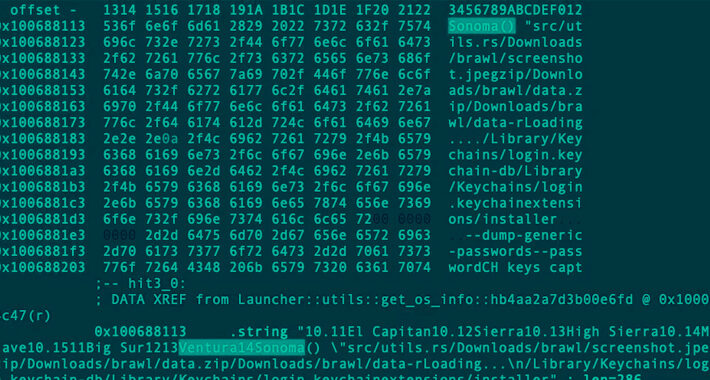
Rust-based Realst Infostealer Targeting Apple macOS Users’ Cryptocurrency Wallets – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNCryptocurrency / Endpoint Security A new malware family called Realst has become the latest to target Apple macOS systems,...
Critical MikroTik RouterOS Vulnerability Exposes Over Half a Million Devices to Hacking – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNNetwork Security / Vulnerability A severe privilege escalation issue impacting MikroTik RouterOS could be weaponized by remote malicious actors...
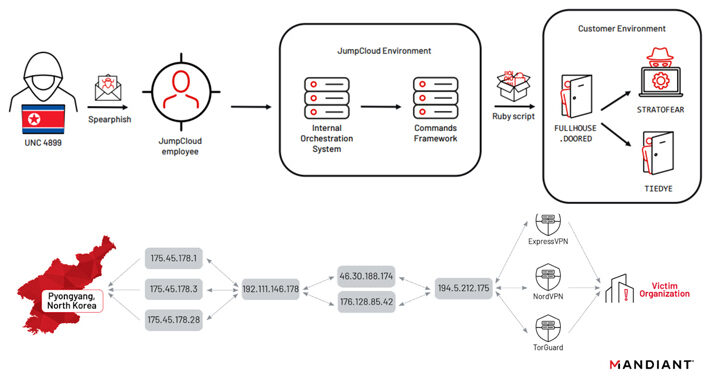
North Korean Nation-State Actors Exposed in JumpCloud Hack After OPSEC Blunder – Source:thehackernews.com
Source: thehackernews.com – Author: . North Korean nation-state actors affiliated with the Reconnaissance General Bureau (RGB) have been attributed to the JumpCloud hack following an operational...
FraudGPT Follows WormGPT as Next Threat to Enterprises – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Less than two weeks after WormGPT hit the scene as threat actors’ alternative to the wildly popular ChatGPT generative AI...
Zero-Day Vulnerabilities Discovered in Global Emergency Services Communications Protocol – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading A radio communications protocol used by emergency services worldwide harbors several critical vulnerabilities that could allow...
Decoy Dog Gets an Upgrade With New Persistence Features – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Discovered just a few months ago, Decoy Dog, a remote access Trojan based on open-source Pupy malware,...
ChatGPT, Other Generative AI Apps Prone to Compromise, Manipulation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Users of applications that use ChatGPT-like large language models (LLMs) beware: An attacker that creates untrusted...
Ivanti Zero-Day Exploit Disrupts Norway’s Government Services – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading A zero-day authentication bypass vulnerability in Ivanti software was exploited to carry out an attack on...
Cybercrime as a Public Health Crisis – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Cobb, Independent Researcher If you’ve ever been defrauded, you may have found it hard to deal with. I know I did,...
Patch Now: Up to 900K MikroTik Routers Vulnerable to Total Takeover – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Up to 900,00 MikroTik routers — a popular target for threat actors including nation-state groups —...
‘FraudGPT’ Malicious Chatbot Now for Sale on Dark Web – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors riding on the popularity of ChatGPT have launched yet another copycat hacker tool that offers...
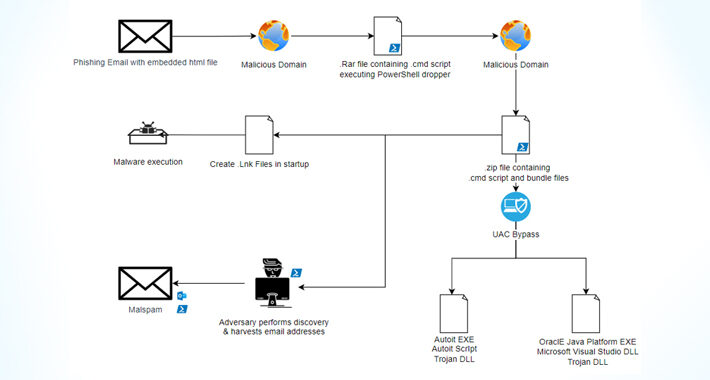
Casbaneiro Banking Malware Goes Under the Radar with UAC Bypass Technique – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNMalware / Cyber Threat The financially motivated threat actors behind the Casbaneiro banking malware family have been observed making...
macOS Under Attack: Examining the Growing Threat and User Perspectives – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023The Hacker NewsEndpoint Security / macOS As the number of people using macOS keeps going up, so does the...
TETRA:BURST — 5 New Vulnerabilities Exposed in Widely Used Radio Communication System – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNNetwork Security / Vulnerability A set of five security vulnerabilities have been disclosed in the Terrestrial Trunked Radio (TETRA)...
How MDR Helps Solve the Cybersecurity Talent Gap – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023The Hacker NewsCyber Threat Intelligence How do you overcome today’s talent gap in cybersecurity? This is a crucial issue...
Zenbleed: New Flaw in AMD Zen 2 Processors Puts Encryption Keys and Passwords at Risk – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNHardware Security / Encryption A new security vulnerability has been discovered in AMD’s Zen 2 architecture-based processors that could...
Atlassian Releases Patches for Critical Flaws in Confluence and Bamboo – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNServer Security / Zero Day Atlassian has released updates to address three security flaws impacting its Confluence Server, Data...
Ivanti Releases Urgent Patch for EPMM Zero-Day Vulnerability Under Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNEnterprise Security / Zero Day Ivanti is warning users to update their Endpoint Manager Mobile (EPMM) mobile device management...
Apple Rolls Out Urgent Patches for Zero-Day Flaws Impacting iPhones, iPads and Macs – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 25, 2023THNEndpoint Security / Zero Day Apple has rolled out security updates to iOS, iPadOS, macOS, tvOS, watchOS, and Safari...
China Propaganda Spreads via US News Sites, Freelancers, Times Square – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The organizers of a pro-People’s Republic of China (PRC) influence campaign called “HaiEnergy” are taking the...
Orgs Face Record $4.5M Per Data Breach Incident – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading The average cost per data breach for business in 2023 jumped to $4.45 million, a 15% increase...
Are AI-Engineered Threats FUD or Reality? – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Dwyer, Head of Research, IBM Security X-Force The moment that generative AI applications hit the market, it changed the pace of...
Atlassian RCE Bugs Plague Confluence, Bamboo – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Three just-disclosed remote code execution (RCE) security vulnerabilities open up Atlassian Confluence Data Center & Server, and...
KillNet’s Kremlin Connection Unclear as the Cybercrime Collective Grows – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Although the precise connection between Russian threat group KillNet and the Kremlin remains nebulous, its high-profile, and increasingly...
IBM: Cost of a Data Breach Hits Another High – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The average cost to an organization hit with a data breach reached a record high this year, though those companies...