Source: www.csoonline.com – Author: Die Server des Autoteilezulieferes Yorozu wurden verschlüsselt. mayam_studio – Shutterstock.com Der japanische Autoteilezulieferer Yorozu stellte kürzlich fest, dass seine Server verschlüsselt wurden....
Month: October 2024
7 risk management mistakes CISOs still make – Source: www.csoonline.com
Source: www.csoonline.com – Author: Given its importance and complexity, risk management is a trap door for many CISOs. Here are seven ways to keep your enterprise...
Low turnover leaves job-seeking CISOs with nowhere to go – Source: www.csoonline.com
Source: www.csoonline.com – Author: News Analysis 22 Oct 20245 mins CareersCSO and CISOSalaries Workplace stress has many security executives eyeing the exit. But fewer options, and...
Singapore unveils AI system guidelines, emphasizing secure-by-design – Source: www.csoonline.com
Source: www.csoonline.com – Author: A secure-by-design approach for AI systems can be challenging, as it requires specialized skills and may involve significant costs. Singapore has rolled...
Showcasing our Industry-First BDR Solution in Singapore – Source: securityboulevard.com
Source: securityboulevard.com – Author: SquareX SquareX @ Cyber Security World Asia + GovWare 2024 October 2024 marked an exciting time for SquareX as we returned to our...
DEF CON 32 – AppSec Village – Lessons Learned from Building and Defending LLM Applications – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Tuesday, October 22, 2024 Home » Cybersecurity » Application Security » DEF CON 32 – AppSec Village – Lessons Learned...
USENIX NSDI ’24 – Harvesting Idle Memory for Application-managed Soft State with Midas – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Yifan Qiao, Zhenyuan Ruan, Haoran Ma, Adam Belay, Miryung Kim, Harry Xu Our sincere thanks to USENIX, and the Presenters...
Modernizing Data Security: Imperva and IBM zSystems in Action – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lynne Murray As data security continues to evolve, businesses require solutions that scale to modern environments. Imperva and IBM zSystems have partnered...
USENIX NSDI ’24 – SIEVE is Simpler than LRU: An Efficient Turn-Key Eviction Algorithm for Web Caches – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Community Award Winner! Authors/Presenters:Yazhuo Zhang, Juncheng Yang, Yao Yue, Ymir Vigfusson, K.V. Rashmi Our sincere thanks to USENIX, and the...
How Security Automation Platforms Streamline SOC Operations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maycie Belmore What is a security automation platform? A security automation platform automates key tasks in security operations, reducing the need for...
USENIX NSDI ’24 – Accelerating Skewed Workloads With Performance Multipliers in the TurboDB Distributed Database – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Jennifer Lam, Jeffrey Helt, Wyatt Lloyd, Haonan Lu Our sincere thanks to USENIX, and the Presenters & Authors for publishing...
Is an AI-augmented SOC The Way Forward? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire Even with the growing focus on innovation, fear, uncertainty, and doubt (FUD) continue to influence how some perceive AI advancements...
What We Can Learn From Recent Ransomware Attacks – Source:www.hackerone.com
Source: www.hackerone.com – Author: HackerOne. Earlier this month, software vendor Kaseya made headlines when a vulnerability in its Virtual System Administrator (VSA) software led to an...
Grandoreiro, the global trojan with grandiose ambitions – Source: securelist.com
Source: securelist.com – Author: GReAT Grandoreiro is a well-known Brazilian banking trojan — part of the Tetrade umbrella — that enables threat actors to perform fraudulent...
SEC Charges Four Companies Over Misleading Disclosures on SolarWinds Hack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine The US Securities and Exchange Commission (SEC) on Tuesday announced charges and million-dollar penalties against four prominent companies for “making...
US Police Detective Charged With Purchasing Stolen Credentials – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Department of Justice has announced charges against a Buffalo police detective who allegedly bought stolen credentials and on...
Stream.Security Secures $30 Million Series B – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Israeli early-stage startup Stream.Security has banked $30 million in a new round of venture capital funding to continue work on...
SecurityWeek’s 2024 ICS Cybersecurity Conference Kicks Off in Atlanta – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek’s 2024 ICS Cybersecurity Conference kicks off today at the InterContinental Hotel Buckhead Atlanta. With 80+ sessions over three days, the conference...
Google Warns of Samsung Zero-Day Exploited in the Wild – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A zero-day vulnerability in Samsung’s mobile processors has been leveraged as part of an exploit chain for arbitrary code execution,...
Critical Vulnerabilities Expose mbNET.mini, Helmholz Industrial Routers to Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Germany’s CERT@VDE has alerted organizations to several critical and high-severity vulnerabilities discovered recently in industrial routers. Impacted vendors have released...
BlackCat Ransomware Successor Cicada3301 Emerges – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The Alphv/BlackCat ransomware gang might have pulled an exit scam in early March, but the threat appears to have resurfaced...
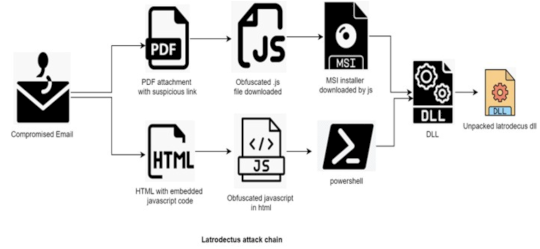
Latrodectus Malware Increasingly Used by Cybercriminals – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend The Latrodectus malware has been increasingly used by cybercriminals, with recent campaigns targeting the financial, automotive and healthcare sectors, according...
Securing the Supply Chain by Working With Ethical Hackers – Source:www.hackerone.com
Source: www.hackerone.com – Author: HackerOne. Software supply chain attacks increasingly create concern among cybersecurity experts as these exploits are becoming more common. But solving the problem...
Socket Accelerates Open-Source Security With $40M Series B – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Application Security , Application Security & Online Fraud , Fraud Management & Cybercrime Socket Plans to Triple Headcount After Big Growth, Deliver...
Researchers Debut AI Tool That Helps Detect Zero-Days – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development Vulnerability Tool Detected Flaws in OpenAI...
CISA Ramping Up Election Security Warnings as Voting Begins – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Election Security , Fraud Management & Cybercrime , Government US Cyber Defense Agency Says Election Is Secure Despite Intensifying Threats Chris Riotta...
Dental Center Chain Settles Data Breach Lawsuit for $2.7M – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Legislation & Litigation , Standards, Regulations & Compliance 2023 Hacking Incident Affected 1.9 Million Patients, Employees Marianne Kolbasuk McGee (HealthInfoSec) • October...
What Today’s SOC Teams Can Learn From Baseball – Source: www.darkreading.com
Source: www.darkreading.com – Author: Mike Mitchell Mike Mitchell, VP, Threat Hunt Intelligence, Intel 471 October 22, 2024 5 Min Read Source: Augustas Cetkauskas via Alamy Stock...
Name That Toon: The Big Jump – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Need a push? A day for a cybersecurity professional can be full of adrenaline-pumping moments. Come up with a...
Russia-Linked Hackers Attack Japan’s Govt, Ports – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: StudioProX via Shutterstock Two Russian hacking groups leveled distributed denial-of-service (DDoS) attacks at Japanese logistics and shipbuilding...