Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The US military was reckoning with two major cyber concerns over the weekend — one the...
Author: admin
Air-Gapped ICS Systems Targeted by Sophisticated Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Security teams in industrial control systems (ICS) environments are fighting a worm that gets past air-gapped defenses. Researchers...
Abyss Locker Ransomware Looks to Drown VMware’s ESXi Servers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The Abyss Locker ransomware gang is now a threat to industrial control systems (ICS), enterprises, and public-sector organizations...
Call of Duty Self-Spreading Worm Takes Aim at Player Lobbies – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Activision, the video game publisher behind Call of Duty: Modern Warfare II, the popular first-person shooter, has...
New P2PInfect Worm Targets Redis Servers with Undocumented Breach Methods – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 31, 2023THNCyber Threat / Botnet The P2PInfect peer-to-peer (P2) worm has been observed employing previously undocumented initial access methods to...
Server Inventory Checklist – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: It’s important to maintain accurate infrastructure inventories to assist secure and effective network administration. A checklist, like the accompanying file from TechRepublic...
Data Encryption Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: The Data Encryption Policy’s purpose is to define for employees, computer users and IT department staff the encryption requirements to be used...
Israeli Oil Refinery Taken Offline by Pro-Iranian Attackers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The website of Israel’s largest oil refinery is inaccessible after it was attacked by an Iranian hacktivist...
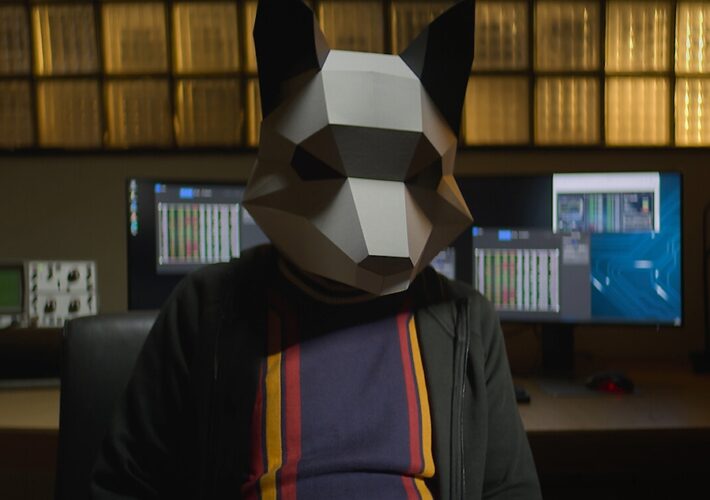
Summer Documentary Watch Party: 8 Sizzling Cybersecurity Tales – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor Keep up with the latest cybersecurity threats, newly-discovered vulnerabilities, data breach information, and emerging trends. Delivered daily or...
Patchwork Hackers Target Chinese Research Organizations Using EyeShell Backdoor – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 31, 2023THNCyber Espionage / Malware Threat actors associated with the hacking crew known as Patchwork have been spotted targeting universities...
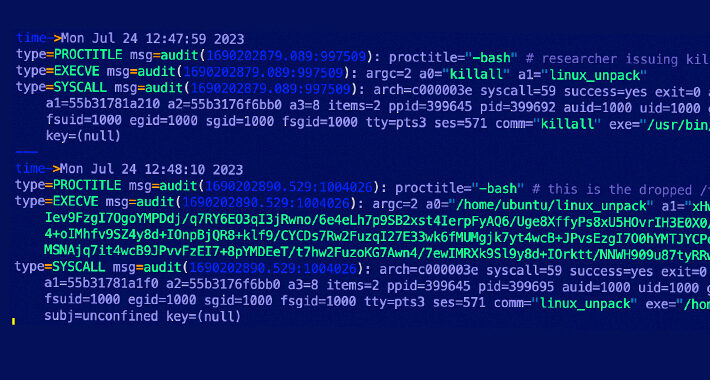
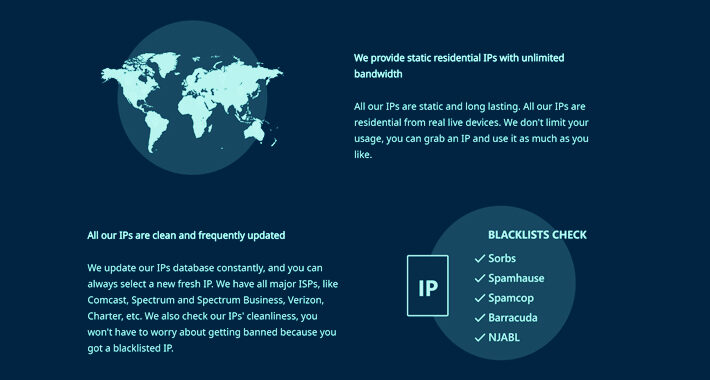
AVRecon Botnet Leveraging Compromised Routers to Fuel Illegal Proxy Service – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 31, 2023THNNetwork Security / Botnet More details have emerged about a botnet called AVRecon, which has been observed making use...
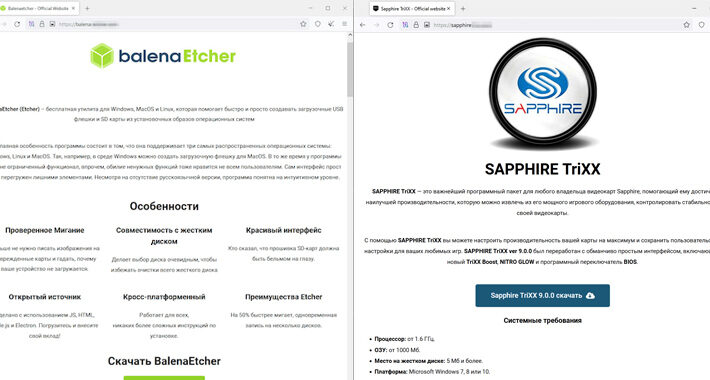
Fruity Trojan Uses Deceptive Software Installers to Spread Remcos RAT – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 31, 2023THNMalware / Cyber Threat Threat actors are creating fake websites hosting trojanized software installers to trick unsuspecting users into...
Multiple Flaws Found in Ninja Forms Plugin Leave 800,000 Sites Vulnerable – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 31, 2023THNWebsite Security / WordPress Multiple security vulnerabilities have been disclosed in the Ninja Forms plugin for WordPress that could...
New Android Malware CherryBlos Utilizing OCR to Steal Sensitive Data – Source:thehackernews.com
Source: thehackernews.com – Author: . A new Android malware strain called CherryBlos has been observed making use of optical character recognition (OCR) techniques to gather sensitive...
RFP Template for Browser Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 29, 2023The Hacker NewsBrowser Security / Data Security Increasing cyber threats and attacks have made protecting organizational data a paramount...
Apple Sets New Rules for Developers to Prevent Fingerprinting and Data Misuse – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 29, 2023THNData Security / Privacy Apple has announced plans to require developers to submit reasons to use certain APIs in...
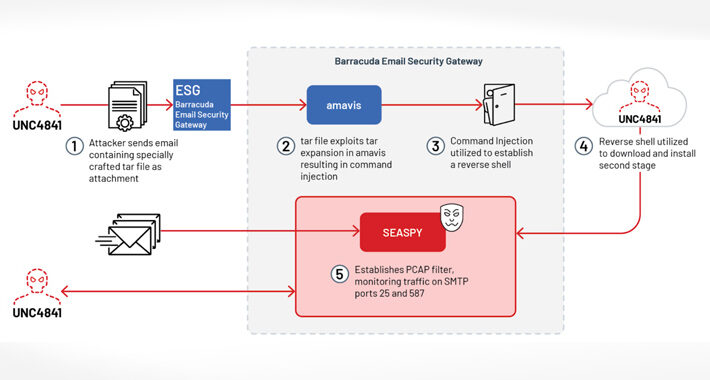
Hackers Deploy “SUBMARINE” Backdoor in Barracuda Email Security Gateway Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 29, 2023THNEmail Security / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday disclosed details of a “novel...
Ivanti Warns of Another Endpoint Manager Mobile Vulnerability Under Active Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 29, 2023THNVulnerability / Enterprise Security Ivanti has disclosed yet another security flaw impacting Endpoint Manager Mobile (EPMM), formerly known as...
Hack Crew Responsible for Stolen Data, NATO Investigates Claims – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading SiegedSec, a hacktivist crew that targets government bodies, shared on their Telegram channel what they claim to...
CherryBlos Malware Uses OCR to Pluck Android Users’ Cryptocurrency – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Researchers this week warned of two related malware campaigns, dubbed CherryBlos and FakeTrade, targeting Android users for cryptocurrency...
Stark#Mule Malware Campaign Targets Koreans, Uses US Army Documents – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading A Korean-language malware campaign known as Stark#Mule is targeting victims using US military recruiting documents as...
Senator Blasts Microsoft for Negligence in 365 Email Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The heads of the Justice Department, the Cybersecurity and Infrastructure Security Agency, and the Federal Trade Commission...
Another AI Pitfall: Digital Mirroring Opens New Cyberattack Vector – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading “Digital twins” — AI assistants trained to service our many needs by learning about and in...
Beyond ChatGPT: Organizations Must Protect Themselves Against the Power of AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fred Kwong, Vice President & Chief Information Security Officer, DeVry University Society is on the frontier of new possibilities with artificial intelligence...
North Korean Cyberspies Target GitHub Developers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading The North Korean state-sponsored Lazarus advanced persistent threat (APT) group is back with yet another impersonation scam, this time...
Cybersecurity Insights with Contrast CISO David Lindner | 7/28 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 A recent report by Cohesity sees the top three things being required for cyber insurance...
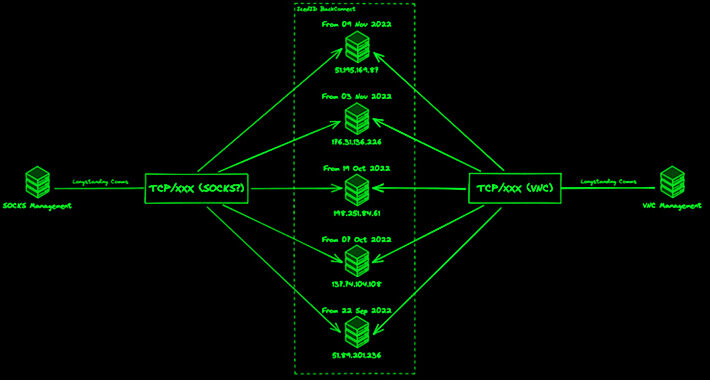
IcedID Malware Adapts and Expands Threat with Updated BackConnect Module – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 28, 2023THNMalware / Cyber Threat The threat actors linked to the malware loader known as IcedID have made updates to...
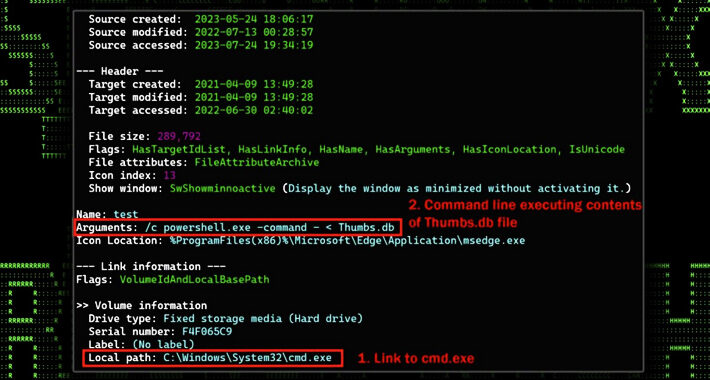
STARK#MULE Targets Koreans with U.S. Military-themed Document Lures – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 28, 2023THNCyber Attack / Malware An ongoing cyber attack campaign has set its sights on Korean-speaking individuals by employing U.S....
Why CISOs Should Get Involved With Cyber Insurance Negotiation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Sometimes being the CISO can be a no-win position. According to a recent survey by human resources and...
Despite Post-Log4j Security Gains, Developers Can Still Improve – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Developers are increasingly adopting security testing as part of the development pipeline, but companies still have...