Source: www.bleepingcomputer.com – Author: Bill Toulas An international law enforcement operation codenamed ‘SpecTor’ has arrested 288 dark web vendors and customers worldwide, with police seizing €50.8...
How To Secure Web Applications Against AI-assisted Cyber Attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sponsored by Outpost24 Artificial intelligence (AI) has brought forth a new era of innovation, with its transformative impact being felt across various...
Going into the Darknet: How Cynet Lighthouse Services Keep Cybersecurity Teams One Step Ahead of Hackers – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By monitoring the darknet, as well as underground forums, Cynet is able to identify and prepare for the latest cybersecurity...
Security Tool Integration Isn’t Enough Anymore – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Manoj Arora, Founder & CEO, Difenda Organizations today are overwhelmed with options when it comes to security tools and...
Making a Business Case for Cyber Threat Intelligence: Unveiling the Value Realization Framework – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Kaustubh Medhe, Head of Research and Intelligence at Cyble Cybercriminal motivations rarely change over time. A typical cyberattack is...
Global Operation Takes Down Dark Web Drug Marketplace – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Law enforcement agencies around the world seized an online marketplace and arrested nearly 300 people allegedly involved in buying and...
IT Services Firm Bitmarck Takes Systems Offline Following Cyberattack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire German IT services provider Bitmarck on Monday announced that it has shut down customer and internal systems following a cyberattack....
T-Mobile Says Personal Information Stolen in New Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire US wireless carrier T-Mobile is informing some customers that their personal information was compromised in a recent data breach. After...
Critical Infrastructure Organizations Urged to Identify Risky Communications Equipment – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Cybersecurity and Infrastructure Security Agency (CISA) on Monday issued an alert to urge critical infrastructure organizations to scope...
iPhone Users Report Problems Installing Apple’s First Rapid Security Response Update – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Apple has released its first Rapid Security Response update, but many iPhone users have complained that they are having problems...
Cybersecurity M&A Roundup: 38 Deals Announced in April 2023 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Thirty-eight cybersecurity-related merger and acquisition (M&A) deals were announced in March 2023. An analysis conducted by SecurityWeek shows that more...
CISA Warns of Attacks Exploiting Oracle WebLogic Vulnerability Patched in January – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Cybersecurity and Infrastructure Security Agency (CISA) has added three vulnerabilities to its known exploited vulnerabilities catalog, including an...
Exploitation of 5-Year-Old TBK DVR Vulnerability Spikes – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Fortinet warns of a massive spike in exploitation attempts targeting a five-year-old authentication bypass vulnerability in TBK DVR devices. A...
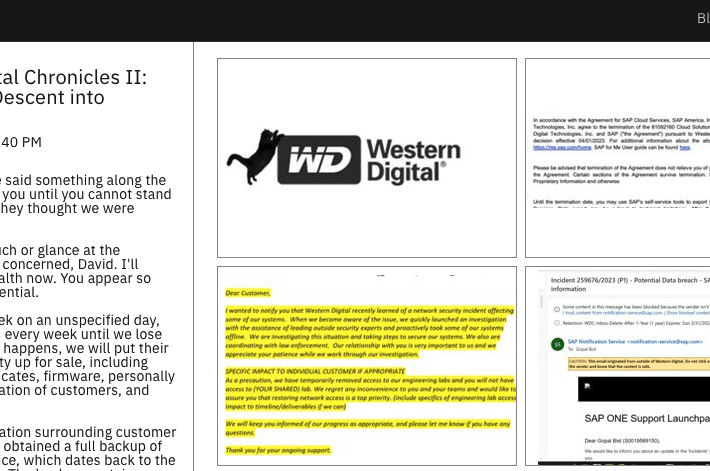
Leaked Files Show Extent of Ransomware Group’s Access to Western Digital Systems – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A ransomware group has leaked files showing the extent of their access to Western Digital systems and it appears that...
Medusa ransomware gang leaks students’ psychological reports and abuse allegations – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Students and teachers at the Minneapolis Public School (MPS) District, which suffered a huge ransomware attack at the end of...
20 Hottest Cybersecurity Products At RSAC 2023 – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Security News Kyle Alspach April 25, 2023, 11:57 AM EDT At RSA Conference 2023 this week, vendors are showcasing new products...
RSAC 2023 Day 1: Fighting Bad AI with Good AI Future of Cybersecurity – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Just a moment… Enable JavaScript and cookies to continue Original Post URL: https://www.proofpoint.com/us/newsroom/news/rsac-2023-day-1-fighting-bad-ai-good-ai-future-cybersecurity Category & Tags: – Views: 1
Promising Jobs at the U.S. Postal Service, ‘US Job Services’ Leaks Customer Data – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs A sprawling online company based in Georgia that has made tens of millions of dollars purporting to sell access to jobs...
The future is now! Mind-bending highlights from RSA 2023 – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: At this year’s RSA Conference, we witnessed some of the brightest minds in cyber security gathered to discuss the...
Microsoft’s next-level nomenclature, naming hacking groups – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Last week, Microsoft’s cyber security division announced that it is changing its taxonomy for naming hacking groups. Previously, Microsoft...
GUEST ESSAY: Making the case for leveraging automation to eradicate cybersecurity burnout – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Zac Amos The rising complexity and prevalence of cybersecurity threats are making experts anxious. Related: Training employees to mitigate phishing...
USENIX Enigma 2023 – Fabrício Ceschin – ‘Spotting The Differences: Quirks Of Machine Learning (In) Security’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Boost Efficiency: Integrate Hyperview Asset Discovery with ServiceNow CMDB – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rajan Sodhi Managing IT assets is a crucial part of any organization’s digital strategy, and effectively tracking, monitoring and organizing these assets...
Modern Device Trust for Today’s Advanced Threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ashur Kanoon Device trust has come a long way, and is evolving even faster, stimulated by integrations and vendors that are developing...
Code42 Incydr + Splunk Integration: Streamline Your Insider Risk Management Program and Automate Response Controls – Source: securityboulevard.com
Source: securityboulevard.com – Author: Brittney Belt According to Code42’s 2023 Data Exposure Report, having the right technology in place and having technology that can provide the...
Randall Munroe’s XKCD ‘Tapetum Lucidum’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Threats, Vulnerabilities, and Risks – Source: securityboulevard.com
Source: securityboulevard.com – Author: SencodeTeam As a business owner or employee in the UK, it’s important to have a comprehensive understanding of the cyber threats, vulnerabilities,...
Delivering Generative AI to Cybersecurity for Over 3 Years – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Shea “Don’t call it a comeback. I’ve been here for years!” – LL Cool J Said best by LL Cool J,...
GUEST ESSAY: Making the case for leveraging automation to eradicate cybersecurity burnout – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Zac Amos The rising complexity and prevalence of cybersecurity threats are making experts anxious. It pressures working analysts to perform...
API Security for Financial Services – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tony Bailey When it comes to the global financial services industry which includes banks, credit unions, exchange houses, finance companies, payment card...