Source: securityboulevard.com - Author: Nitzan Gursky From the crudest low-effort phishing attempts to the most sophisticated...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: cyberwire Toronto, Canada, January 29th, 2024, Cyberwire In an era where online...
Source: securityboulevard.com - Author: Michael Vizard A report published by Datadog suggests that cybercriminal activity aimed...
Source: securityboulevard.com - Author: Bruce Morton Looking Back at 2023 2023 was a year of change...
Source: securityboulevard.com - Author: Naveen Sunkavally Last Wednesday, on January 24, 2024, the Jenkins team issued...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author In the ever-evolving world of...
Source: securityboulevard.com - Author: Cameron Delfin In today’s digital age, organizations face the constant threat of...
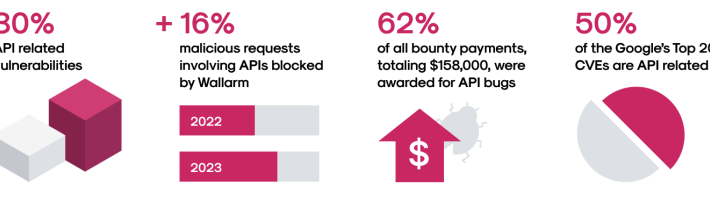
Source: securityboulevard.com - Author: girishwallarm The Wallarm Security Research team is pleased to share the latest...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity Every January, NASCIO and PTI release their forecasts for...
Source: securityboulevard.com - Author: Esther Han As technology continues to evolve at an unprecedented pace, the...
Source: securityboulevard.com - Author: Leigh Dow Safeguarding our online accounts has never been more crucial. One...
Source: securityboulevard.com - Author: Joseph Beeton, Senior Application Security Researcher, Contrast Security Security Bloggers Network Home...
Source: securityboulevard.com - Author: Riddika Grover The rise in cyber attacks has become a major worry....
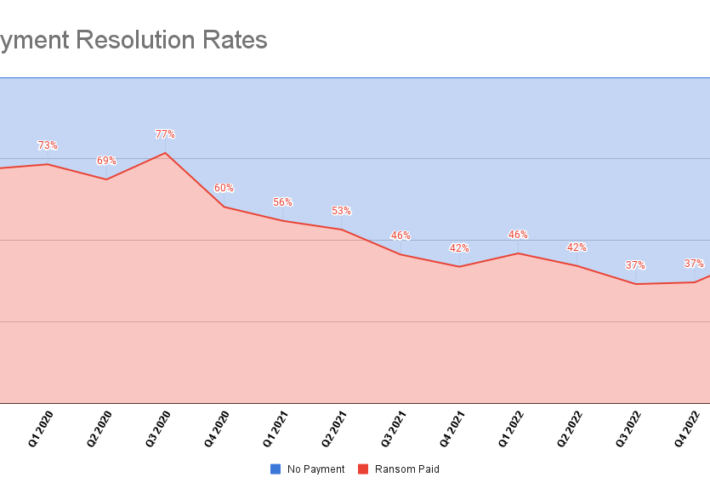
Source: securityboulevard.com - Author: Bill Siegel Table of Contents Ransomware Bans Payment Rates Types of Ransomware...
Source: securityboulevard.com - Author: Pondurance Every month, the Pondurance team hosts a webinar to keep clients...
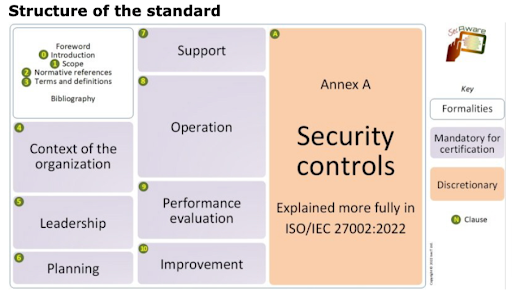
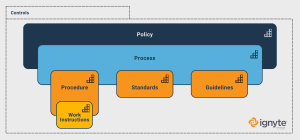
Source: securityboulevard.com - Author: Max Aulakh Cybersecurity is a vast and complex field, and it’s made...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
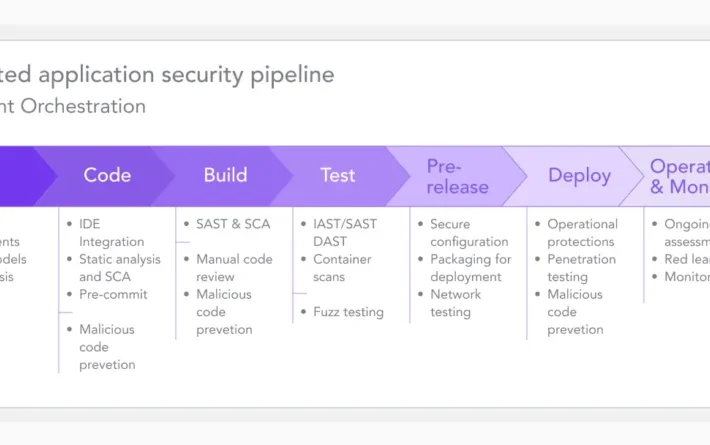
Source: securityboulevard.com - Author: Aaron Linskens In recent years, DevSecOps swiftly emerged as a crucial new...
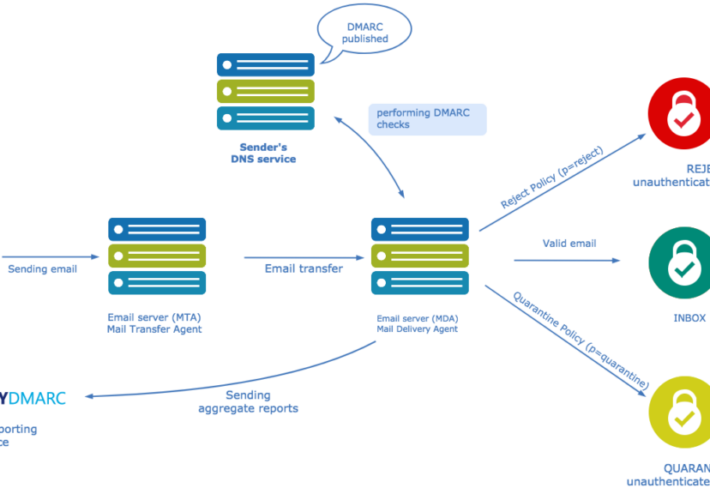
Source: securityboulevard.com - Author: Ani Avetisyan With the rising volume of fraudulent emails and AI-enhanced phishing...
Source: securityboulevard.com - Author: Marc Handelman Hot Topics Cybersecurity Standards vs Procedures vs Controls vs Policies...
Source: securityboulevard.com - Author: Scott Wright The way AI stores data is a huge concern. As...
Source: securityboulevard.com - Author: Marc Handelman Hot Topics Cybersecurity Standards vs Procedures vs Controls vs Policies...
Source: securityboulevard.com - Author: Jeffrey Burt Check Point researchers last year saw a 587% increase between...
Source: securityboulevard.com - Author: Michael Callahan January is often a time for reflection, and setting goals...
Source: securityboulevard.com - Author: Ijlal Loutfi Researchers have been working on solutions for runtime security for...
Source: securityboulevard.com - Author: Julie Peterson CI/CD Pipeline Security Given the demand for rapid innovation and...
Source: securityboulevard.com - Author: Marc Handelman Thursday, January 25, 2024 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Richi Jennings Patternz and Nuviad enable potentially hostile governments to track individuals...