Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Toyota has disclosed that for more than 10 years, a misconfigured cloud bucket left more 2.15 million...
Microsoft Follina Bug Is Back in Meme-Themed Cyberattacks Against Travel Orgs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A threat actor is exploiting last year’s Follina (RCE) remote code execution vulnerability to deploy the...
Microsoft Advisories Are Getting Worse – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jacob Baines, Lead Vulnerability Researcher, VulnCheck As the 20th anniversary of Patch Tuesday approaches later this year, many are reflecting on the...
TSA Official: Feds Improved Cybersecurity Response Post-Colonial Pipeline – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading In the wake of the ransomware attack on the Colonial Pipeline, the US Transportation Security Agency...
New RA Group ransomware gang is the latest group using leaked Babuk source code – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A previously unknown ransomware group known as RA Group is targeting companies in U.S. and South Korea with leaked Babuk...
Introducing the DRM-Report Q1 2023: Unveiling the Current State of Ransomware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini DRM Dashboard Ransomware Monitor released the first quarterly report for the year 2023 about the activities of ransomware groups globally....
Former Ubiquiti employee gets 6 years in jail for stealing confidential data and extorting company – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A former Ubiquiti employee has been sentenced to six years in jail for the theft of confidential data and extorting company for...
Former ByteDance executive alleges TikTok of wrongful conduct – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A former ByteDance executive revealed that the China government has access to TikTok data, including data stored in the United....
Brightly Software Notifying 3 Million SchoolDude Users of Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Brightly Software last week started informing roughly three million individuals that their personal information might have been compromised in a...
Discord Informs Users of Data Breach Involving Customer Support Provider – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire VoIP and instant messaging social platform Discord is notifying users that some of their information was compromised in a cybersecurity...
WordPress Field Builder Plugin Vulnerability Exploited in Attacks Two Days After Patch – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Threat actors were seen adopting public proof-of-concept (PoC) exploit code targeting a cross-site scripting (XSS) vulnerability in the Advanced Custom...
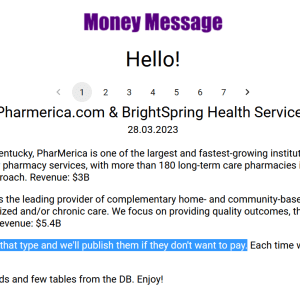
PharMerica Discloses Data Breach Impacting 5.8 Million Individuals – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire National pharmacy network PharMerica last week started sending out notification letters to more than 5.8 million individuals to disclose a...
Capita Cyberattack Hits UK Pension Funds – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The recent hacker attack aimed at UK-based business process outsourcing and professional services company Capita could impact hundreds of pension...
Philadelphia Inquirer Hit by Cyberattack Causing Newspaper’s Largest Disruption in Decades – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press The Philadelphia Inquirer experienced the most significant disruption to its operations in 27 years due to what the newspaper calls...
CISA: Several Old Linux Vulnerabilities Exploited in Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Cybersecurity and Infrastructure Security Agency (CISA) has added several Linux and Linux-related flaws to its known exploited vulnerabilities...
ReversingLabs File Enrichment API for Microsoft Sentinel – Source: securityboulevard.com
Source: securityboulevard.com – Author: ReversingLabs The modern security operations center (SOC) team requires high levels of agility and accuracy to detect and respond to the latest...
Rail Security: “Unsafe at Any Speed” – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kevin Kumpf A version of this article was originally published on IndustrialCyber.co. What entices me to sit down and write a blog?...
How to Know if You’ve Been Infected by Ransomware – Source: securityboulevard.com
Source: securityboulevard.com – Author: Stu Sjouwerman Detecting ransomware activity has become increasingly difficult because adversaries are constantly evolving their tools, tactics and techniques. For example, threat...
The Importance of Understanding the Unique Challenges of IT & OT Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sagi Kovaliov Cybersecurity threats have been increasing at an alarming rate, and organizations must continuously adapt to address these threats. The convergence...
War, Hunh. Yeah. What is it Good For? Reducing Insurer Liability for Cyberattacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mark Rasch A New Jersey court recently ruled that an insurer was not relieved from its obligation to pay for Merck’s losses...
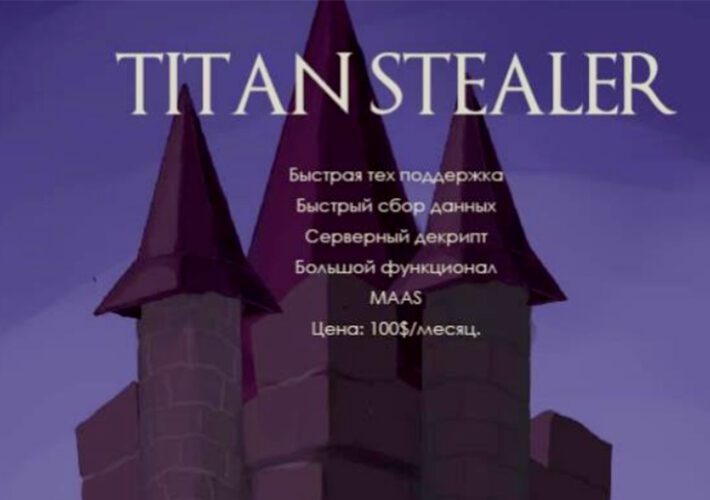
Info-Stealing Malware Populates ‘Cloud of Logs’ Offerings – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Private Subscription Services Emerge, Together With Fresh Strains of Info Stealers Mathew J. Schwartz (euroinfosec)...
The Battle Against IoT Cyber Threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dariel Marlow The rapid increase of the Internet of Things (IoT) technology has transformed the world in many ways. From home automation...
What Happens When an AI Company Falls Victim to a Software Supply Chain Vulnerability – Source: securityboulevard.com
Source: securityboulevard.com – Author: Barak Brudo An image illustrating AI goes wrong On March 20th OpenAI took down the popular generative AI tool ChatGPT for a few...
Setting up an OT-ICS Incident Response Plan – Source: securityboulevard.com
Source: securityboulevard.com – Author: Prayukth K V Operational Technology (OT) and Industrial Control System (ICS) are the backbones of critical infrastructure that controls and monitor physical...
SHARED INTEL: From airbags to malware: vehicle cyber safety arises in the age of connected cars – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Kolawole Samuel Adebayo In an increasingly interconnected world, the evolution of the automotive industry presents an exciting yet daunting prospect....
Private Tweets Exposed, Unauthorized Tracking Collaboration, AI Risks and Regulation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Eston In this episode we discuss a recent Twitter security incident that caused private tweets sent to Twitter Circles to become...
Live Webinar Tomorrow | Using Machine Learning and Hyperscaled Cloud to Deliver Zero Trust – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Jason Georgi Global Field CTO, Prisma SASE, Palo Alto Networks Jason is the Global Field Chief Technology Officer for Prisma SASE...
Airline exposes passenger info to others due to a ‘technical error’ – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma airBaltic, Latvia’s flag carrier has acknowledged that a ‘technical error’ exposed reservation details of some of its passengers to other airBaltic...
New RA Group ransomware targets U.S. orgs in double-extortion attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new ransomware group named ‘RA Group’ is targeting pharmaceutical, insurance, wealth management, and manufacturing firms in the United States...