Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Schneider Electric; Siemens Energy; the University of California, Los Angeles (UCLA); Werum, a pharmaceutical technology provider; and...
Day: June 27, 2023
Mockingjay Slips By EDR Tools With Process Injection Technique – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Endpoint detection and response (EDR) systems have become increasingly efficient at detecting typical process injection attempts...
Trans-Rights Hacktivists Steal City of Ft. Worth’s Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In a security breach first discovered on June 23, Fort Worth, a north Texas city that has more...
Pilot Applicant Information for American, Southwest Hacked – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Hackers breached a database maintained by Pilot Credentials, a recruiting company based in Austin, Texas, resulting...
Most Enterprise SIEMs Blind to MITRE ATT&CK Tactics – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Despite enterprises’ best efforts to shore up their security information and event management (SIEM) postures, most platform...
Why the FDA’s SBOM Mandate Changes the Game for OSS Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jenn Gile, Head of Product Marketing, F5 NGINX The US Food and Drug Administration (FDA) is not exactly top of mind for...
Why Cyber Funding Flows for Rural Water Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A recent bill that proposes $7.5 million in annual cybersecurity funding for the next five years...
Preventing Cyberattacks on Schools Starts With K–12 Cybersecurity Education – Source: www.darkreading.com
Source: www.darkreading.com – Author: Laurie Salvail, Executive Director, CYBER.ORG Our K–12 schools are under cyberattack. From 2016 to 2022, public K–12 schools in the United States...
Suncor Energy Cyberattack Impacts Petro-Canada Gas Station Payment Operations – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici After parent company Suncor Energy revealed they were the target of a cyberattack, customers at Petro-Canada gas stations across Canada...
45,000 NYC Public School Students’ Data Stolen in MOVEit Breach – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici According to the New York City Department of Education (NYC DOE), threat actors broke into the NYC DOE’s MOVEit Transfer...
SEC notice to SolarWinds CISO and CFO roils cybersecurity industry – Source: www.csoonline.com
Source: www.csoonline.com – Author: US SEC staff have recommended legal action against individual SolarWinds employees, in an unusual move that is causing a stir among cybersecurity...
Fortanix adds confidential data search for encrypted enterprise data – Source: www.csoonline.com
Source: www.csoonline.com – Author: Fortanix Confidential Data Search supports scalable searches in encrypted databases with sensitive data, without compromising data security or privacy regulations. Cloud data...
Bionic integrations offer context-based vulnerability management – Source: www.csoonline.com
Source: www.csoonline.com – Author: Bionic Signals and Bionic Business Risk Scores are being added to Bionic’s Application security posture management platform for context-based risk prioritization. Application...
New Android banking trojan targets US, UK, and Germany – Source: www.csoonline.com
Source: www.csoonline.com – Author: The threat actors are distributing their malware via the Play Store, and already had over 30,000 installations as of March. An ongoing...
Fileless attacks surge as cybercriminals evade cloud security defenses – Source: www.csoonline.com
Source: www.csoonline.com – Author: Threat actors are concealing campaigns to evade detection and establish stronger footholds in compromised systems. Irga-igra / ConnectVector / Shutterstock The number...
Survey reveals mass concern over generative AI security risks – Source: www.csoonline.com
Source: www.csoonline.com – Author: Malwarebytes survey reveals 81% of people are concerned about the security risks posed by ChatGPT and generative AI, while just 7% think...
BrandPost: Effective security training programs are vital to creating a cyber-aware workforce – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | CISOs today face an expanding attack surface, increasingly threats, and a cybersecurity skills gap. An integrated and automated approach to...
Extortion Group Clop’s MOVEit Attacks Hit 108 Victims – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance & Risk Management Known Victims Now Include New York City...
Army Alert on Free Smartwatches: Don’t Sport These Wearables – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social Engineering Malware-Infected Watches Are the New USB Thumb Drive for...
Critical Vendor Risk Considerations for AI Use in Healthcare – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development Damian Chung of Netskope on...
Socure Buys Berbix for $70M to Fortify Identity Verification – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Device Identification , Endpoint Security Buying Document Verification Startup Berbix Will Make Socure Faster, More Accurate Michael Novinson (MichaelNovinson) • June...
Live Webinar | A Master Class on IT Security: Roger Grimes Teaches You Phishing Mitigation – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Account Takeover Fraud , ACH Fraud , Analytics Presented by KnowBe4 60 mins Phishing attacks have come...
Chinese APT Group Uses New Tradecraft to Live Off the Land – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government Group Targeting Transportation, Construction, Government Agencies, CrowdStrike Says Anviksha More...
Achieving Zero Trust That Works – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anudeep Parhar What’s the secret to overcoming common roadblocks when implementing Zero Trust The concept of Zero Trust dates back more than...
Essential 8 Maturity Model: Achieving Cyber Security Excellence – Source: securityboulevard.com
Source: securityboulevard.com – Author: Scytale The Essential 8 Maturity Model is quickly rising in rank and is known for helping businesses establish the baseline of cyber...
Protecting Confidential Documents: The Power of Hidden Anti-Leak Marks – Source: securityboulevard.com
Source: securityboulevard.com – Author: LeaksID We had a conversation with Sergey Voynov, CEO of G-71, regarding his perspective on additional means of document protection. It is...
BSidesSF 2023 – Wilson Tang – Using Machine Learning To Detect Sensitive Documents On SharePoint – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Your Shopping List for Security & Privacy Program Essentials – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richa Tiwari Whether your org is about to begin its journey for SOC 2, or you’re planning to wrangle up more standards...
ARMO achieves SOC 2 certification: strengthening security and trust – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ben Hirschberg We are thrilled to announce that ARMO, the makers of Kubescape and ARMO Platform, has successfully obtained the SOC 2...
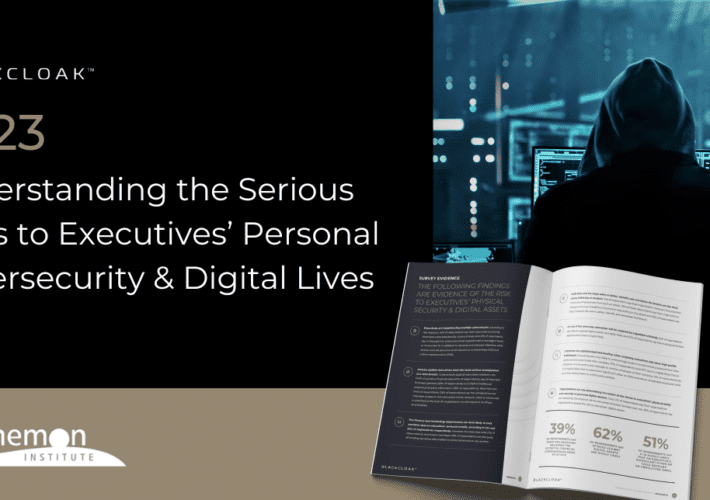
The Unsung Heroes: Security Teams Grappling with Personal Cyber Threats to Executives – Source: securityboulevard.com
Source: securityboulevard.com – Author: Leigh Dow In a world that is more connected than ever, cybersecurity has become a fundamental aspect of any business. With every...