Source: securityboulevard.com – Author: Jeffrey Burt The operators behind the Ebury server-side malware botnet have been doing business since at least 2009 and, according to the...
Month: May 2024
USENIX Security ’23 – It’s All In Your Head(Set): Side-Channel Attacks On AR/VR Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – It’s All In Your Head(Set): Side-Channel Attacks...
Will We Ever See Federal Data Breaches End Entirely? – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Government cybersecurity may get worse before it gets better. By April Miller, Managing Editor, ReHack Magazine Data breaches are a...
UK Lags Europe on Exploited Vulnerability Remediation – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 UK organizations are trailing their European counterparts on time to remediate software flaws in the US Known Exploited Vulnerability (KEV) catalog,...
BreachForums Hacking Marketplace Taken Down Again – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US authorities appear to have disrupted a notorious hacking forum, just days after a threat actor advertised data stolen from...
Bipartisan Senators Endorse $32M Annually for AI Research – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific Funding Aimed at Boosting Non-Defense Research and Innovation in AI Rashmi...
Live Webinar | Practical Strategies for Accelerating AI Adoption in Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Wade Ellery Field Chief Technology Officer, Radiant Logic Wade Ellery, Field Chief Technology Officer and Senior Technical Evangelist with Radiant Logic....
SIEM Stalwart LogRhythm to Merge With Exabeam – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Security Information & Event Management (SIEM) , Security Operations Cisco’s Earlier Acquisition of Splunk Makes Waves in the SIEM Market David...
AI Talks: Compliance Strategies for Global Data Privacy Regulations – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Kurt Roemer Chief Security Strategist, Citrix As Chief Security Strategist for Citrix Systems, Kurt Roemer leads the security, compliance, risk and...
Live Webinar | Techniques for Building Cyber Resiliency in Your Software Development Life Cycle – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 DevSecOps , Next-Generation Technologies & Secure Development , Security Awareness Programs & Computer-Based Training Presented by Security Innovation 60...
Report: 11 Vulnerabilities Found in GE Ultrasound Devices – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Healthcare , Industry Specific GE HealthCare Says Risks Can Largely Be Mitigated Through Security Best Practices...
EU and US Advance Bilateral Talks on AI, Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific European Commission Technology Chief Visits Washington for AI, Cyber Discussions Chris...
Flaw in Wi-Fi Standard Can Enable SSID Confusion Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Pawel Michalowski via Shutterstock Researchers at Belgium’s KU Leuven discovered a fundamental design flaw in the IEEE...
Palo Alto Networks and IBM to Jointly Provide AI-Powered Security Offerings – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SANTA CLARA, Calif. and ARMONK, N.Y., May 15, 2024 /PRNewswire/ — Palo Alto Networks (NASDAQ: PANW), the global cybersecurity leader, and IBM (NYSE: IBM), a leading provider...
Notice of a Data Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WILLOW GROVE, Pa., May 14, 2024 /PRNewswire/ — On or around February 6, 2024, Hypertension-Nephrology Associates, P.C. (“the Practice”) became aware it was the...
Scammers Fake DocuSign Templates to Blackmail & Steal From Companies – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Andrea Danti via Alamy Stock Photo Phishing emails mimicking DocuSign are rising, thanks to a thriving underground...
FBI, DoJ Shut Down BreachForums, Launch Investigation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Convery flowers via Alamy Stock Photo On the morning of May 15, the FBI seized...
D-Link Routers Vulnerable to Takeover Via Exploit for Zero-Day – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: KsanderDN via Shutterstock Researchers have released an exploit for a zero-day security flaw in a family of...
3 Tips for Becoming the Champion of Your Organization’s AI Committee – Source: www.darkreading.com
Source: www.darkreading.com – Author: Matan Getz Matan Getz, CEO & Co-Founder, Aim Security May 15, 2024 5 Min Read Source: marcos alvarado via Alamy Stock Photo...
Smashing Security podcast #372: The fake deepfake, and Estate insecurity – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Remember when a US mother was accused of distributing explicit deepfake photos and videos to try to get her teenage...
How to Set Up & Use a VPN on Android (A Step-by-Step Guide) – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Nicole Rennolds We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
What Is the Dark Web? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: The negative press, coupled with YouTube horror stories, has cemented the Dark Web’s reputation for illicit behavior. Today, the Dark Web is...
Quick Glossary: DevSecOps – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: The way software is developed has changed. DevSecOps is transforming the industry by incorporating security from the early stages and automating traditional...
5 key takeaways for CISOs, RSA Conference 2024 – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Last week, over 40,000 business and cyber security leaders converged at the Moscone Center in San Francisco to attend...
Why Is Hardware More Secure than Software? – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team The underlying differences between hardware and software when implementing critical cryptosystems. By Kimmo Järvinen, Co-founder and CTO, Xiphera The majority...
The Fusion of Fraud and IAM: An Event with Transmit Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Editor Next week our founder Simon Moffatt will be speaking at an event in London with leading customer identity and access management...
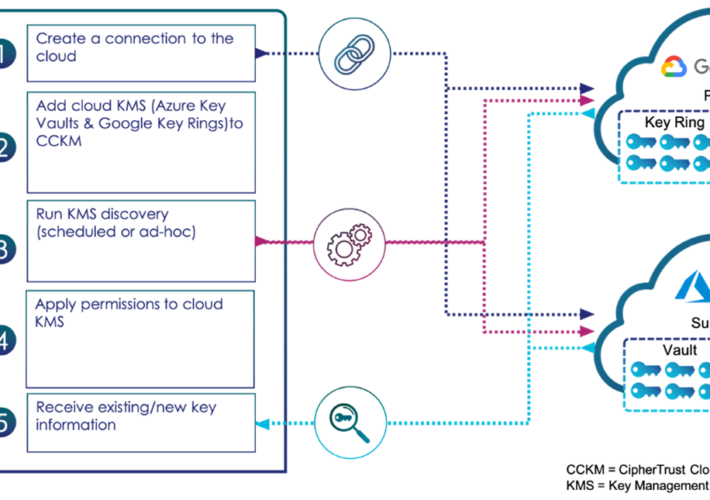
Systematically Bring to Light the Keys in Your Clouds – Source: securityboulevard.com
Source: securityboulevard.com – Author: madhav Systematically Bring to Light the Keys in Your Clouds madhav Wed, 05/15/2024 – 10:23 The cloud has enabled organizations to create...
Thunderbird Vulnerabilities Fixed in Ubuntu and Debian – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rohan Timalsina In recent Ubuntu and Debian security updates, several vulnerabilities have been addressed in Thunderbird, the popular open-source mail and newsgroup...
5 Must-Haves to Get (and Stay) Compliant With Privacy and Security Frameworks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Adar Givoni, Director of Compliance, Scytale Achieving and maintaining compliance with data privacy and security frameworks is a complex undertaking that requires...
How an Intrusion Detection System Can Ensure End-User Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: TuxCare Team It’s never been more important for businesses to invest in the best security measures available to them. Hackers and cybercriminals...