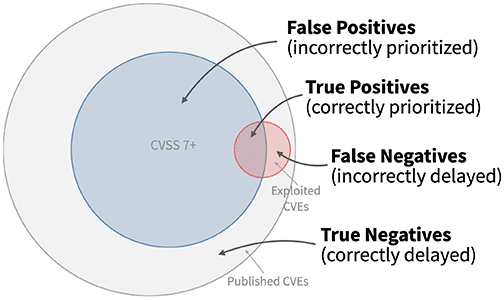
Source: securityboulevard.com - Author: Alexandra Aguiar The average vulnerability and patch management backlog now contains over...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
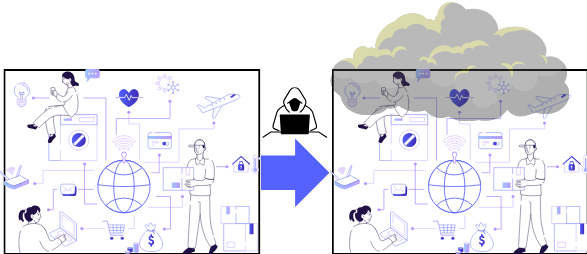
Source: securityboulevard.com - Author: NSFOCUS Today’s ever-evolving digital landscape presents unparalleled opportunities alongside formidable cybersecurity challenges,...
Source: securityboulevard.com - Author: Don Hoffman Last week, the BlackCat ransomware group (also known as ALPHV)...
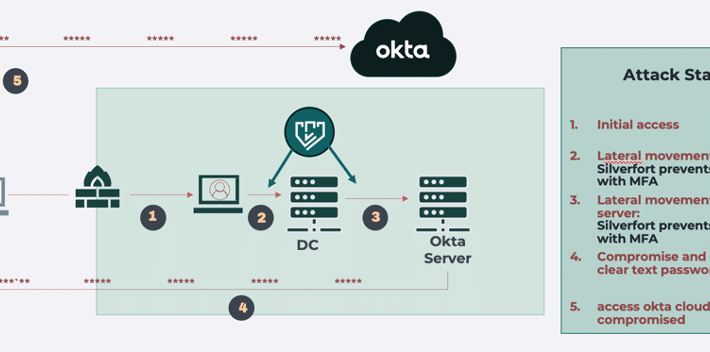
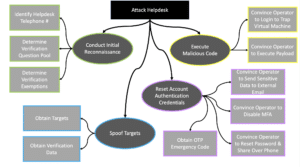
Source: securityboulevard.com - Author: emmaline Introduction As we have witnessed in recent weeks with the MGM...
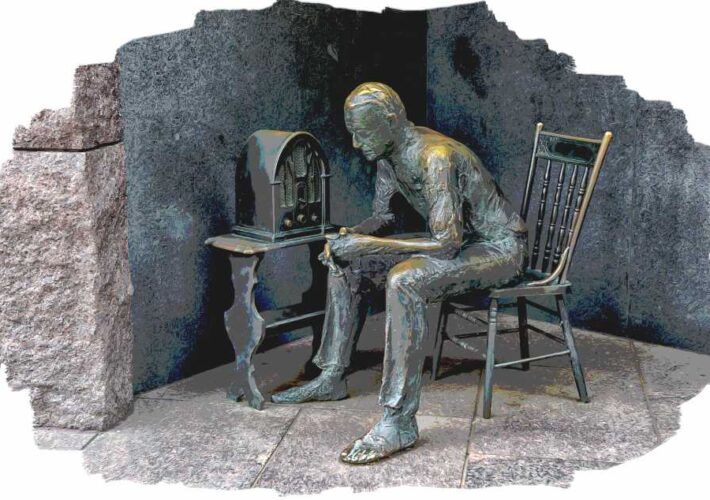
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
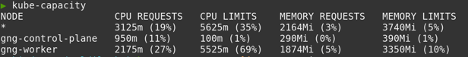
Source: securityboulevard.com - Author: Stevie Caldwell Platforms, sometimes called internal developer platforms, are a unified infrastructure...
Source: securityboulevard.com - Author: Michael Toback Introduction In today’s interconnected world, understanding the OWASP Top 10...
Source: securityboulevard.com - Author: Chris Needs New Product Release News You use the HYAS platform today...
Source: securityboulevard.com - Author: Aaron Linskens Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Joel Wong At Swimlane, “armor” takes on a distinct meaning. It represents...
Source: securityboulevard.com - Author: Heidi King Session will feature speaker from AWS Identity and explain how...
Source: securityboulevard.com - Author: rezilion What is SOC 2 compliance? What exactly does SOC 2 compliance...
Source: securityboulevard.com - Author: Paul Roberts One truism of the cybersecurity world is that attackers have...
Source: securityboulevard.com - Author: Team Nuspire An alarming security concern has arisen within the Juniper network...
Source: securityboulevard.com - Author: Michael Vizard A Barracuda Networks report published today suggests cybercriminals are becoming...
Source: securityboulevard.com - Author: Mark Knowles Remember the days when security was simple – or so...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Scott Wright Although no data is unimportant, there are different security or...
Source: securityboulevard.com - Author: bacohido By Byron V. Acohido Creating ever smarter security software to defend...
Source: securityboulevard.com - Author: Michael Toback Introduction: The Rising Importance of IoT in 2023 In the...
Source: securityboulevard.com - Author: Natalie Anderson Apptega, the end-to-end GRC platform for forward-thinking IT and managed service...
Source: securityboulevard.com - Author: Jeffrey Burt Affiliates of the Russia-linked LockBit ransomware group are using remote...
Source: securityboulevard.com - Author: Alan Shimel Speaker 1: This is Techstrong TV. Alan Shimel: Hey everyone....
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Mitchell Ashley Speaker 1: This is Techstrong TV. Mitch Ashley: Hey, everybody,...
Source: securityboulevard.com - Author: Casey Joyce Phishing attacks have long been a major concern in the...
Source: securityboulevard.com - Author: Michael Toback Introduction In today’s rapidly evolving digital landscape, the surge of...
Source: securityboulevard.com - Author: Michael Vizard At its Fal.Con 2023 conference, CrowdStrike made a host of...
Source: securityboulevard.com - Author: Tony Bradley TechSpective Podcast Episode 116 Getting hacked sucks in all...