Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
FTC accuses payments firm of knowingly assisting tech support scammers
Multinational payment processing firm Nexway has been rapped across the knuckles by the US authorities, who claim that the firm knowingly processed fraudulent credit card payments...
Take a tour of the Edgescan Cybersecurity Platform
Graham Cluley Security News is sponsored this week by the folks at Edgescan. Thanks to the great team there for their support! Edgescan simplifies Vulnerability Management...
Infoblox Uncovers DNS Malware Toolkit & Urges Companies to Block Malicious Domains
SANTA CLARA, Calif., April 20, 2023 /PRNewswire/ — Infoblox Inc. the company that delivers a simplified, cloud- enabled networking and security platform for improved performance and protection, today published...
Bitsight Expands into Integrated Cyber-Risk Management
BOSTON – April 20, 2023 – Bitsight, a leader in managing and monitoring cyber risk, today unveiled its expansion into a broader category of integrated cyber risk...
‘GhostToken’ Opens Google Accounts to Permanent Infection
A security vulnerability in Google’s Cloud Platform (GCP) could have allowed cyberattackers to hide an unremovable, malicious application inside a victim’s Google account, dooming the account...
Red Canary Announces Readiness
DENVER, April 20, 2023 /PRNewswire/ — Red Canary, a leader in managed detection and response, launched Red Canary Readiness, a new portfolio of offerings that gives teams a...
3CX Supply Chain Attack Tied to Financial Trading App Breach
Turns out 3CX was not the original target in a recent supply chain compromise affecting customers of the video conferencing software maker: The attack came via...
Major US CFPB Data Breach Caused by Employee
The Consumer Financial Protection Bureau (CFPB), an agency of the US government that protects consumers in the financial sector, announced that an employee committed a major...
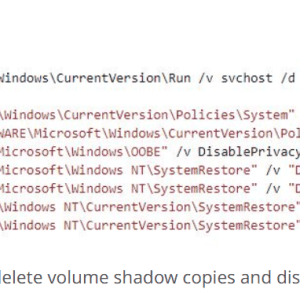
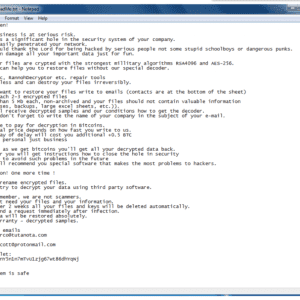
Trigona Ransomware Trolling for ‘Poorly Managed’ MS-SQL Servers
The Trigona ransomware threat actors are waging a campaign against Microsoft SQL database servers because many of them have external connections and weak passwords, leaving them open...
Expert Insight: Dangers of Using Large Language Models Before They Are Baked
The Berryville Institute of Machine Learning (BIML) recently attended Calypso AI’s Accelerate AI 2023 conference in Washington, DC. The meeting included practitioners from both government and...
Twitter’s 2FA Policy Is a Call for Passkey Disruption
Twitter recently disabled SMS-based two-factor authentication (2FA) except for Twitter Blue subscribers. While the intended results may be cost-savings and boosting the number of subscribers, the...
‘AuKill’ Malware Hunts & Kills EDR Processes
The “AuKill” cybercrime tool has emerged, which threat actors are using to disable endpoint detection and response (EDR) defenses used by enterprises before deploying ransomware. It makes use of...
North Korean Hacker Suspected in 3CX Software Supply Chain Attack
The 3CX Desktop App software has been reportedly compromised via a prior software supply chain breach, with a North Korean actor suspected to be responsible. According...
Daggerfly APT Targets African Telecoms Firm With New MgBot Malware
The APT group known as Daggerfly (as well as Evasive Panda and Bronze Highland) has been observed targeting a telecommunications organization in Africa with new plugins...
ChatGPT-Related Malicious URLs on the Rise
The number of newly registered and squatting domains related to ChatGPT grew by 910% monthly between November 2022 and early April 2023. The findings, shared by...
#CYBERUK23: UK Strengthens Cybersecurity Audits for Government Agencies
The UK Government has officially launched GovAssure, a new regime of independent audits of government agencies’ cyber resilience, the Chancellor of the Duchy of Lancaster Oliver...
The EU’s Cyber Solidarity Act: Security Operations Centers to the rescue! – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Márk Szabó. The legislation aims to bolster the Union’s cyber-resilience and enhance its capabilities to prepare for, detect and respond to incidents...
PC running slow? 10 ways you can speed it up – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: André Lameiras. Before you rush to buy new hardware, try these simple tricks to get your machine up to speed again –...
Experts disclosed two critical flaws in Alibaba cloud database services – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Researchers disclosed two critical flaws in Alibaba Cloud’s ApsaraDB RDS for PostgreSQL and AnalyticDB for PostgreSQL. Researchers from cloud security...
Google TAG warns of Russia-linked APT groups targeting Ukraine – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. The researchers from Google TAG are warning of Russia-linked threat actors targeting Ukraine with phishing campaigns. Russia-linked threat actors launched...
Trigona Ransomware targets Microsoft SQL servers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Threat actors are hacking poorly secured and Interned-exposed Microsoft SQL servers to deploy the Trigona ransomware. Threat actors are hacking...
Russian national sentenced to time served for committing money laundering for the Ryuk ransomware operation – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Russian national Denis Mihaqlovic Dubnikov has been sentenced to time served for committing money laundering for the Ryuk ransomware operation. Russian...
Google fixed the second actively exploited Chrome zero-day of 2023 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Google rolled out emergency security patches to address another actively exploited high-severity zero-day flaw in the Chrome browser. Google rolled...
Why BISOs should oversee policy & report to CROs
By Edwin Doyle, Global Cyber Security Strategist. Cyber security policy is a comprehensive framework consisting of guidelines, protocols, principles and regulations that aim to safeguard an...
Climate change, cyber security and saving the planet
EXECUTIVE SUMMARY: Although the topics of climate change and cyber security seem worlds apart, the reality is that they’re deeply interconnected. The intersection of the two...
RSAC Fireside Chat: How timely intel from the cyber underground improves counter measures
Good intelligence in any theater of war is invaluable. Timely, accurate intel is the basis of a robust defense and can inform potent counterattacks. Related: Ukraine...
What to know: New AI rules in the U.S.
EXECUTIVE SUMMARY: As the fastest-growing consumer application in history, with more than 100 million monthly active users, ChatGPT has gained the attention of lawmakers and policy...
New Zero-Click Exploits Against iOS
HomeBlog New Zero-Click Exploits Against iOS CitizenLab has identified three zero-click exploits against iOS 15 and 16. These were used by NSO Group’s Pegasus spyware in...
RSAC Fireside Chat: StackHawk helps move the application security needle to ‘shift everywhere’
By Byron V. Acohido Embedding security into the highly dynamic way new software gets created and put into service — on the fly, by leveraging ephemeral...