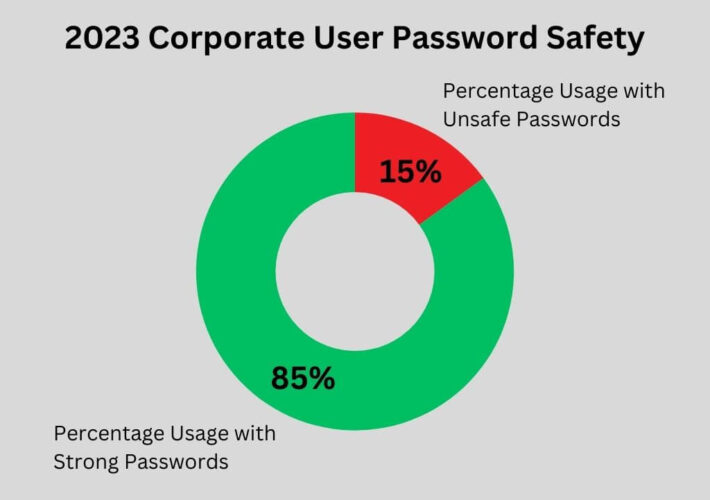
Source: securityboulevard.com - Author: Enzoic The 2023 data from Enzoic for Active Directory Lite (also known...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Ahona Rudra Reading Time: 5 min Your email is one of the...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: cyberwire New York, U.S.A., January 22nd, 2024, Cyberwire Memcyco will showcase its...
Source: securityboulevard.com - Author: Jeffrey Burt A Chinese espionage group spotted last year by Mandiant researchers...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author Account takeover – also referred...
Source: securityboulevard.com - Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security...
Source: securityboulevard.com - Author: Chris Pierson The importance of data privacy continues to grow exponentially. We...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity The 54th Annual Meeting of The World Economic Forum...
Source: securityboulevard.com - Author: girishwallarm In today’s complex digital landscape, the security of APIs has become...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Vivek Nair, Wenbo Guo, Justus Mattern, Rui Wang, James...
Source: securityboulevard.com - Author: Gary Warner The Crypto Launderers: Crime and Cryptocurrencies from the Dark Web...
Source: securityboulevard.com - Author: Avast Blog I consider myself pretty savvy when it comes to protecting...
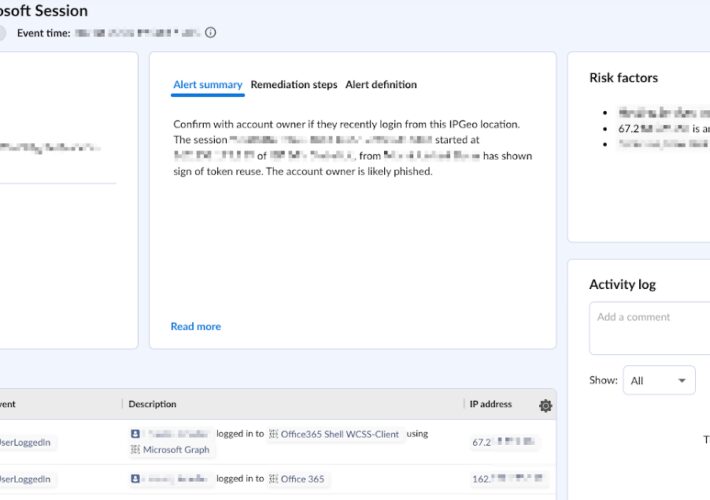
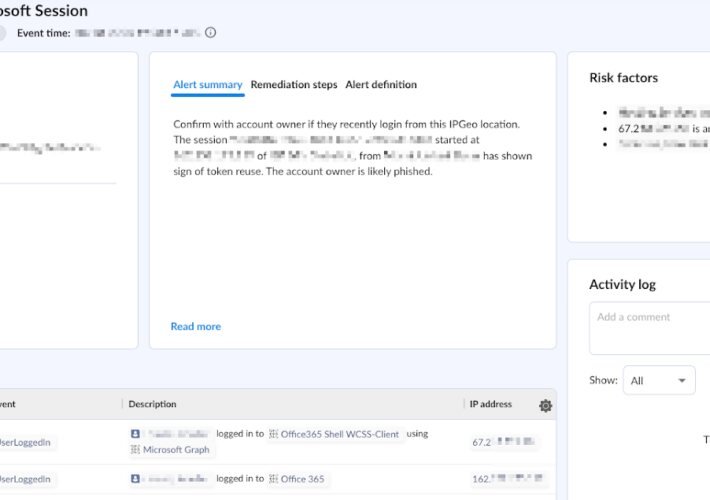
Source: securityboulevard.com - Author: Lila Joy Ginsberg Pass-The-Cookie (PTC), also known as token compromise, is a...
Source: securityboulevard.com - Author: Lila Joy Ginsberg In a world of evolving SaaS security threats, organizations...
Source: securityboulevard.com - Author: Cole Grolmus Quick, how many publicly traded cybersecurity companies are there? Take...
Source: securityboulevard.com - Author: Branden Williams Breaches are never ending, and if you have not already...
Source: securityboulevard.com - Author: Farah Iyer Pass-The-Cookie (PTC), also known as token compromise, is a common...
Source: securityboulevard.com - Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security...
Source: securityboulevard.com - Author: Andrew Hendry Challenge: Sophisticated Bots Are Evolving Fast Via AI Sophisticated bots...
Source: securityboulevard.com - Author: DataDome 2023 in Review As we know all too well at DataDome,...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Michael Vizard The OpenPubkey project this week shared a mechanism for remotely...
Source: securityboulevard.com - Author: Michael Thelander Of all the SaaS tools used by federal IT teams,...
Source: securityboulevard.com - Author: Francis Guibernau On January 16, 2024, the Federal Bureau of Investigation (FBI)...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Sindhu Reddy Kalathur Gopal, Diksha Shukla, James David Wheelock,...
Source: securityboulevard.com - Author: Adam King Penetration testing has become a cornerstone of robust cybersecurity strategy....
Source: securityboulevard.com - Author: Matthew Rosenquist Cybersecurity risks increase every year and bludgeon victims who fail...
The Benefits of Using DCIM Software for Data Center Cable Management – Source: securityboulevard.com
Source: securityboulevard.com - Author: Rajan Sodhi In the ever-evolving landscape of information technology, the management of...
Source: securityboulevard.com - Author: Maciej Mensfeld In my previous blog post, we saw how the growth...