Source: www.databreachtoday.com – Author: 1 Hector Monsegur Director of Research, Alacrinet Hector Monsegur is an internationally recognized expert on global cyber security issues and a leading...
Month: June 2024
August Spotlight | Automated Threat Intelligence Correlation – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Getting a Firmer Grip on AI Privacy Concerns in Healthcare – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial intelligence technologies offer tremendous promise in healthcare, but it’s crucial for organizations to carefully assess the complex data privacy concerns...
How the Growing Demands of Healthcare Are Complicating Risk – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare is increasingly complex and interconnected, and the push to exchange more digital patient information among providers adds to the risk...
Chinese Hackers Used Open-Source Rootkits for Espionage – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Network Firewalls, Network Access Control UNC3886 Targeted Edge Devices for Persistence,...
Radiology Practice Hack Affects Sensitive Data of 512,000 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Cybercrime , Fraud Management & Cybercrime Breach Is Latest Major Cyber Incident Reported by a Medical Imaging Provider...
Popular Chatbots Spout Russian Misinformation, Finds Study – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development OpenAI, Meta and 8 Other Chatbots Use Disinformation Network as...
Pentagon Cybersecurity, Workforce Woes Threaten Tech Rollout – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Government , Industry Specific New Report Says DOD Is Lagging in Procuring New Tech Amid Cybersecurity...
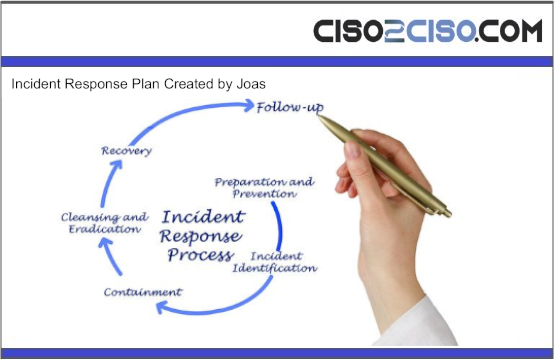
INCIDENT RESPONSE PLAN
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
INCIDENT REPORTING TEMPLATE
The Incident Response Form captures essential details related to incident management within an organization. It includes sections such as Incident Response Details, Incident Report Information, Incident...
UK Pathology Lab Ransomware Attackers Demanded $50 Million – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware Russian-Speaking Gang Follows Typical Playbook; Critical Services Still Disrupted Mathew J. Schwartz (euroinfosec) • June...
Researchers Uncover Chinese Hacking Cyberespionage Campaign – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Chinese Threat Actor ‘Velvet Ant’ Evaded Detection...
Chemical Firms Boost Cybersecurity Ahead of New Regulations – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Leadership & Executive Communication , Training & Security Leadership New Report Finds Chemical Firms Are Investing in...
IMF Touts Fiscal Policy Change, Taxes to Soften AI Impact – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development Agency Suggests Taxing AI-Related Carbon...
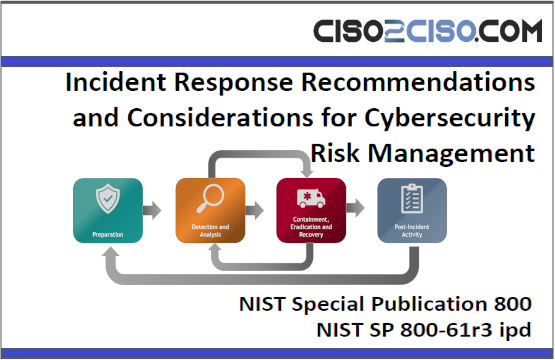
Incident Response Recommendations and Considerations for Cybersecurity Risk Management
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
From plan to deployment: Implementing a cloud-native application protection platform(CNAPP) strategy
The document emphasizes the importance of Cloud Security Posture Management (CSPM) and the utilization of Defender for Cloud to enhance security measures. It highlights the need...
Identity and Access Management Policy
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NHS Ransomware Attack: What Makes Healthcare a Prime Target for Ransomware? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Rubrik’s Steve Stone on Reducing Data-Related Vulnerabilities in Healthcare June 18, 2024...
Hackers Plead Guilty After Breaching Law Enforcement Portal – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Government Justice Says Sagar Steven Singh and Nicholas Ceraolo Doxed and Threatened Victims Chris...
Police Dismantle Asian Crime Ring Behind $25M Android Fraud – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Geo Focus: Asia , Geo-Specific Hackers Used Dozens of Servers to Distribute Malicious Android Apps Jayant...
CISA Conducts First-Ever AI Security Incident Response Drill – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Government US Cyber Defense Agency Developing AI Security Incident Collaboration...
Artificial Intelligence Risk Management Framework
Generative Artificial Intelligence Profile The document “NIST AI 600-1, Artificial Intelligence Risk Management Framework: Generative Artificial Intelligence Profile” outlines a comprehensive framework for managing risks associated...
National Cyber Strategy 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ley Marco de Ciberseguridad e Infraestructura Crítica de la Información
La Ley Marco de Ciberseguridad tiene como objetivo principal establecer un marco normativo que regule y coordine la ciberseguridad entre organismos estatales y privados. Esta ley...
MALWARE DEVELOPMENT PROCESS DIARIES
IN THIS COMPREHENSIVE GUIDE, WE DELVE INTO THE WORLD OF ANDROID SECURITY FROM AN OFFENSIVE PERSPECTIVE, SHEDDING LIGHT ON THE VARIOUS TECHNIQUES AND METHODOLOGIES USED BY...
MALWARE DEVELOPMENT EVADING DIARIES
IN THE INTRICATE LANDSCAPE OF CYBERSECURITY, MALWARE STANDS AS A PERVASIVE AND EVER-EVOLVING THREAT, CONTINUALLY ADAPTING TO CIRCUMVENT DETECTION AND EXPLOIT VULNERABILITIES IN DIGITAL SYSTEMS. ITS...
NSA Network Infrastructure Security Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NIST SP 800 Incident Response Recommendations and Considerations for Cybersecurity Risk Management
Incident response is a critical part of cybersecurity risk management and should be integrated across organizational operations. The six CSF 2.0 Functions play vital roles in...
NIST Policy Template Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NIST AI_Risk Management Framework Playbook
The Playbook provides suggested actions for achieving the outcomes laid out inthe AI Risk Management Framework (AI RMF) Core (Tables 1 – 4 in AI RMF1.0)....