Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Threat actors are targeting corporate users who are interested in downloading Webex — by buying ad space...
Cuba Ransomware Gang Continues to Evolve With Dangerous Backdoor – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Researchers have uncovered fresh malware samples attributed to ransomware group Cuba, representing new versions of BurntCigar...
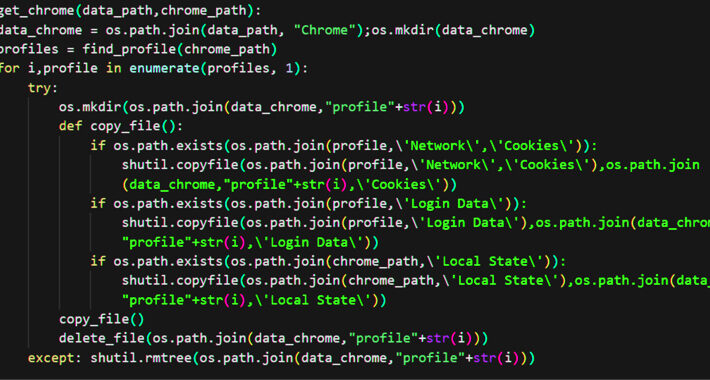
NodeStealer Malware Now Targets Facebook Business Accounts on Multiple Browsers – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 15, 2023THNOnline Security / Malware An ongoing campaign is targeting Facebook Business accounts with bogus messages to harvest victims’ credentials...
DDoS 2.0: IoT Sparks New DDoS Alert – Source:thehackernews.com
Source: thehackernews.com – Author: . The Internet of Things (IoT) is transforming efficiency in various sectors like healthcare and logistics but has also introduced new security...
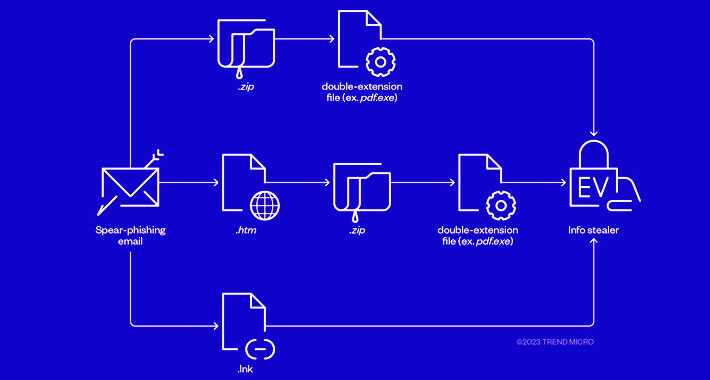
Cybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 15, 2023THNRansomware / Cyber Threat The threat actors behind RedLine and Vidar information stealers have been observed pivoting to ransomware...
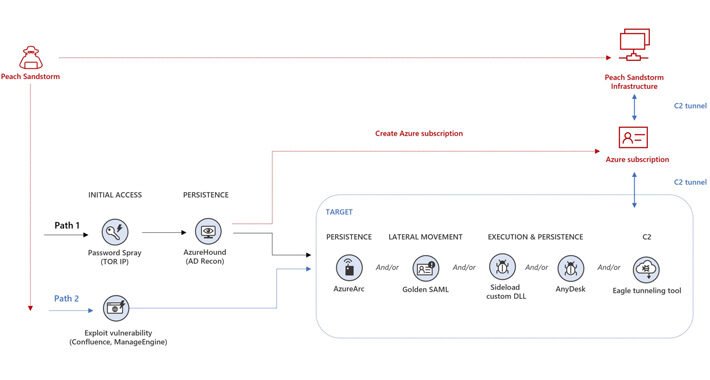
Iranian Nation-State Actors Employ Password Spray Attacks Targeting Multiple Sectors – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 15, 2023THNCyber Attack / Password Security Iranian nation-state actors have been conducting password spray attacks against thousands of organizations globally...
Battling DDoS attacks in the cloud – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Grant Asplund is a proven multi-channel senior sales and marketing executive with history of exemplary achievement introducing/launching new products and establishing...
MGM Resorts had $339M compromised in 10 minutes or less – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Hackers launched an attack that hit MGM Resorts on Sunday morning, rendering doors to buildings unusable, and ATM machines...
GUEST ESSAY: The timing is ripe to instill trust in the open Internet — and why this must get done – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Hannah Aubry In today’s digital age, trust has become a cornerstone of building a better Internet. Preserving privacy for a...
BLASTPASS: Government agencies told to secure iPhones against spyware attacks – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley What’s happened? CISA, the United States’s Cybersecurity and Infrastructure Security Agency, has ordered federal agencies to patch their iPhones against...
Greater Manchester Police latest force to suffer serious data breach – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Uh-oh, yet another UK police force has suffered a serious data breach. After the incidents involving Cumbria Police, Norfolk and...
Automation is key to effective and efficient pentest reporting – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Graham Cluley Security News is sponsored this week by the folks at PlexTrac. Thanks to the great team there for...
Car companies are collecting data on your sex life, and apparently you’re fine with that – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley It seems modern cars are gobbling up all kinds of data about their drivers including – astonishingly – details of...
Banking Cybersecurity: The Risks Faced by Financial Institutions – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac A data breach in the financial sector is one of the most impactful events in the cybersecurity landscape. That is...
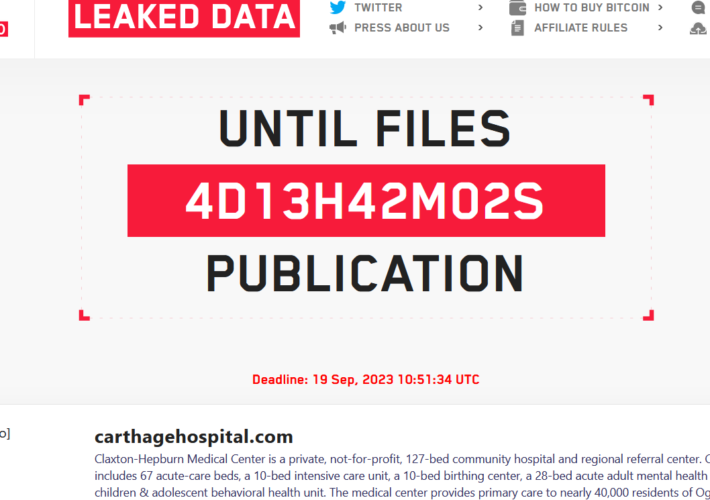
Lockbit ransomware gang hit the Carthage Area Hospital and the Clayton-Hepburn Medical Center in New York – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Lockbit ransomware gang hit the Carthage Area Hospital and the Clayton-Hepburn Medical Center in New York Pierluigi Paganini September 14,...
UK Greater Manchester Police disclosed a data breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini UK Greater Manchester Police disclosed a data breach Pierluigi Paganini September 14, 2023 UK Greater Manchester Police (GMP) disclosed a...
The iPhone of a Russian journalist was infected with the Pegasus spyware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The iPhone of a Russian journalist was infected with the Pegasus spyware Pierluigi Paganini September 14, 2023 The iPhone of...
Kubernetes flaws could lead to remote code execution on Windows endpoints – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Kubernetes flaws could lead to remote code execution on Windows endpoints Pierluigi Paganini September 14, 2023 Researchers discovered three security...
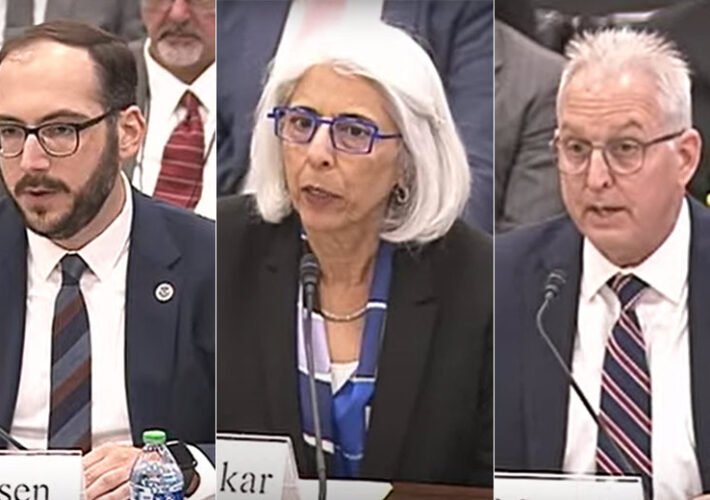
How the U.S. Government Views the Bright, Dark Sides of AI – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development White House, DOD, DHS Leaders Reveal How their Agencies Use...
Breach Roundup: Pegasus on Exiled Russian Journalist’s Phone – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Also: 9-Year Prison Sentence for Insider Trading Fueled by Password Theft Anviksha More (AnvikshaMore) • September 14, 2023 Image:...
Panel | Secrets on the Loose: How to Get the Most out of Your Secrets Management Program – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Robert Sawyer Sr. Director of Solutions Marketing, CyberArk Robert Sawyer is a software engineer turned marketing leader with over 20 years...
Live Fireside Chat | Getting Governance that Works – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
China Denies Banning Government Use of Apple iPhones – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Geo Focus: Asia , Geo-Specific , Government China Cites Apple Security Flaws in Warning to Foreign Mobile Device Manufacturers Jayant Chakravarti...
U.S. Senator Seeks Input on Ways to Protect Patient Privacy – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Healthcare , HIPAA/HITECH , Industry Specific Inquiry is Latest Move by a Lawmaker Hinting of New Data Protection Legislation Marianne Kolbasuk...
BSides Buffalo 2023 – Magno Logan – Hacking GitHub Actions – Abusing GitHub And Azure For Fun And Profit – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
Shifting Perspectives and Regulations Relating to Consent Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: ForgeRock Guest Contributor Businesses have a certain responsibility to disclose how consumer data is being used, and if they don’t, they face...
Patch Tuesday Update – September 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bill Niester Fall is here in much of America, and amidst the crunching of football pads and the smashing of apples for...
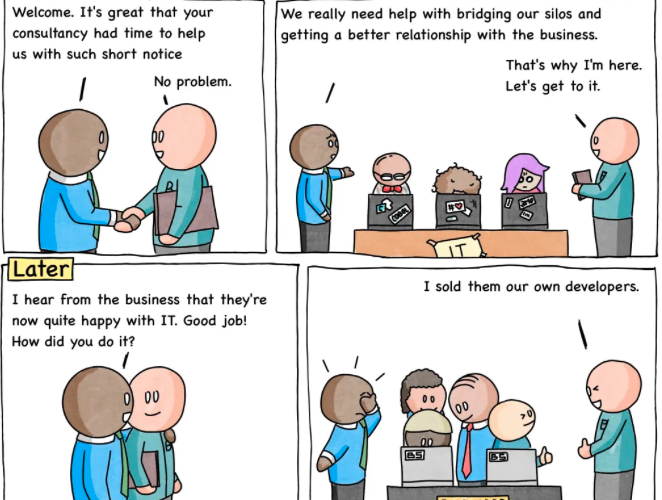
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnarav – #258 — The Business Are Happy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
Automating Kubernetes Cost Reductions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anthony Day Meet Rosie & Her Architecture Cloud costs are a common pain point. We hear about it all the time from...
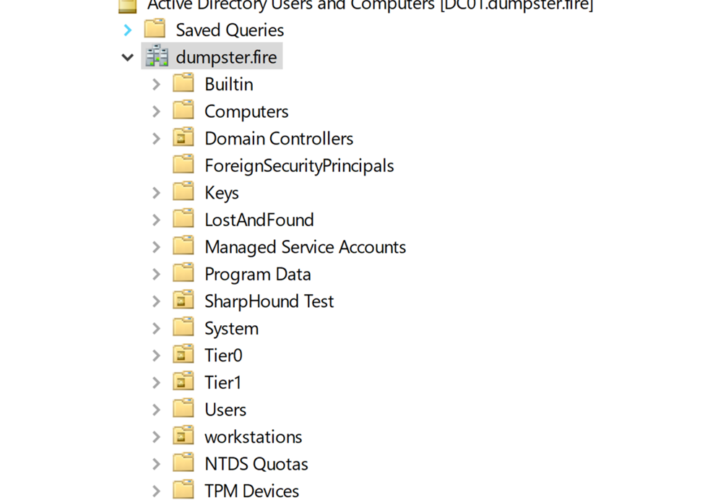
What is Tier Zero — Part 2 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jonas Bülow Knudsen What is Tier Zero — Part 2 Round 2! This is Part 2 of our webinar and blog post series Defining the...