Source: www.bleepingcomputer.com – Author: Bill Toulas The Phishing-as-a-Service (PhaaS) platform named ‘Greatness’ has seen a spike in activity as it targets organizations using Microsoft 365 in...
Day: May 10, 2023
The Industrywide Consequences of Making Security Products Inaccessible – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ross Haleliuk , Product Leader and Head of Product, LimaCharlie When you look at the cybersecurity vendor market, it’s hard not to...
Microsoft Digital Defense Report: Trends In Device and Infrastructure Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Cybersecurity is ever-evolving. That‘s why Microsoft tracks intelligence from trillions of daily security signals to gain insight into what...
Free Tool Unlocks Some Encrypted Data in Ransomware Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Good news for ransomware victims: Researchers have released a free tool on GitHub that they say...
New Startup SquareX Targets Brower-Based Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Startup SquareX emerges from stealth with plans for a “disposable browser” for users to access the Internet...
Keeper Security Announces Minority Growth Equity Investment From Summit Partners – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 CHICAGO, May 9, 2023 /PRNewswire/ — Keeper Security (“Keeper” or the “Company”), a leading provider of zero-trust and zero-knowledge cybersecurity software, today announced that global...
Microsoft Patches 2 Zero-Day Vulnerabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Microsoft’s security update for May 2023 is the lightest in volume since August 2021 with fixes...
Apple ID: 3 things to remember when changing this password – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Erik Eckel Image: ink drop/Adobe Stock When changing your Apple ID password — and you are changing your Apple account security passcode...
Proofpoint’s 2023 Voice of the CISO Report Reveals Nearly Two-Thirds of CISOs have had to Deal with the Loss of Sensitive Data in the Past 12 Months – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 82% of CISOs believe employees leaving the organization contributed to the data loss incident, a challenge exacerbated by staff turnover SUNNYVALE,...
Proofpoint’s 2023 Voice of the CISO Report Reveals Nearly Two-Thirds of CISOs have had to Deal with the Loss of Sensitive Data in the Past 12 Months – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 82% of CISOs believe employees leaving the organization contributed to the data loss incident, a challenge exacerbated by staff turnover SUNNYVALE,...
Microsoft Patch Tuesday, May 2023 Edition – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Microsoft today released software updates to fix at least four dozen security holes in its Windows operating systems and other software,...
Feds Take Down 13 More DDoS-for-Hire Services – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs The U.S. Federal Bureau of Investigation (FBI) this week seized 13 domain names connected to “booter” services that let paying customers...
Alert: NextGen Data Breach Puts 1 Million User Identities at Risk – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu NextGen Healthcare, a U.S.-based provider of electronic health record software, notified its clients that threat actors breached its systems and...
Patch Tuesday May 2023 – Microsoft Slates for Release 11 Security Fixes for Edge Browser Vulnerabilities – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Vladimir Unterfingher Heimdal® returns with yet another rendition of its monthly Patch Tuesday updates. Our May edition includes security releases for vulnerabilities...
PIPEDREAM Malware against Industrial Control Systems – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Another nation-state malware, Russian in origin: In the early stages of the war in Ukraine in 2022, PIPEDREAM, a known...
Are your employees missing these social engineering red flags? – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Social engineering is one of the most significant and difficult network security challenges to contend with. Due to the...
Unconsidered benefits of a consolidation strategy every CISO should know – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Pete has 32 years of Security, Network, and MSSP experience and has been a hands-on CISO for the last 17 years...
MY TAKE: DigiCert and Oracle partner to extend digital trust and scalable infrastructure globally – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido One meeting I had at RSA Conference 2023, was a briefing about a new partnership, announced this...
The global food distribution giant Sysco discloses a data breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Sysco, the global food distribution giant, disclosed a data breach, the compromised data includes customer and employee data. Sysco Corporation is...
A Linux NetFilter kernel flaw allows escalating privileges to ‘root’ – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A Linux NetFilter kernel flaw, tracked as CVE-2023-32233, can be exploited by unprivileged local users to escalate their privileges to...
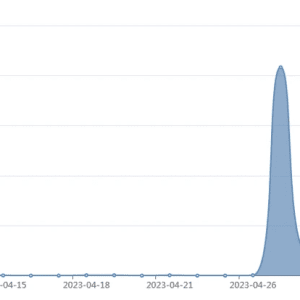
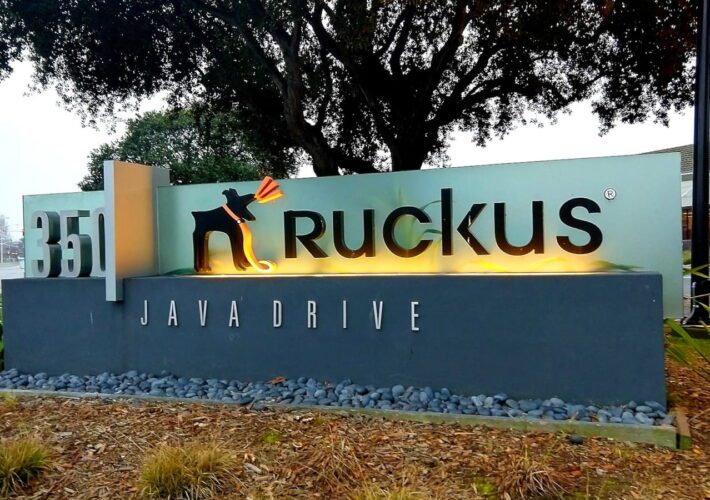
Fortinet warns of a spike of the activity linked to AndoryuBot DDoS botnet – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A DDoS botnet dubbed AndoryuBot has been observed exploiting an RCE, tracked as CVE-2023-25717, in Ruckus access points. FortiGuard Labs...
FBI seized 13 domains linked to DDoS-for-hire platforms – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The U.S. DoJ announced the seizure of 13 new domains associated with DDoS-for-hire platforms as part of Operation PowerOFF. The...
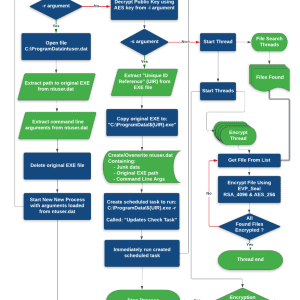
New CACTUS ransomware appeared in the threat landscape – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers warn of a new ransomware family called CACTUS that exploits known vulnerabilities in VPN appliances to gain initial access...
Iran-linked APT groups started exploiting Papercut flaw – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Microsoft warns of Iran-linked APT groups that are targeting vulnerable PaperCut MF/NG print management servers. Microsoft warns that Iran-linked APT...
ESET APT Activity Report Q4 2022–Q1 2023 – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Jean-Ian Boutin An overview of the activities of selected APT groups investigated and analyzed by ESET Research in Q4 2022 and Q1 2023 ESET...
How the war in Ukraine has been a catalyst in private‑public collaborations – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: André Lameiras As the war shows no signs of ending and cyber-activity by states and criminal groups remains high, conversations around the...
GitHub now auto-blocks token and API key leaks for all repos – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan GitHub is now automatically blocking the leak of sensitive information like API keys and access tokens for all public code...
Spanish police dismantle phishing operation linked to crime ring – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The National Police of Spain have arrested two hackers, 15 members of a criminal organization, and another 23 people involved...
Critical Ruckus RCE flaw exploited by new DDoS botnet malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new malware botnet named ‘AndoryuBot’ is targeting a critical-severity flaw in the Ruckus Wireless Admin panel to infect unpatched...
Food distribution giant Sysco warns of data breach after cyberattack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Sysco, a leading global food distribution company, has confirmed that its network was breached earlier this year by attackers who...