Source: www.techrepublic.com – Author: Cedric Pernet Image: Getty Images/iStockphoto Several ransomware groups and state-sponsored cyberespionage threat actors are exploiting a vulnerability affecting printing software tools PaperCut...
Day: May 17, 2023
Top 10 facial recognition software vendors for 2023 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Franklin Okeke Image: Alexander/Adobe Stock Biometric security technologies such as facial recognition, are becoming more sophisticated due to the rise in cybersecurity...
Transform Any Place into a Smart Space – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Transform rooms, buildings, and spaces into assets that inform new insights, inspire collaboration, and drive efficiencies through automation and analytics. With our...
Monitoring the dark web to identify threats to energy sector organizations – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Searchlight Cyber researchers warn of threat actors that are offering on the dark web access to energy sector organizations. Dark...
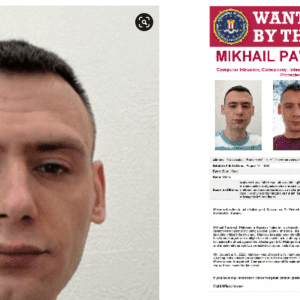
US Gov offers a $10M reward for a Russian ransomware actor – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The US government is offering a $10M reward for Russian national Mikhail Pavlovich Matveev (30) charged for his role in...
Multiple flaws in Teltonika industrial cellular router expose OT networks to hack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts found multiple vulnerabilities in Teltonika industrial cellular routers that could expose OT networks to cyber attacks. A joint analysis...
University admission platform Leverage EDU exposed student passports – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The popular university admission platform Leverage EDU leaked almost 240,000 sensitive files, including students’ passports, financial documents, certificates, and exam...
Lacroix Group shut down three facilities after a ‘targeted cyberattack’ – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini French electronics manufacturer Lacroix Group shut down three plants after a cyber attack, experts believe it was the victim of...
U.S. Transportation Department Breach Exposes Data of 237,000 Employees – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși The US Department of Transportation (USDOT) recently revealed threat actors breached its system in a cyberattack. The data breach compromised...
UNC3944 Uses Azure Serial Console for Stealthy Access to Virtual Machines – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Researchers revealed that the UNC3944 threat actors use phishing and SIM-swapping attacks to get control over Microsoft Azure admin accounts....
Capita Recommends Its Customers to Assume Their Data Was Stolen – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici At the end of March, a cyberattack affected Capita’s systems, resulting in the theft of customer data. Six weeks after...
No more macros? No problem, say miscreants, we’ll adapt – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Microsoft’s decision to block internet-sourced macros by default last year is forcing attackers to find new and creative ways to compromise...
Cybercriminals have adapted since Microsoft’s decision to block macros – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Microsoft’s decision to disable macros by default has resulted in “vastly different … attack chains” from cybercriminals and a “new normal...
CISO anxiety returns amid heightened concern of material cyberattacks – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Dive Brief: After a year of relative calm, more than two-thirds of CISOs across the globe are concerned about a material...
Cybersecurity stress returns after a brief calm: Proofpoint report – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Sixty-eight percent of CISOs globally fear a cyberattack in the next 12 months, up by over 40% year over year and...
Getting a Tighter Grip on Supply Chain Security Risk – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 3rd Party Risk Management , Events , Governance & Risk Management Proofpoint CEO Ashan Willy on Ways to Identify Third-Party Compromises...
Access to Energy Sector ICS/OT Systems Offered on Hacker Forums – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Threat actors have been offering access to energy sector organizations, including industrial control systems (ICS) and other operational technology (OT)...
4 Countries Join NATO Cyber Defense Center – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The NATO Cooperative Cyber Defence Centre of Excellence (CCDCOE) announced on Wednesday that four countries have joined as members: Ukraine,...
Apple Blocked 1.7 Million Applications From App Store in 2022 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Apple this week announced that it blocked 1.7 million applications from being published in the App Store in 2022. The...
Critical Infrastructure Organizations Warned of BianLian Ransomware Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), and the Australian Cyber Security Centre...
Entro Raises $6M to Tackle Secrets Sprawl – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Israeli startup Entro has attracted investor interest in technology aimed at helping businesses manage and secure secrets like API keys,...
Lacroix Closes Production Sites Following Ransomware Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Technological equipment giant Lacroix Group says it has closed three production sites for the week after experiencing a ransomware attack....
Cybersecurity M&A Roundup for May 1-15, 2023 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Seventeen cybersecurity-related merger and acquisition (M&A) deals were announced in the first half of May 2023. An analysis conducted by...
Chrome 113 Security Update Patches Critical Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Google this week announced the release of a Chrome 113 security update that resolves a total of 12 vulnerabilities, including...
US Offering $10M Reward for Russian Man Charged With Ransomware Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Mikhail Pavlovich Matveev, a 30-year-old Russian national, has been charged by the US Justice Department for his alleged role in...
Is this the answer to Google Drive spam? – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Last week I received an unsolicited email from someone called Emma. She works for a “language learning app”, and said...
ChatGPT’s Chief Testifies Before Congress, Calls for New Agency to Regulate Artificial Intelligence – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press The head of the artificial intelligence company that makes ChatGPT told Congress on Tuesday that government intervention “will be critical...
Google is going to delete your data forever, if you haven’t logged into your account for two years – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley A new blog post by Google describes their new policy on dealing with inactive accounts – and it’s an important...
Surprise! Elon Musk’s encrypted Twitter DMs feature will cost you dear – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Elon Musk may have fired many of the staff in Twitter’s Trust & Safety division after purchasing the company in...
IBM Acquires Polar Security for Data Security Posture Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard IBM this week acquired Polar Security to add a data security posture management platform to its cybersecurity portfolio. Kevin Skapinetz,...