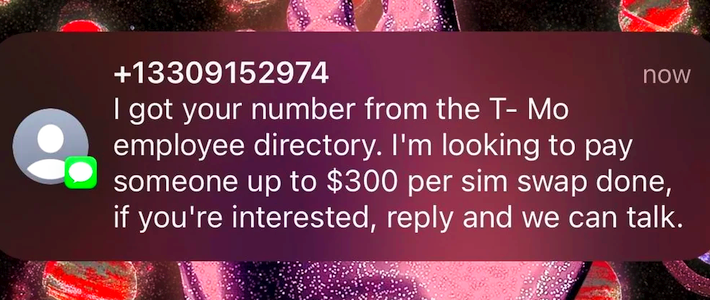
Source: securityboulevard.com - Author: Richi Jennings Widespread spam targets carrier employees, as scrotes try harder to...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
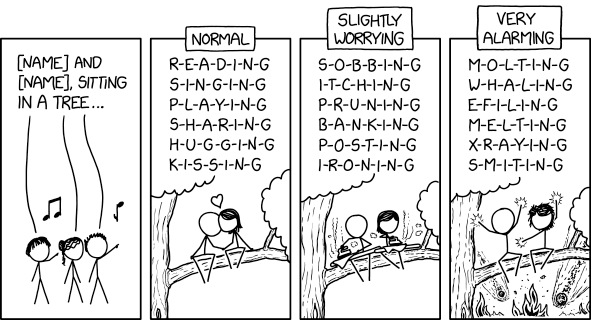
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This...
Source: securityboulevard.com - Author: Jeffrey Burt Mental telehealth startup Cerebral says it will stop sharing sensitive...
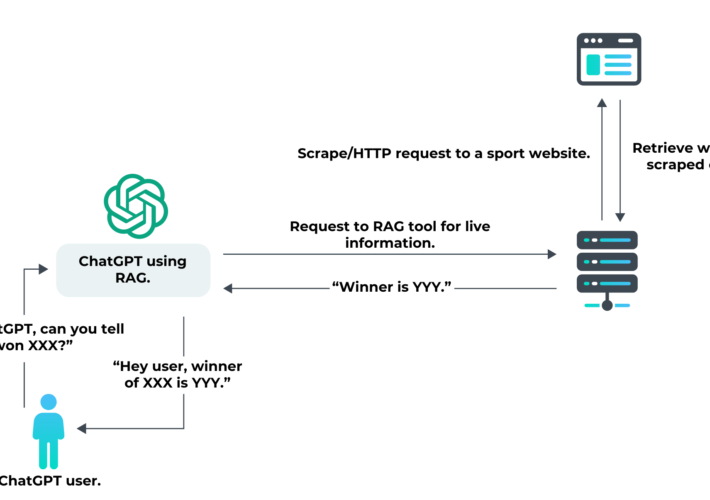
Source: securityboulevard.com - Author: Antoine Vastel Generative AI tools like ChatGPT have worked to solve the...
Source: securityboulevard.com - Author: Team Nuspire Strong detection and response capabilities are pivotal for identifying and...
Source: securityboulevard.com - Author: Dana Epp Is Bruno any good for API hacking? That’s been a...
Source: securityboulevard.com - Author: Erez Hasson Bad bots continue to affect consumers and organizations across all...
Source: securityboulevard.com - Author: Riddika Grover Cyber attacks have become increasingly prevalent. This has caused significant...
Source: securityboulevard.com - Author: Shriram Sharma RSA Conference 2024, taking place at San Francisco’s Moscone Center...
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido San Francisco, Calif. — The amazing digital...
Source: securityboulevard.com - Author: Jeffrey Burt Almost 600,000 Roku customers had their accounts hacked through two...
Source: securityboulevard.com - Author: Kevin Smith As a managed service provider (MSP), you are tasked with...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: *Andrew Searles, Yoshimichi Nakatsuka, Ercan Ozturk, Andrew Paverd, Gene...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Michael Vizard Zscaler plans to acquire Airgap Networks to apply network segmentation...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
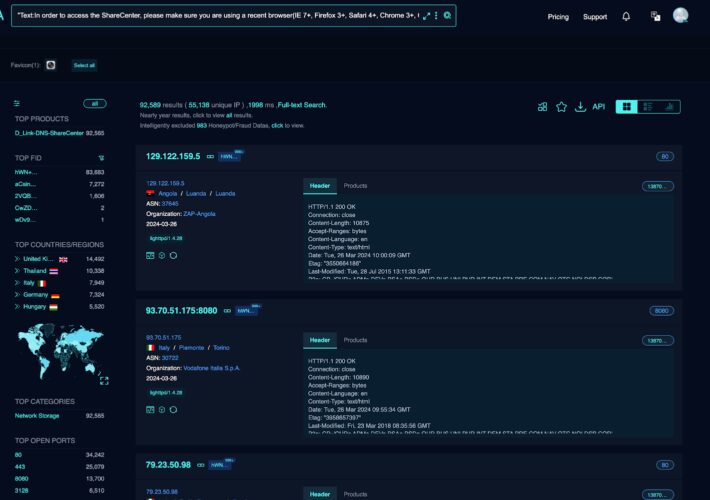
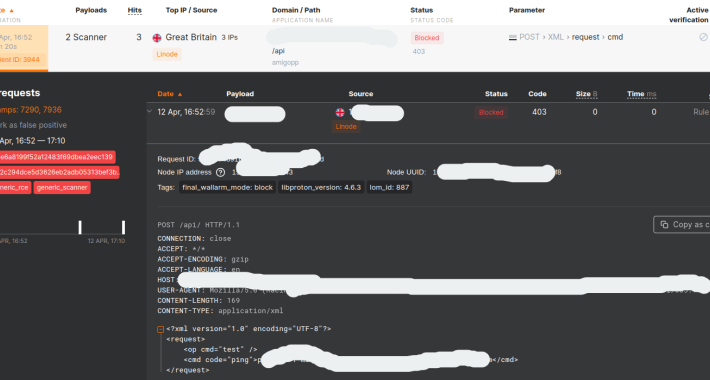
Source: securityboulevard.com - Author: wlrmblog On Friday April 12, Palo Alto disclosed that some versions of...
Source: securityboulevard.com - Author: Shikha Dhingra Web application security testing aims to detect, prevent, and address...
Source: securityboulevard.com - Author: Enzoic CISA issued a fresh CISA emergency directive in early April instructing...
Source: securityboulevard.com - Author: Dragos Josanu XZ Utils is a collection of open-source command-line tools for...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Jeff Martin Just a few weeks ago, we wrote about how the...
Source: securityboulevard.com - Author: Roy Blit Understand how AI models add risk and how to address...
Source: securityboulevard.com - Author: Ryan Healey-Ogden In the case of the XZ breach, this backdoor could...
Source: securityboulevard.com - Author: Greg Bulmash There's been a lot of talk about SBOMs in tech...
Source: securityboulevard.com - Author: Aaron Fulkerson Generative AI (GenAI) technologies, especially large language models like OpenAI’s...
Source: securityboulevard.com - Author: Richi Jennings The analytics firm kept big organizations’ secrets in an insecure...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Jeffrey Burt Russian state-sponsored hackers who broke into Microsoft’s corporate email accounts...
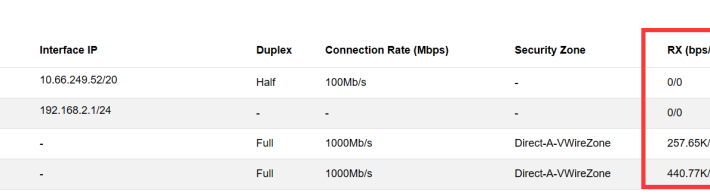
Source: securityboulevard.com - Author: NSFOCUS NIPS aims to accurately monitor abnormal network traffic, automatically blocking various...