Qualys Discovers Two Major Vulnerabilities – Techstrong TV Bharat Jogi, Director of Security and Threat Research...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Importance of being agile & the necessary ingredients Fraud represents an asymmetric challenge. A fast reaction...
What is mobile security? The use of smartphones has surged, but the users’ knowledge regarding the...
Automatic Restoration of Corrupted UPX-packed Samples In this blog, we share a tool (available on Git...
Pondurance Innovations and Integrations for Cloud Security Cloud computing has created the biggest tectonic shift in...
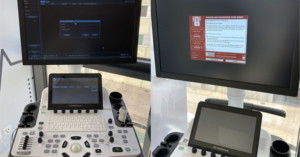
Educational institutions and students on hacker’s radar Over the last two months, hackers have stepped up...
Consistent Authentication and Device Posture policies for SaaS The adoption of SaaS (Software as a Service)...
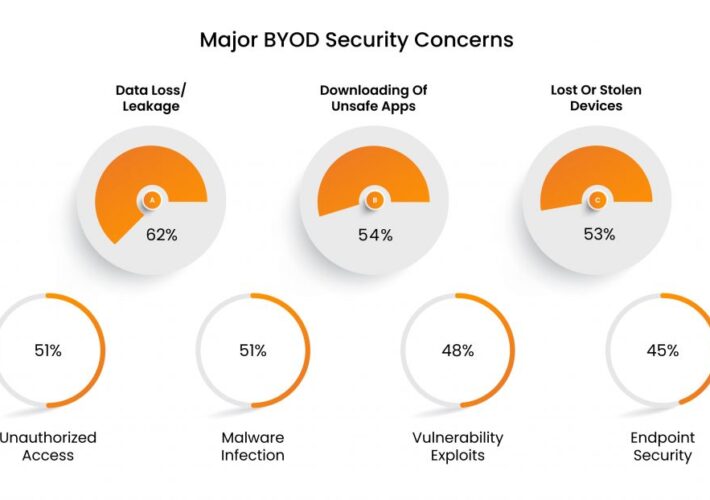
The Emergence Of BYOD: Are Personal Devices Acceptable? To bring or not to ‘bring your own...
Forrester: CISO Budgets Not Immune to Cuts With looming pullbacks in enterprise technology budgets—including, potentially, security...
Why It’s Important to Take Notice of AWS IAM Roles Anywhere IAM Roles Anywhere may be...
Confessions of a Network Engineer – Remote Access VPNs In 2001, I joined a global retailer...
Janet Jackson Can Crash Laptops, Credential Phishing Attacks Skyrocket, A Phone Carrier That Doesn’t Track You...
Extra, Extra, VERT Reads All About It: Cybersecurity News for the Week of August 22, 2022...
Your DevOps Process Needs to Integrate API Security If your organization relies on the cloud, you...
OpenText/Micro Focus Deal Signals New Phase of Consolidation After 30 years in and around the security...
LastPass Admits Hackers Stole Source Code, Proprietary Tech Info The last thing any company that makes...
BSidesTLV 2022 – Rani Hod’s ‘How Not To Encrypt Your Files’ Our thanks to BSidesTLV for...
Exposing a Compilation of Known Ransomware Group’s Dark Web Onion Web Sites – An OSINT Analysis...
Will Voluntary CISA Cyber Goals Be Enough to Protect Critical Infrastructure? The Cybersecurity and Infrastructure Security...
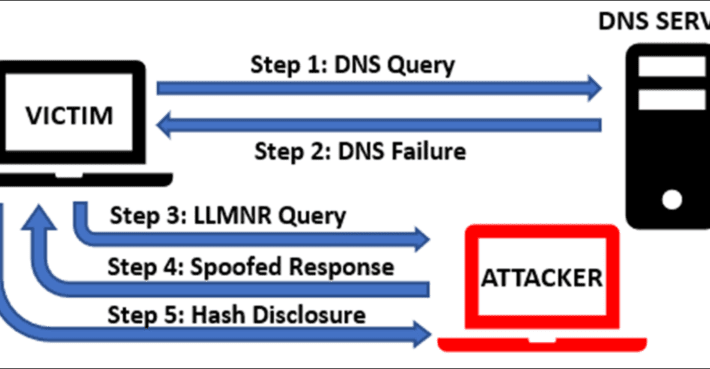
How to Prevent High Risk Authentication Coercion Vulnerabilities Most of us already know the basic principle...
BSidesTLV 2022 – Philip Tsukerman’s And Amir Kutcher’s ‘Unmasked! – Fighting Stealthy Execution Methods Using Process...
Key Points from the IBM Cost of a Data Breach Report 2022 The volume and impact...
Apple flaws put company networks at risk Last week, Apple found two zero-day vulnerabilities in both...
This Week in Malware – 450 Packages and a Phishing Campaign Against PyPI Maintainers This week...
XKCD ‘Tetherball Configurations’ via the comic artistry and dry wit of Randall Munroe, resident at XKCD!...
When to Use Penetration Testing Software, Services, or Both The post When to Use Penetration Testing...
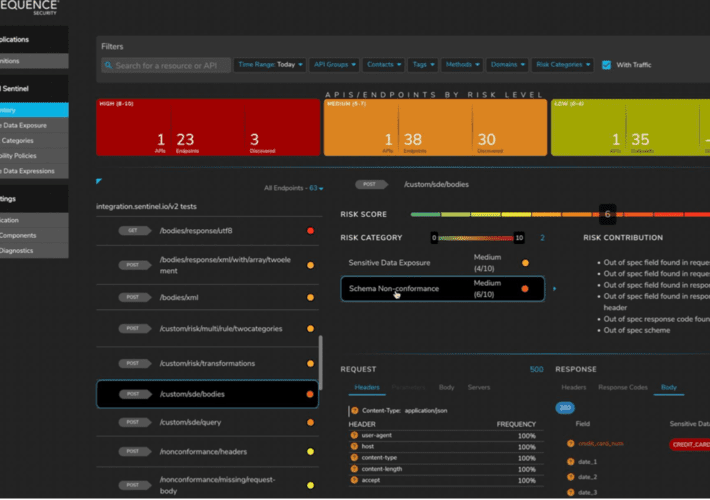
Unified API Protection for Telcos and Mobile Carriers – Time to Value Largest Mobile Carrier Identified...
BSidesTLV 2022 – Shira Stepansky’s ‘Diamond Model Analysis Of Whatsapp Security Breach’ Our thanks to BSidesTLV...
IAM budget in a recession How to make the most out of your 2023 IAM budget...
LastPass Breach Raises Disclosure Transparency Concerns In the graphic novel “The Watchman” by Alan Moore and...