Source: securityboulevard.com – Author: Jenn Sherman It’s been a few weeks now since Carahsoft’s FedRAMP Headliner Summit, but there is no shortage of moments to recall...
Threat Groups Accelerating the Use of Dual Ransomware Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Ransomware groups are shrinking the time between attacks on the same victim, sometimes targeting the same company twice within 48...
Must-read Cyber Security Awareness Month insights from an industry expert – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Lari Luoma has over 20 years of experience working in the fields of security and networking. For the last 11 years,...
GUEST ESSAY: Has shielding and blocking electromagnetic energy become the new normal? – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Nikoline Arns Surrounded by the invisible hum of electromagnetic energy, we’ve harnessed its power to fuel our technological marvels for...
EU Lawmaker Questions CSAM Proposal ‘Conflicts of Interest’ – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Encryption & Key Management , Legislation & Litigation , Security Operations LIBE Committee Chair Seeks Clarifications from EU Home Affairs Minister...
Some Prospect Medical Hospitals in Dire State, Post-Attack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Continued Operation of 3 Connecticut Hospitals Now in Question Marianne Kolbasuk McGee...
Live Webinar ANZ | Achieving Air Gapped Security on VMs in Azure – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Alert: Attackers Actively Exploiting WS_FTP Vulnerabilities – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Attack Surface Management , Critical Infrastructure Security Cybersecurity Officials Recommend Immediate Patching to Fix Serious Flaws...
Chertoff Group Arm to Buy Trustwave from Singtel for $205M – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Managed Detection & Response (MDR) , Managed Security Service Provider (MSSP) MSSP, MDR Provider Lost Nearly...
Common Errors When Connecting Multiple iPhones to One Apple ID – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Erik Eckel Although connecting two iPhones to the same Apple ID has its advantages — including expanding your or a partner’s access...
Cyberghost VPN Review (2023): Features, Pricing, and Security – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares CyberGhost VPN Fast facts Our rating: 4.3 stars out of 5 Pricing: Starts at $2.11 per month Key features: Offers...
FBI Warns of Dual Ransomware Attacks and Data Destruction Trends – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US Federal Bureau of Investigation (FBI) has issued a Private Industry Notification highlighting two concerning trends in the world of...
BunnyLoader Malware Targets Browsers and Cryptocurrency – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Zscaler ThreatLabz has identified a newly emerging Malware-as-a-Service (MaaS) threat known as “BunnyLoader,” available on underground forums. The tool, priced at...
AI-Generated Phishing Emails Almost Impossible to Detect, Report Finds – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The potential for cybercriminals to use AI chatbots to create phishing campaigns has been cause for concern and now it has...
Nearly 100,000 Industrial Control Systems Exposed to the Internet – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Thousands of organizations around the world are using industrial control systems (ICS) exposed to the public internet, new analysis from Bitsight...
Cybersecurity Awareness Month Celebrates 20 Years – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity Awareness Month was founded in 2004 and this year sees the initiative celebrate 20 years of raising awareness of security...
Cigna Agrees $172m Payment to Settle Fraud Allegations – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A leading health insurer has agreed to pay over $172m to resolve charges it seriously violated the False Claims Act by...
Royal Family Website Downed by DDoS Attack – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The official website of the UK’s royal family was taken offline by a distributed denial of service (DDoS) attack on Sunday,...
US, UK, and Democratic Nations Unite to Combat Cyber-Threats to Civil Society – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security agencies from the US and UK last week convened a meeting off democratic nations designed to find new ways of...
WS_FTP flaw CVE-2023-40044 actively exploited in the wild – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini WS_FTP flaw CVE-2023-40044 actively exploited in the wild Experts warn of threat actors actively exploiting CVE-2023-40044 flaw in recently disclosed...
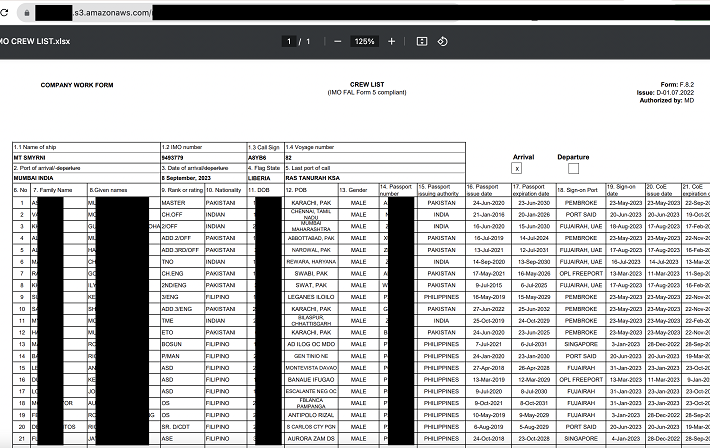
National Logistics Portal (NLP) data leak: seaports in India were left vulnerable to takeover by hackers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini National Logistics Portal (NLP) data leak: seaports in India were left vulnerable to takeover by hackers The National Logistics Portal...
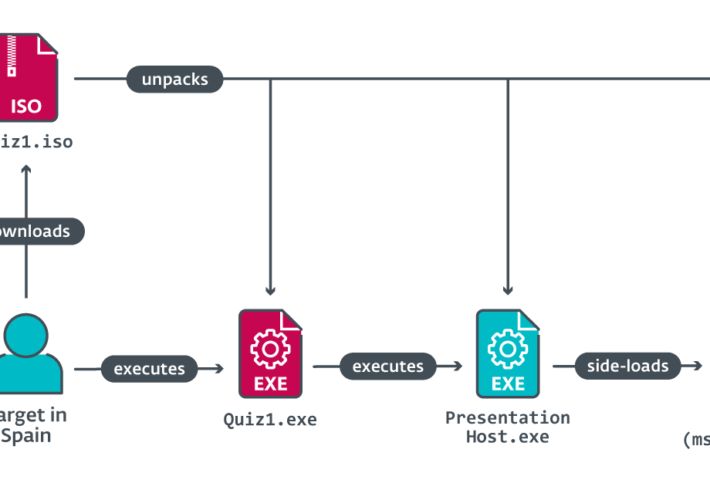
North Korea-linked Lazarus targeted a Spanish aerospace company – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini North Korea-linked Lazarus targeted a Spanish aerospace company North Korea-linked APT group Lazarus impersonated Meta’s recruiters in an attack against...
Ransomware attack on Johnson Controls may have exposed sensitive DHS data – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ransomware attack on Johnson Controls may have exposed sensitive DHS data Experts warn that the recent attack on building automation...
LUCR-3: Scattered Spider Getting SaaS-y in the Cloud – Source:thehackernews.com
Source: thehackernews.com – Author: . LUCR-3 overlaps with groups such as Scattered Spider, Oktapus, UNC3944, and STORM-0875 and is a financially motivated attacker that leverages the...
APIs: Unveiling the Silent Killer of Cyber Security Risk Across Industries – Source:thehackernews.com
Source: thehackernews.com – Author: . Introduction In today’s interconnected digital ecosystem, Application Programming Interfaces (APIs) play a pivotal role in enabling seamless communication and data exchange...
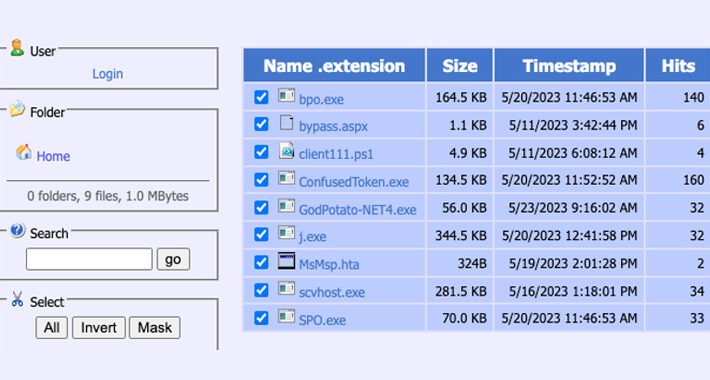
Silent Skimmer: A Year-Long Web Skimming Campaign Targeting Online Payment Businesses – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 02, 2023THNWebb Security / Payment Security A financially motivated campaign has been targeting online payment businesses in the Asia Pacific,...
Don’t Let Zombie Zoom Links Drag You Down – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Many organizations — including quite a few Fortune 500 firms — have exposed web links that allow anyone to initiate a...
Logic Flaws Let Attackers Bypass Cloudflare’s Firewall and DDoS Protection – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac The effectiveness of Cloudflare’s Firewall and DDoS prevention has been proven to be compromised by an attack technique that takes...
Iran-Linked APT34 Spy Campaign Targets Saudis – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A phishing campaign which drops cyber espionage malware is taking aim at users in the Middle East....
Which DFIR Challenges Does the Middle East Face? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nick Rago, Tech Journalist With a constantly changing digital landscape, enterprises are finding it harder to keep threats at bay. There isn’t...