Source: www.tripwire.com – Author: Graham Cluley US federal agencies have teamed up to release a cybersecurity best practice guidance for the water and wastewater sector (WWS)....
Cracked software beats gold: new macOS backdoor stealing cryptowallets – Source: securelist.com
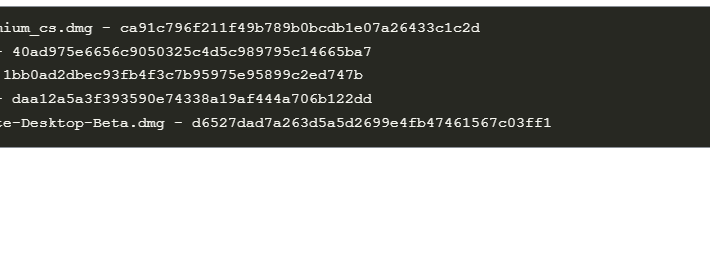
Source: securelist.com – Author: Sergey Puzan A month ago, we discovered some cracked apps circulating on pirating websites and infected with a Trojan proxy. The malicious...
Data Privacy Week: Lack of Understanding, Underfunding Threaten Data Privacy and Compliance – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A lack of understanding combined with budgetary squeezes are significant obstacles for organization’s navigating data privacy and compliance with data protection...
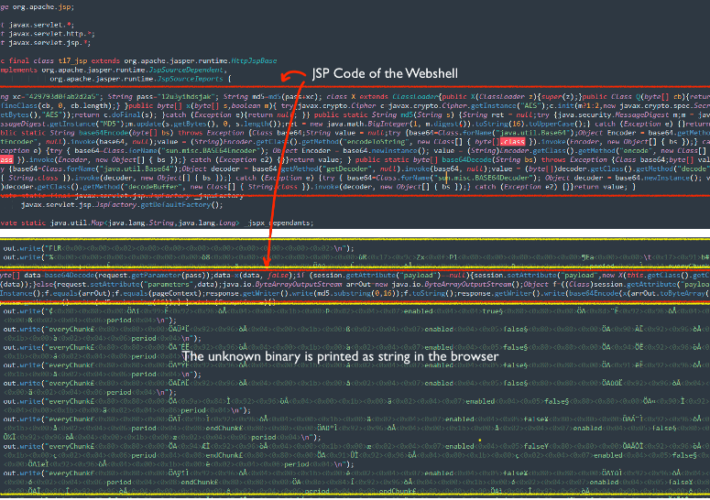
Threat actors exploit Apache ActiveMQ flaw to deliver the Godzilla Web Shell – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Threat actors exploit Apache ActiveMQ flaw to deliver the Godzilla Web Shell Researchers warn of a spike in attacks exploiting...
Cybercriminals leaked massive volumes of stolen PII data from Thailand in Dark Web – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cybercriminals leaked massive volumes of stolen PII data from Thailand in Dark Web Resecurity researchers warn of massive leak of...
Backdoored pirated applications targets Apple macOS users – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Backdoored pirated applications targets Apple macOS users Researchers warned that pirated applications have been employed to deliver a backdoor to...
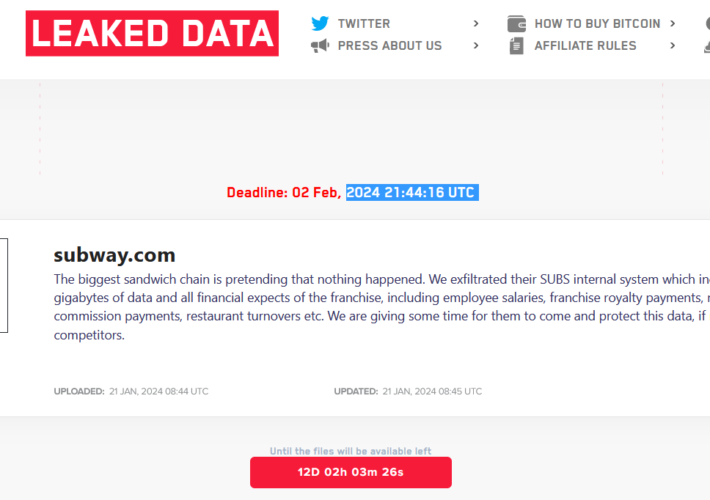
LockBit ransomware gang claims the attack on the sandwich chain Subway – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini LockBit ransomware gang claims the attack on the sandwich chain Subway The LockBit ransomware gang claimed to have hacked Subway,...
FTC Bans InMarket for Selling Precise User Location Without Consent – Source:thehackernews.com
Source: thehackernews.com – Author: . The U.S. Federal Trade Commission (FTC) is continuing to clamp down on data brokers by prohibiting InMarket Media from selling or...
Apache ActiveMQ Flaw Exploited in New Godzilla Web Shell Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 22, 2024NewsroomVulnerability / Malware Cybersecurity researchers are warning of a “notable increase” in threat actor activity actively exploiting a now-patched...
Tietoevry ransomware attack causes outages for Swedish firms, cities – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Finnish IT services and enterprise cloud hosting provider Tietoevry has suffered a ransomware attack impacting cloud hosting customers in one...
Watch out for “I can’t believe he is gone” Facebook phishing posts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams A widespread Facebook phishing campaign stating, “I can’t believe he is gone. I’m gonna miss him so much,” leads unsuspecting...
Brave to end ‘Strict’ fingerprinting protection as it breaks websites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Brave Software has announced plans to deprecate the ‘Strict’ fingerprinting protection mode in its privacy-focused Brave Browser because it causes...
Court charges dev with hacking after cybersecurity issue disclosure – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A German court has charged a programmer investigating an IT problem with hacking and fined them €3,000 ($3,265) for what...
USENIX Security ’23 – Kaiming Cheng, Jeffery F. Tian, Tadayoshi Kohno, Franziska Roesner – Exploring User Reactions and Mental Models Towards Perceptual Manipulation Attacks in Mixed Reality – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the organizations strong commitment to Open...
Welcome to Data Privacy Week: Empowering Your Cybersecurity with BlackCloak – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Pierson The importance of data privacy continues to grow exponentially. We recognize this critical need and are excited to kick off...
Cybersecurity Challenges at the World Economic Forum – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity The 54th Annual Meeting of The World Economic Forum took place in Davos, Switzerland, this past week, and cybersecurity...
Webinar: Join us for the latest in API Threats on January 24, 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: girishwallarm In today’s complex digital landscape, the security of APIs has become paramount. As we move into 2024, it’s essential to stay...
Security Affairs newsletter Round 455 by Pierluigi Paganini – INTERNATIONAL EDITION – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Security Affairs newsletter Round 455 by Pierluigi Paganini – INTERNATIONAL EDITION | Admin of the BreachForums hacking forum sentenced to...
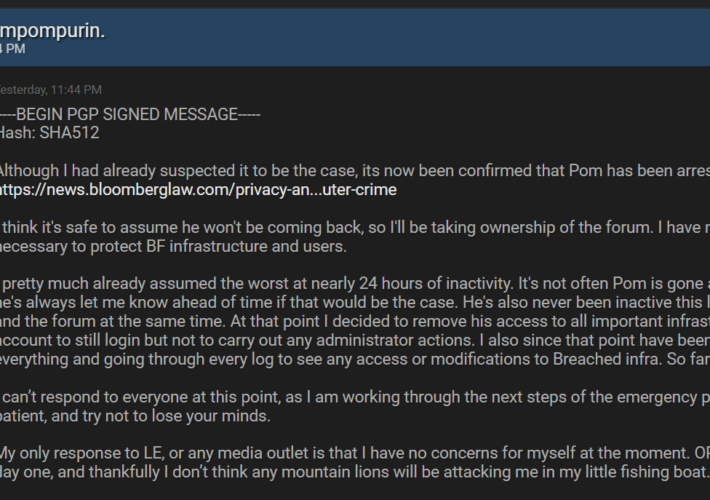
Admin of the BreachForums hacking forum sentenced to 20 years supervised release – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Admin of the BreachForums hacking forum sentenced to 20 years supervised release Conor Brian Fitzpatrick, the admin of the BreachForums...
Russia-linked Midnight Blizzard APT hacked Microsoft corporate emails – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Russia-linked Midnight Blizzard APT hacked Microsoft corporate emails Microsoft revealed that the Russia-linked APT Midnight Blizzard has compromised some of...
Weekly Update 383 – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt They’re an odd thing, credential lists. Whether they’re from a stealer as in this week’s Naz.API incident, or just aggregated...
USENIX Security ’23 – Unique Identification of 50,000+ Virtual Reality Users from Head & Hand Motion Data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Vivek Nair, Wenbo Guo, Justus Mattern, Rui Wang, James F. O’Brien, Louis Rosenberg, Dawn Song Many thanks to USENIX...
Book Review: The Crypto Launderers: Crime and CryptoCurrencies – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gary Warner The Crypto Launderers: Crime and Cryptocurrencies from the Dark Web to DeFi and Beyond – by David Carlisle I...
Your data is under siege. Here’s how to win the war. – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog I consider myself pretty savvy when it comes to protecting my personal data. But last year I nearly fell for...
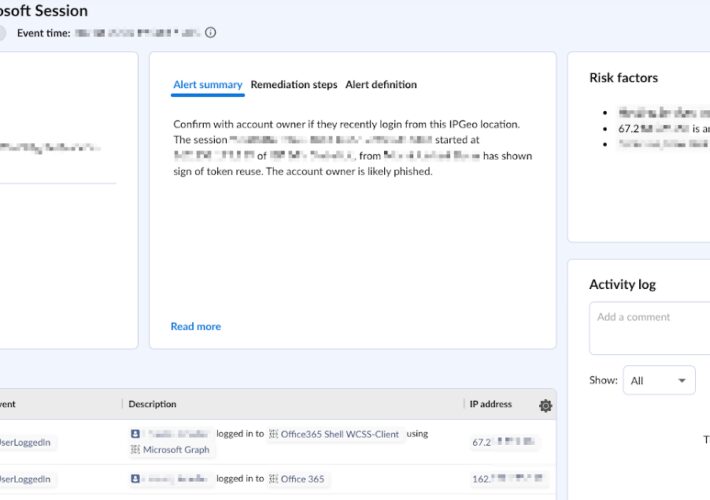
Behind the Breach: Pass-The-Cookie Beyond IdPs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lila Joy Ginsberg Pass-The-Cookie (PTC), also known as token compromise, is a common attack technique employed by threat actors in SaaS environments. ...
Unlock SaaS Security Intelligence with Splunk and Obsidian – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lila Joy Ginsberg In a world of evolving SaaS security threats, organizations require advanced threat detection and response capabilities. Obsidian’s integration with...
Demystifying Cybersecurity’s Public Companies – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cole Grolmus Quick, how many publicly traded cybersecurity companies are there? Take a guess. I’ll wait. … Struggling to come up with...
Protect Yourself and Freeze Your Credit – Source: securityboulevard.com
Source: securityboulevard.com – Author: Branden Williams Breaches are never ending, and if you have not already put freezes on your credit reports, make a late New...
BreachForums Admin Avoids Prison Term – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cryptocurrency Fraud , Cybercrime , Fraud Management & Cybercrime ‘Pompompurin’ Sentenced to Supervised Release, Banned From Internet for 1 Year Prajeet...
Microsoft: Russian Hackers Had Access to Executives’ Emails – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Computing Giant Says Hackers Did Not Access Customer Data or Production Systems...