Source: www.infosecurity-magazine.com – Author: The Embargo ransomware group is deploying customized Rust-based tooling to overcome cybersecurity defenses, according to ESET researchers. The new toolkit was observed...
Month: October 2024
Former British PM Cameron Calls for Tech Engagement with China Despite Cyber Threats – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Written by The US, UK and like-minded nations should strengthen their security strategy against Chinese cyber threats but also try to collaborate...
70% of Leaders See Cyber Knowledge Gap in Employees – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Nearly 70% of business leaders believe their employees lack critical cybersecurity knowledge, a sharp increase from 56% in 2023. The figure comes from...
Exploring the Latest Security Innovations at Hardwear.io – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Endpoint Security , Hardware / Chip-level Security , Internet of Things Security Annual Conference and Hackathon Showcases Solutions for Protecting IoT Devices...
Retaining EU Adequacy Crucial to UK Economy: Lawmaker – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: General Data Protection Regulation (GDPR) , Geo Focus: The United Kingdom , Geo-Specific Europe Will Renew or Deny Data Sharing Agreement in...
Check Point, Mimecast Settle SEC Case From SolarWinds Hack – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Security and Exchange Commission compliance (SEC) SEC: Check Point, Mimecast Disclosures Didn’t...
No, The Chinese Have Not Broken Modern Encryption Systems with a Quantum Computer – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Who? • October 22, 2024 9:48 AM My background in theoretical physics (named “fundamental physics” at my University)...
Code Red: How KnowBe4 Exposed a North Korean IT Infiltration – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Fraud Management & Cybercrime , Ransomware , Social Engineering Presented by KnowBe4 60mins A recent incident shed light...
Live Webinar | Agency Cyber Incident Response Team (CIRT) Playbook – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Presented by Center for Information Security (CIS) 60 Minutes If you’re like other U.S. State, Local, Tribal, and...
How AI Can Eliminate Graymail to Increase Employee Productivity – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Email Security & Protection , Fraud Management & Cybercrime Mike Britton • October 22, 2024 The trend toward remote working...
Exploring the Latest Security Innovations at Hardwear.io – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Endpoint Security , Hardware / Chip-level Security , Internet of Things Security Annual Conference and Hackathon Showcases Solutions for Protecting IoT Devices...
Retaining EU Adequacy Crucial to UK Economy: Lawmaker – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: General Data Protection Regulation (GDPR) , Geo Focus: The United Kingdom , Geo-Specific Europe Will Renew or Deny Data Sharing Agreement in...
Check Point, Mimecast Settle SEC Case From SolarWinds Hack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Security and Exchange Commission compliance (SEC) SEC: Check Point, Mimecast Disclosures Didn’t...
Code Red: How KnowBe4 Exposed a North Korean IT Infiltration – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Fraud Management & Cybercrime , Ransomware , Social Engineering Presented by KnowBe4 60mins A recent incident shed light...
How AI Can Eliminate Graymail to Increase Employee Productivity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Email Security & Protection , Fraud Management & Cybercrime Mike Britton • October 22, 2024 The trend toward remote working...
Team-Based Training and the Power of Simulation – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Tom Marsland Cloud Range October 22, 2024 In the constantly evolving realm of cybersecurity, it is critical for incident responders...
The AI Fix #21: Virtual Trump, barking mad AI, and a robot dog with a flamethrower – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Skip to content News and views from the world of artificial intelligence. In episode 21 of “The AI Fix”, Mark...
Grandoreiro, the global trojan with grandiose goals – Source: securelist.com
Source: securelist.com – Author: GReAT Grandoreiro is a well-known Brazilian banking trojan — part of the Tetrade umbrella — that enables threat actors to perform fraudulent...
Samsung Zero-Day Vuln Under Active Exploit, Google Warns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: B Christopher via Alamy Stock Photo A zero-day vulnerability, tracked as CVE-2024-44068, has been discovered in Samsung’s mobile...
Honeywell and Google Cloud to Accelerate Auto Operations With AI Agents for the Industrial Sector – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE CHARLOTTE, N.C. and SUNNYVALE, Calif., Oct. 21, 2024 /PRNewswire/ — Honeywell (NASDAQ: HON) and Google Cloud announced a unique collaboration connecting artificial intelligence (AI) agents with assets, people...
OPA for Windows Vulnerability Exposes NTLM Hashes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: adison pangchai via Shutterstock Organizations using Open Policy Agent (OPA) for Windows should consider updating to v0.68.0...
SoftwareOne Launches Cloud Competency Centre in Malaysia – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Kuala Lumpur, Malaysia – 22 Oct. 2024 – SoftwareOne Holding AG, a leading global software and cloud solutions provider, has launched a...
Retail & Hospitality ISAC Launches Program Aimed at Securing Supply Chains – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE VIENNA, VA (October 22, 2024) – The Retail and Hospitality Information Sharing and Analysis Center (RH-ISAC) announced the launch of...
Most US Political Campaigns Lack DMARC Email Protection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Saphiens via Alamy Stock Photo Nearly 75% of US Senate campaign websites are lacking when it comes to...
Swarms of Fake WordPress Plug-ins Infect Sites With Infostealers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Primakov via Shutterstock Threat actors have taken a campaign that uses fake browser updates to spread malware...
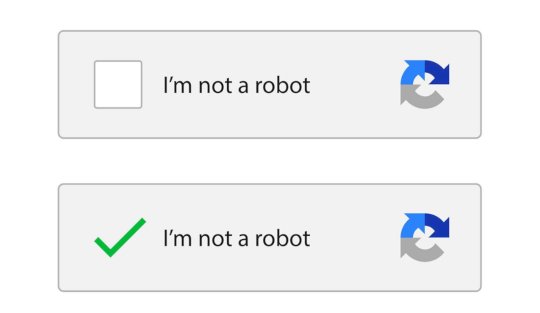
Tricky CAPTCHA Caught Dropping Lumma Stealer Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Oleksandr Hruts via Alamy Stock Photo Lumma Stealer stars in a new campaign that uses...
User-Experience-Irrwege: 5 Fehler, die Ihre Sicherheit gefährden – Source: www.csoonline.com
Source: www.csoonline.com – Author: Manche Unternehmen zwingen ihren Mitarbeitern unnötig komplexe und damit kontraproduktive Sicherheitsmaßnahmen auf – obwohl sie es besser wissen sollten. Übermäßig komplexe, unnötige...
Four firms charged, fined over handling of SolarWinds hack disclosures – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 22 Oct 20246 mins Data BreachThreat and Vulnerability Management Analyst says there are lessons for CSOs in the contents of the...
Threat actors increasingly using malicious virtual hard drives in phishing attacks – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 22 Oct 20245 mins Email SecurityMalwareSecurity The tactic is a way of getting around email gateways and antivirus, according to Cofense....
IBM adds quantum-resistant controls within new security suite – Source: www.csoonline.com
Source: www.csoonline.com – Author: New offerings are targeted at bolstering an organization’s cryptographic and AI security posture. In an effort to arm organizations against emerging AI...