The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Zero Trust Matutity Model by CISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Real Cyber War – The Political Economy of Internet Freedom by Shawn Powers & Michael Jablonski
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Hack the Cybersecurity Interview – A complete Interview Preparation Guide for jumpstarting your cybersecurity career by Ken Underhill – Christophe Fulon – Tia Hopkins – Packt
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity for Dummies by Lawrence C. Miller
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
0-days Detected in-the-Wild in 2022 – Year in Review – Maddie Stone – Zer0Con 2023 – Google
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Classic Intrusion Analysis Frameworks for AWS Environments: Application and Enhancement by AWS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Practical Guide for CSIRTs by OAS – A Sustainable Business Model.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Executive Guide to Cyber Crisis Management 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NEW TO DFIR – FIELD MANUAL – The Ultimate Guide Getting Started in Forensics & Incident Response (DFIR) by SANS DFIR
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Boards Are Having the Wrong Conversations About Cybersecurity – Board interactions with the CISO are lacking – by Lucia Millica and Keri Pearlson – Harvard Business Review
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DevSecOps Guides – Comprehensive resource for integrating security into the software development by HADESS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Data Leakage for Dummies by Lawrence C. Miller
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
4 Steps to Building a Master Blue Team Home Lab by Logan Simpson
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DEFENCE-IN-DEPTH – Security Myths, Popular Pursuits, Reality & Concealed Vulnerabilities by The Security Institute Fellow
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Awareness for dummies series by Ira Winkler
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
So You Want To Be a Hacker – A story guide by Logan Simpson
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Personal Cyber Security First Steps by Australian Government – ACSC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SANS Offensive Operations – ChatGPT for Offensive Security – What is ChatGPT and how can it be used in offensive security ?
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Report on the Biden Laptop by Marco Polo
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
10 top scams to watch out for this fall – You won’t believe #5 – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: As either a business or as an individual, losing financial resources to scams and fraud can be deeply difficult,...
FBI Warns of Rising Trend of Dual Ransomware Attacks Targeting U.S. Companies – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 30, 2023THNRansomware / Cyber Threat The U.S. Federal Bureau of Investigation (FBI) is warning of a new trend of dual...
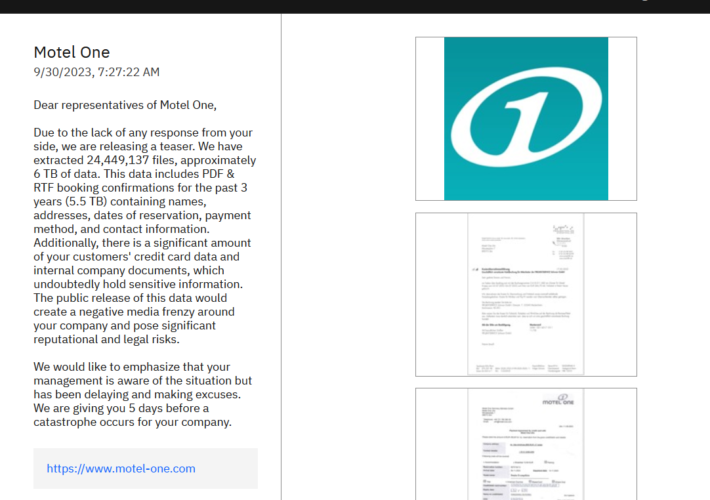
ALPHV/BlackCat ransomware gang hacked the hotel chain Motel One – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini ALPHV/BlackCat ransomware gang hacked the hotel chain Motel One Pierluigi Paganini September 30, 2023 The ALPHV/BlackCat ransomware gang added the...
FBI warns of dual ransomware attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini FBI warns of dual ransomware attacks Pierluigi Paganini September 30, 2023 The U.S. Federal Bureau of Investigation (FBI) warns of...
Progress Software fixed two critical severity flaws in WS_FTP Server – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Progress Software fixed two critical severity flaws in WS_FTP Server Pierluigi Paganini September 30, 2023 Progress Software has addressed a...
Child abuse site taken down, organized child exploitation crime suspected – exclusive – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Child abuse site taken down, organized child exploitation crime suspected – exclusive Pierluigi Paganini September 30, 2023 A child abuse...
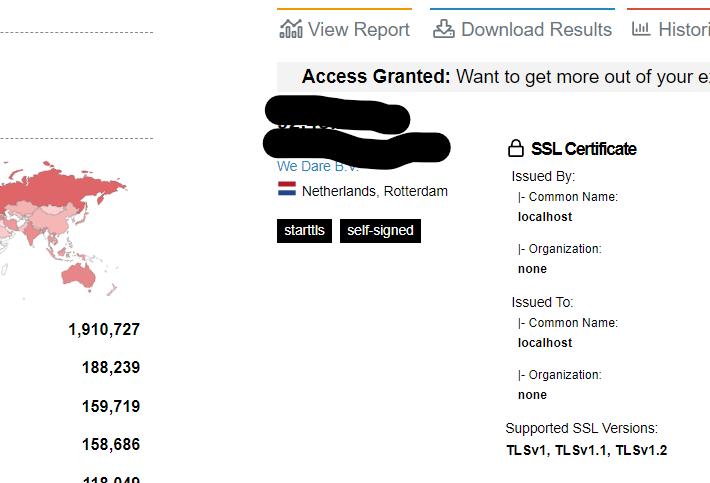
A still unpatched zero-day RCE impacts more than 3.5M Exim servers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A still unpatched zero-day RCE impacts more than 3.5M Exim servers Pierluigi Paganini September 29, 2023 Experts warn of a...
Vulns Found In Another Progress Software File Transfer App – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Patch Management ‘There’s a 10-out-10 severity bug you need to patch right now!’ Prajeet Nair (@prajeetspeaks)...
Inside Look: FDA’s Cyber Review Process for Medical Devices – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security , Hardware / Chip-level Security , Healthcare Jessica Wilkerson of the FDA Details Agency’s ‘Refuse to Accept’ Policy and...