Source: securityboulevard.com – Author: Ken Palla Trust is the currency we trade for success in a digital economy. Building and maintaining digital trust isn’t just a...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – Securing the ICT Supply Chain from Cybersecurity Threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-securing-the-ict-supply-chain-from-cybersecurity-threats/ Category & Tags: CISO Suite,Governance, Risk &...
The ROI of Microsegmentation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nik Hewitt The ROI of microsegmentation is undeniable for optimal business security investment The complexity, frequency, and eventual costs of cybersecurity threats...
Deadglyph Backdoor Targeting Middle Eastern Government – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Backdoor Is Associated With Stealth Falcon APT Group Prajeet Nair (@prajeetspeaks) •...
Cloud Smart Roadshow San Diego: Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Cloud Data Security & Resilience , Next-Generation Technologies & Secure Development Presented by VMware ...
Cloud Smart Roadshow San Jose: Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Presented by VMware 300 Minutes Learn how to navigate the cloud landscape with VMware, your compass for...
Cloud Smart Roadshow Los Angeles: Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Cloud Security , Next-Generation Technologies & Secure Development Presented by VMware 300 Minutes...
Live Webinar – 5 Critical Stages in Deploying a Modern Security Tech Stack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
CommonSpirit Details Financial Fallout of $160M Cyberattack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyber Insurance , Fraud Management & Cybercrime , Governance & Risk Management No Word Yet on Hospital Chain’s Cyber Insurance Claim,...
Polish Privacy Regulator Probes OpenAI’s ChatGPT – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , General Data Protection Regulation (GDPR) , Next-Generation Technologies & Secure Development Agency Is the Latest...
When It Comes to Email Security, The Cloud You Pick Matters – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Businesses using Google Workspace are only half as likely to suffer a reportable cyberattack compared to...
Xenomorph Android Malware Targets Customers of 30 US Banks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading The cybercriminals behind a sophisticated Android banking Trojan called Xenomorph, who have been actively targeting users...
MOVEit Flaw Leads to 900 University Data Breaches – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading National Student Clearinghouse, a nonprofit that provides enrollment and other services for thousands of colleges and universities...
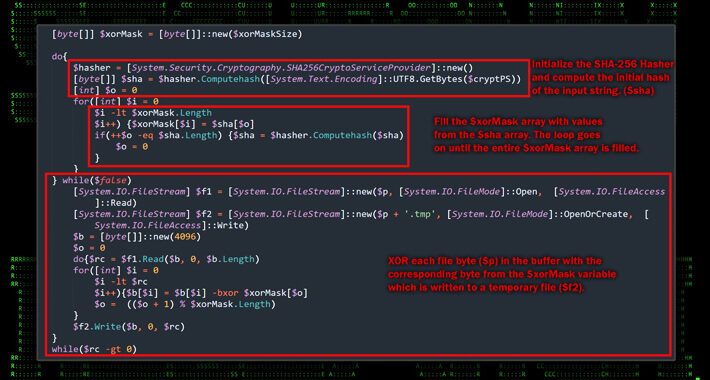
UAE-Linked ‘Stealth Falcon’ APT Mimics Microsoft in Homoglyph Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Researchers have recently discovered a sophisticated backdoor with unusual architecture, dubbed “Deadglyph,” used in a cyber-espionage attack...
The Hot Seat: CISO Accountability in a New Era of SEC Regulation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Sivan Tehila, CEO & Founder, Onyxia Cyber Recent headlines have cast a spotlight on the evolving nature of cyber threats and their...
Cyber Hygiene: A First Line of Defense Against Evolving Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Basic security hygiene is more impactful than you may realize. While industry headlines are often dominated by emerging tech...
Don’t Get Burned by CAPTCHAs: A Recipe for Accurate Bot Protection – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 One of the more pervasive online threats comes from cybercriminals programming bots to roam the Internet looking for ways to manipulate...
Ukrainian Military Targeted in Phishing Campaign Leveraging Drone Manuals – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 25, 2023THNCyber Attack / Phishing Ukrainian military entities are the target of a phishing campaign that leverages drone manuals as...
Are You Willing to Pay the High Cost of Compromised Credentials? – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 25, 2023The Hacker NewsPassword Security / Cybersecurity Weak password policies leave organizations vulnerable to attacks. But are the standard password...
6 steps to stop ransomware from taking you hostage – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Ransomware is a growing threat, especially for US-based organizations. Cyber criminals increasingly focus on “triple extortion” ransomware attacks, which...
GUEST ESSAY: A roadmap for the finance teams at small businesses to improve cybersecurity – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Neil Taurins If you’re a small business looking for the secret sauce to cybersecurity, the secret is out: start with...
How Will SEC Rules Affect Reporting, Tracking of Incidents? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Security Operations , Standards, Regulations & Compliance TrustedSec’s Alex Hamerstone on New US Securities and Exchange Commission Rules...
Cloud Smart Roadshow Irving (Dallas): Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Cloud Security , Next-Generation Technologies & Secure Development Presented by VMware 300 Minutes...
Cloud Smart Roadshow San Diego: Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Cloud Data Security & Resilience , Next-Generation Technologies & Secure Development Presented by VMware ...
Data Breach Toll Tied to Clop Group’s MOVEit Attacks Surges – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Incident & Breach Response 2,050 Organizations Affected After Data Stolen From Secure File-Sharing Software...
Cloud Smart Roadshow San Jose: Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Presented by VMware 300 Minutes Learn how to navigate the cloud landscape with VMware, your compass for...
Cloud Smart Roadshow Los Angeles: Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Presented by VMware 300 Minutes Learn how to navigate the cloud landscape with VMware, your compass for...
Stealthy APT Gelsemium Seen Targeting Southeast Asian Government – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A stealthy advanced persistent threat (APT) actor known as Gelsemium has been observed targeting a government entity in Southeast Asia...
Nigerian Pleads Guilty in US to Million-Dollar BEC Scheme Role – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A Nigerian national residing in South Africa last week pleaded guilty in court in the United States to his role...
900 US Schools Impacted by MOVEit Hack at National Student Clearinghouse – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The National Student Clearinghouse, an educational nonprofit that provides reporting, verification, and research services to colleges and universities in North...