Source: securityboulevard.com - Author: Jeffrey Burt The accelerating innovation of generative AI will increase the risks...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Avast Blog In the dynamic landscape of online scams, our Avast team...
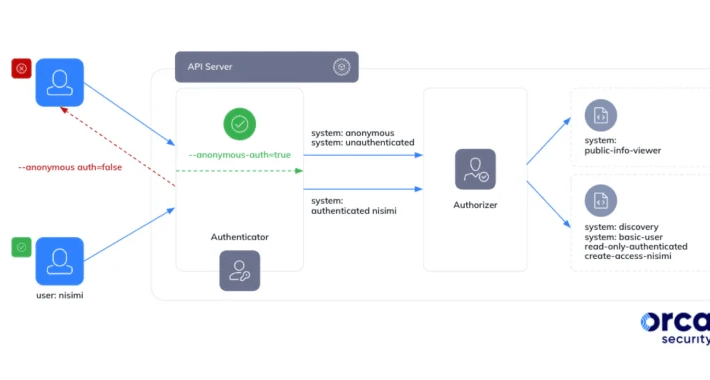
Source: securityboulevard.com - Author: Ben Hirschberg If you’re using GKE (Google Kubernetes Engine), you should be...
Source: securityboulevard.com - Author: Jeffrey Burt The growing number and sophistication of cyberattacks and the financial...
Source: securityboulevard.com - Author: ltabo Meet the Ona: Radu Boian ltabo Thu, 01/25/2024 – 15:01 Hi,...
Source: securityboulevard.com - Author: Steve Winterfeld In the ever-evolving landscape of cybersecurity, securing your company’s operations...
Source: securityboulevard.com - Author: Michal Oglodeck Mark McNasby, CEO and co-founder of Ivy.ai, co-authored this article.Artificial...
Source: securityboulevard.com - Author: Michael Vizard Protect AI today launched a Guardian gateway that enables organizations...
Source: securityboulevard.com - Author: Jeffrey Burt The personal information of more than 340,000 customers of popular...
Source: securityboulevard.com - Author: Axio In last week’s SEC Solution Launch Webinar, Axio CEO Scott Kannry...
Source: securityboulevard.com - Author: Corey Sinclair On 22 January, Fortra issued an advisory stating that versions...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Greg Bulmash We've talked about how Continuous Integration and Continuous Delivery (CI/CD)...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Richi Jennings Researchers discover unsecured database of stolen personal information.And you thought last...
Source: securityboulevard.com - Author: Jonas Bülow Knudsen ADCS Attack Paths in BloodHound — Part 1 Since Will Schroeder and...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
CVE-2024-0204: Fortra GoAnywhere MFT Authentication Bypass Deep-Dive – Source: securityboulevard.com
Source: securityboulevard.com - Author: Zach Hanley On January 22, 2024 Fortra posted a security advisory for...
Source: securityboulevard.com - Author: Steve Prentice What does a suburban roofing company have in common with...
Source: securityboulevard.com - Author: Team Nuspire The Federal Bureau of Investigation (FBI) and the Cybersecurity and...
Source: securityboulevard.com - Author: Aaron Costello, Principal SaaS Security Engineer @ AppOmni One of the security...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Maximizing Security in K-12 IT: Best Practices for Safeguarding Data – Source: securityboulevard.com
Source: securityboulevard.com - Author: Kevin Smith The prevalence of malicious cyber activity is increasing globally, and...
Source: securityboulevard.com - Author: bacohido Washington D.C. Jan. 22, 2024 – Today, the National Cybersecurity Alliance (NCA), announced...
Source: securityboulevard.com - Author: Jeffrey Burt The bad actor who hacked into the X account of...
Source: securityboulevard.com - Author: Horizon3.ai How a Prevailing Transportation Company Modernized Security with NodeZero Cyber protection...
Source: securityboulevard.com - Author: Dana Epp If there is anything we can learn from the latest...
Source: securityboulevard.com - Author: Shelley Leveson, Director of Content Marketing, HYPR One of the biggest security...
Source: securityboulevard.com - Author: bacohido New York, NY, Jan. 22, 2024 —Memcyco Inc, the real-time digital...
Source: securityboulevard.com - Author: Marc Handelman Identity & Access Network Security Security Bloggers Network Home » Cybersecurity »...