Source: www.databreachtoday.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy LIBE Committee Hears From Heads of UK and Irish...
Day: May 24, 2023
Breach Alert! Rheinmetall AG Confirms Being Hit by BlackBasta Ransomware Attack – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Rheinmetall AG announced they suffered a data breach after being a target of a BlackBasta ransomware attack. On May 20th,...
Almost 300k People Affected by Ransomware Attack on Dish Network – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici Dish Network reported a data breach subsequent to the ransomware attack in February and started the process of notifying the...
Digital security for the self‑employed: Staying safe without an IT team to help – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Phil Muncaster Nobody wants to spend their time dealing with the fallout of a security incident instead of building up their business...
Android app breaking bad: From legitimate screen recording to file exfiltration within a year – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Lukas Stefanko ESET researchers discover AhRat – a new Android RAT based on AhMyth – that exfiltrates files and records audio ESET...
ChatGPT and data: Everything you need to know
Since OpenAI unleashed ChatGPT onto the world, opinion has been split between those who believe it will radically improve the way we live and work and...
Hackers attempt to sell personal data of 1.5 million women
The personal information of more than 1.5 million women has been put up for sale on the dark web following an alleged data breach of Indian...
US Sanctions North Korean University for Training Hackers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Department of the Treasury on Tuesday announced sanctions against four entities and one individual for engaging in malicious...
New Honeywell OT Cybersecurity Solution Helps Identify Vulnerabilities, Threats – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Honeywell on Tuesday announced the launch of a new OT cybersecurity solution designed to help organizations identify vulnerabilities and threats...
White House Unveils New Efforts to Guide Federal Research of AI – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press The White House on Tuesday announced new efforts to guide federally backed research on artificial intelligence as the Biden administration...
Virtual Event Today: Threat Detection and Incident Response Summit – Source: www.securityweek.com
Source: www.securityweek.com – Author: Mike Lennon Hi, what are you looking for? SecurityWeek Malware & Threats Join thousands of attendees as we dive into threat hunting...
Mikrotik Belatedly Patches RouterOS Flaw Exploited at Pwn2Own – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Latvian network equipment manufacturer MikroTik has shipped a patch for a major security defect in its RouterOS product and confirmed...
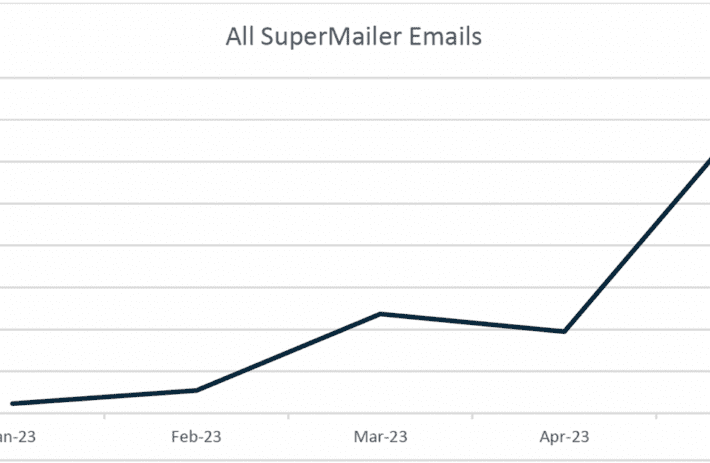
Threat Actor Abuses SuperMailer for Large-scale Phishing Campaign – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend A credential phishing campaign using the legitimate SuperMailer newsletter distribution app has doubled in size each month since January 2023....
New ‘GoldenJackal’ APT Targets Middle East, South Asia Governments – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire An advanced persistent threat (APT) actor named GoldenJackal has been targeting government and diplomatic entities in the Middle East and...
Iranian Hackers Using New Windows Kernel Driver in Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Iranian threat actors have been using a newly identified Windows kernel driver in attacks against Middle East targets since 2020,...
Google Launches Bug Bounty Program for Mobile Applications – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Google this week introduced Mobile VRP (vulnerability rewards program), a new bug bounty program for reporting vulnerabilities found in the...
Rheinmetall Says Military Business Not Impacted by Ransomware Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs German car parts and defense company Rheinmetall has confirmed being targeted in a cyberattack by a known ransomware group, but...
Windows Copilot: Your new AI assistant for Windows 11 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar In a significant development for the PC platform, Microsoft has introduced Windows Copilot, marking a milestone as the first PC...
GoldenJackal state hackers silently attacking govts since 2019 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Image: Bing Create A relatively unknown advanced persistent threat (APT) group named ‘GoldenJackal’ has been targeting government and diplomatic entities...
Windows 11 getting native support for 7-Zip, RAR, and GZ archives – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft is adding native support for RAR, 7-Zip, and GZ archives to an upcoming version of Windows 11 expected this...
New Microsoft PowerToy lets you control 4 PCs with one mouse, keyboard – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has updated PowerToys with two new tools that help control multiple Windows systems with the same keyboard/mouse and quickly...
Windows 11 KB5026436 fixes printing and audio playback issues – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has released the May 2023 optional cumulative update for Windows 11, version 21H2, with fixes for audio and printer...
US sanctions orgs behind North Korea’s ‘illicit’ IT worker army – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The Treasury Department’s Office of Foreign Assets Control (OFAC) announced sanctions today against four entities and one individual for their...
Arms maker Rheinmetall confirms BlackBasta ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas German automotive and arms manufacturer Rheinmetall AG confirms that it suffered a BlackBasta ransomware attack that impacted its civilian business....
Dell’s Project Helix heralds a move toward specifically trained generative AI – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Image: Supatman/Adobe Stock Generative artificial intelligence is at a pivotal moment. Enterprises want to know how to take advantage of...
Microsoft Dataverse: Going from Excel to new AI-powered tools – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Mary Branscombe Image: stnazkul/Adobe Stock Microsoft Excel is the original low-code tool, but data and business logic in an Excel spreadsheet are...
Google Adds Guardrails to Keep AI in Check – Source: www.darkreading.com
Source: www.darkreading.com – Author: Agam Shah, Contributing Writer GOOGLE I/O 2023, MOUNTAIN VIEW, CALIF. — Sandwiched between major announcements at Google I/O, company executives discussed guardrails...
SuperMailer Abuse Bypasses Email Security for Super-Sized Credential Theft – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A high-volume credential-harvesting campaign is using a legitimate email newsletter program named SuperMailer to blast...
What Security Professionals Need to Know About Aggregate Cyber Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tiago Henriques, Vice President of Research, Coalition Risk aggregation is not a new phenomenon. The insurance industry has examined how shared assets...
FBI: Human Trafficking Rings Force Job Seekers Into Cryptojacking Schemes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The FBI is warning US citizens that are traveling to or living abroad in Southeast Asia of...