Source: securityboulevard.com - Author: Michael Toback Introduction In today’s rapidly evolving digital world, the significance of...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Richi Jennings Egyptian opposition presidential candidate Ahmed Eltantawy targeted “by the government.”Would-be president...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author As more and more businesses...
Source: securityboulevard.com - Author: Ken Palla Trust is the currency we trade for success in a...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Nik Hewitt The ROI of microsegmentation is undeniable for optimal business security...
Source: securityboulevard.com - Author: SafeBreach As the pioneer in breach and attack simulation (BAS), SafeBreach launched...
Source: securityboulevard.com - Author: Michael Toback Introduction The concept of “BYOD Policy for Small Business” is...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity Every organization has behaviors they are trying to discourage...
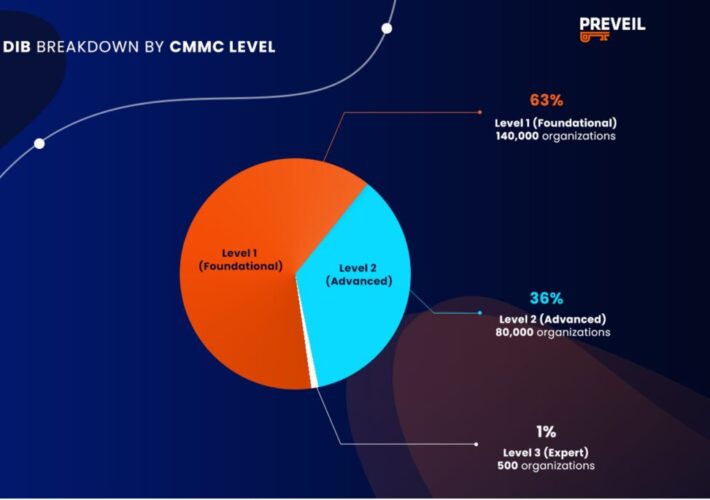
Source: securityboulevard.com - Author: Orlee Berlove, reviewed by Noël Vestal, PMP, CMMC RP The Department of...
Source: securityboulevard.com - Author: hrbrmstr Rite-Aid closed 60+ stores in 2021. They said they’d nuke over...
Source: securityboulevard.com - Author: Michael Toback Introduction The convergence of the Internet of Things (IoT) and...
Source: securityboulevard.com - Author: Amy Luby Are you ready for the MSP event of the year?...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
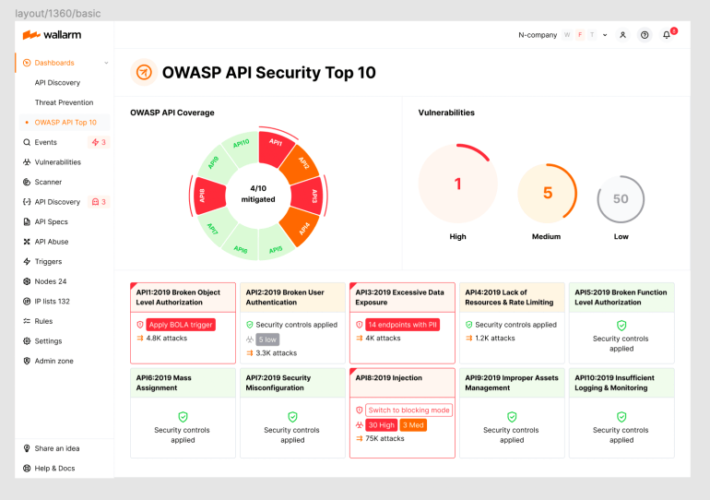
Source: securityboulevard.com - Author: wlrmblog Welcome to the 10th post in our weekly series on the...
Source: securityboulevard.com - Author: Team Solvo Cloud computing has become essential for modern business operations, offering...
Source: securityboulevard.com - Author: Kimberly Rose The advent of DevOps—short for Development and Operations—provided an efficient...
Source: securityboulevard.com - Author: Rajan Sodhi In the dynamic realm of IT infrastructure and network management,...
Source: securityboulevard.com - Author: Michael Toback Introduction In today’s interconnected world, the significance of cybersecurity cannot...
Source: securityboulevard.com - Author: BrianKrebs The password manager service LastPass is now forcing some of its...
Source: securityboulevard.com - Author: Chris Garland The threat landscape for healthcare organizations has shifted tremendously since...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: David Lindner, Director, Application Security Insight #1 There will always be a...
Source: securityboulevard.com - Author: Jeffrey Burt The Chinese government is accusing the United States intelligence community...
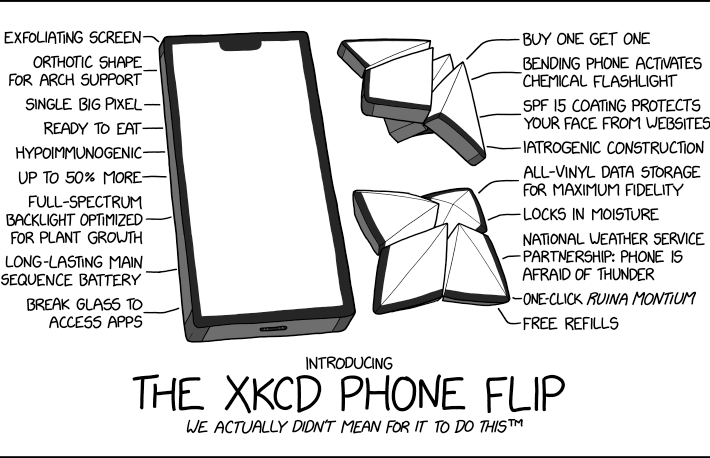
Source: securityboulevard.com - Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Chris Garland Does your organization access CJIS? If so, the deadline for...
Source: securityboulevard.com - Author: Votiro Team Digital footprints are expanding at an unprecedented rate, with individuals...
Source: securityboulevard.com - Author: Don Hoffman As cyber threats continue to evolve and become more sophisticated,...