Source: securityboulevard.com – Author: Jeffrey Burt The threat group that claims to have been involved in the high-profile attacks earlier this month on casino operators MGM...
Guide to IoT in 2023: What’s New and Why It Matters? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback The Dawn of IoT: A Revolution in the Digital World In today’s interconnected world, the Guide to IoT is more...
If the worst happens: How to prep your accounts so your loved one can get into them – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog It’s not fun to think about: But if you should unexpectedly die, could your spouse, partner, children or other loved...
Modernized Financial Cards for the Next Generation of Payments – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nak Koh Financial cards have been a cornerstone of our monetary transactions for decades, providing us with convenience and security. Yet as...
An Enterprise Action Plan For CDR – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team By David NeumanSenior Analyst, TAG Cyber [email protected] Introduction Information is the lifeblood of 21st-century businesses. They depend on the ability to...
Jobs That AI Can’t Replace: The Impact of Automation on Workforce – Source: securityboulevard.com
Source: securityboulevard.com – Author: ISHIR | Software Development India As the relentless march of automation reshapes industries, its profound influence on the workforce becomes increasingly evident....
Enhancing Cyberdefense for Your Business: Where to Begin – Source: securityboulevard.com
Source: securityboulevard.com – Author: Arani Adhikari In today’s digital landscape, cybersecurity incidents have become alarmingly common, affecting businesses of all sizes and industries. No longer limited...
ForgeRock Named Year’s Best Identity and Access Management Solution – Source: securityboulevard.com
Source: securityboulevard.com – Author: Fred Kost The ForgeRock Identity Platform has been awarded for excellence by three industry publications This has been a big year for...
APT36 state hackers infect Android devices using YouTube app clones – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The APT36 hacking group, aka ‘Transparent Tribe,’ has been observed using at least three Android apps that mimic YouTube to infect...
Windows Subsystem for Linux gets new ‘mirrored’ network mode – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has released Windows Subsystem for Linux (WSL) 2.0.0 with a set of new opt-in experimental features, including a new...
Thousands of Juniper devices vulnerable to unauthenticated RCE flaw – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas An estimated 12,000 Juniper SRX firewalls and EX switches are vulnerable to a fileless remote code execution flaw that attackers...
Microsoft Paint finally gets support for layers and transparency – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft is finally rolling out support for layers and image transparency to the Paint image editor application 38 years after...
Bumblebee malware returns in new attacks abusing WebDAV folders – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The malware loader ‘Bumblebee’ has broken its two-month vacation with a new campaign that employs new distribution techniques that abuse...
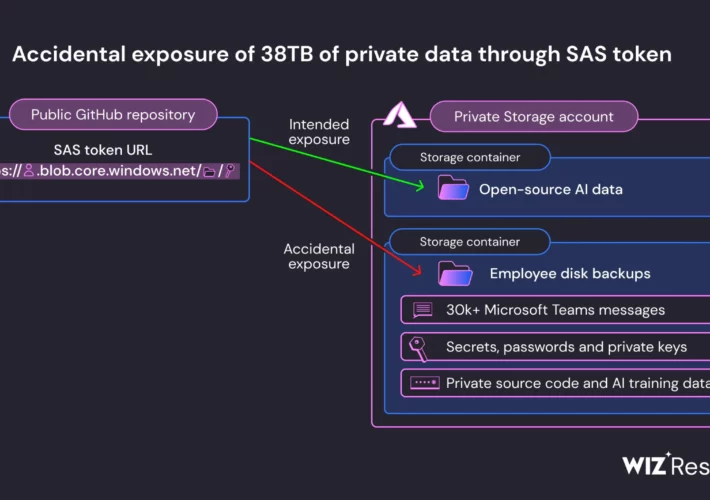
Microsoft leaks 38TB of private data via unsecured Azure storage – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The Microsoft AI research division accidentally leaked dozens of terabytes of sensitive data starting in July 2020 while contributing open-source...
New SprySOCKS Linux malware used in cyber espionage attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A Chinese espionage-focused hacker tracked as ‘Earth Lusca’ was observed targeting government agencies in multiple countries, using a new Linux...
Are your end-users’ passwords compromised? Here’s how to check. – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sponsored by Specops Software Passwords have long been used as the primary gatekeepers of digital security, yet they can also be a...
Australian Law Firm Hack Affected 65 Government Agencies – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Geo Focus: Australia , Geo-Specific Australian Federal Police, Department of Home Affairs Reportedly Among the Victims...
TransUnion Involved in Potential Hacking Incident – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Hacker ‘USDoD’ Claims Attack, Says He Has Data of More Than 50,000 Consumers Akshaya Asokan...
Live Webinar | Hacking Your Digital Identity: How Cybercriminals Can and Will Get Around Your Authentication Methods – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Anti-Phishing, DMARC , Biometrics , Business Email Compromise (BEC) Presented by KnowBe4 60 mins Inadequate authentication measures...
Nuance Notifying 14 NC Healthcare Clients of MOVEit Hacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , Incident & Breach Response , Industry Specific Entities Are Among Growing Tally of Health Sector Victims in Clop Mass...
Sift, LexisNexis Top Digital Fraud Management Forrester Wave – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Finance & Banking , Fraud Management & Cybercrime Newcomer, Established Vendor Lead Efforts to Stop...
Australian Law Firm Hack Affected 65 Government Agencies – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Geo-Specific , Ransomware Australian Federal Police, Department of Home Affairs Reportedly Among the Victims Mihir Bagwe...
TransUnion Involved in Potential Hacking Incident – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Hacker ‘USDoD’ Claims Attack, Says He Has Data of More Than 50,000 Consumers Akshaya Asokan...
Live Webinar | Hacking Your Digital Identity: How Cybercriminals Can and Will Get Around Your Authentication Methods – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Anti-Phishing, DMARC , Biometrics , Business Email Compromise (BEC) Presented by KnowBe4 60 mins Inadequate authentication measures...
Nuance Notifying 14 NC Healthcare Clients of MOVEit Hacks – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Healthcare , Incident & Breach Response , Industry Specific Entities Are Among Growing Tally of Health Sector Victims in Clop Mass...
Sift, LexisNexis Top Digital Fraud Management Forrester Wave – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Finance & Banking , Fraud Management & Cybercrime Newcomer, Established Vendor Lead Efforts to Stop...
Microsoft AI Researchers Expose 38TB of Data, Including Keys, Passwords and Internal Messages – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Researchers at Wiz have flagged another major security misstep at Microsoft that caused the exposure of 38 terabytes of private...
Google Extends Chromebook Lifespan, Promises 10 Years of Automatic Updates – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Google has announced that it is committed to provide regular automatic updates, with security patches, for all recent Chromebook iterations...
OT/IoT and OpenTitan, an Open Source Silicon Root of Trust – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend OpenTitan is a project aimed at bringing the success of open source software to the silicon design space – specifically...
Canadian Government Targeted With DDoS Attacks by Pro-Russia Group – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The pro-Russian cybercrime group named NoName057(16) has been observed launching distributed denial-of-service (DDoS) attacks against Canadian organizations, a fresh government...