Source: www.bleepingcomputer.com – Author: Bill Toulas A phishing campaign detected in late November 2023 has compromised hundreds of user accounts in dozens of Microsoft Azure environments,...
CISA: Roundcube email server bug now exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan CISA warns that a Roundcube email server vulnerability patched in September is now actively exploited in cross-site scripting (XSS) attacks....
Hackers exploit Ivanti SSRF flaw to deploy new DSLog backdoor – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Hackers are exploiting a server-side request forgery (SSRF) vulnerability in Ivanti Connect Secure, Policy Secure, and ZTA gateways to deploy...
Free Rhysida ransomware decryptor for Windows exploits RNG flaw – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas South Korean researchers have publicly disclosed an encryption flaw in the Rhysida ransomware encryptor, allowing the creation of a Windows...
Ransomware attack forces 25 Romanian hospitals to go offline – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Over two dozen hospitals in Romania have taken their systems offline after a ransomware attack took down their healthcare management system....
ExpressVPN bug has been leaking some DNS requests for years – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas ExpressVPN has removed the split tunneling feature from the latest version of its software after finding that a bug exposed...
Security Operations and Management
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ransomfeed – Third Quarter Report 2023 is out! – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ransomfeed – Third Quarter Report 2023 is out! Pierluigi Paganini February 13, 2024 Maintainers behind the Ransomfeed platform have released...
Global Malicious Activity Targeting Elections is Skyrocketing – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Global Malicious Activity Targeting Elections is Skyrocketing Pierluigi Paganini February 13, 2024 Resecurity has identified a growing trend of malicious...
Researchers released a free decryption tool for the Rhysida Ransomware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers released a free decryption tool for the Rhysida Ransomware Pierluigi Paganini February 12, 2024 Researchers discovered a vulnerability in...
Residential Proxies vs. Datacenter Proxies: Choosing the Right Option – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Residential Proxies vs. Datacenter Proxies: Choosing the Right Option Pierluigi Paganini February 12, 2024 Residential Proxies vs. Datacenter Proxies: this...
CISA adds Roundcube Webmail Persistent XSS bug to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini CISA adds Roundcube Webmail Persistent XSS bug to its Known Exploited Vulnerabilities catalog Pierluigi Paganini February 12, 2024 U.S. Cybersecurity...
Canada Gov plans to ban the Flipper Zero to curb car thefts – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Canada Gov plans to ban the Flipper Zero to curb car thefts Pierluigi Paganini February 12, 2024 The Canadian government...
ExpressVPN leaked DNS requests due to a bug in the split tunneling feature – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini ExpressVPN leaked DNS requests due to a bug in the split tunneling feature Pierluigi Paganini February 12, 2024 A bug...
9 Possible Ways Hackers Can Use Public Wi-Fi to Steal Your Sensitive Data – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini 9 Possible Ways Hackers Can Use Public Wi-Fi to Steal Your Sensitive Data Pierluigi Paganini February 12, 2024 Exploring the...
US Feds arrested two men involved in the Warzone RAT operation – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US Feds arrested two men involved in the Warzone RAT operation Pierluigi Paganini February 12, 2024 The U.S. Justice Department...
Raspberry Robin spotted using two new 1-day LPE exploits – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Raspberry Robin spotted using two new 1-day LPE exploits Pierluigi Paganini February 11, 2024 Raspberry Robin continues to evolve, it...
Security testing White Paper
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cloud Reassurance: A Framework To Enhance Resilience And Trust
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Reporting Cyber Risk to Boards
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 Visa Merchant Fraud Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Insider Data Breach at Verizon Affects Over 63,000 Employees – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici An insider data breach at Verizon has compromised the personal information of more than 63,000 employees, nearly half of the...
Credentialess / Username
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 Cybersecurity Regulation Recap (Part 4): Tech Development & Governance – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS In 2023, countries worldwide continued to strengthen their cybersecurity capabilities and systems in response to their national needs, using regulatory means...
Single Sign-On with Fortra IdP – Source: securityboulevard.com
Source: securityboulevard.com – Author: Digital Defense by Fortra What is Fortra IdP? Fortra Identity Provider (IdP) serves as a centralized solution that allows users to log...
USENIX Security ’23 – Internet Service Providers’ And Individuals’ Attitudes, Barriers, And Incentives To Secure IoT – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Nissy Sombatruang, Tristan Caulfield, Ingolf Becker, Akira Fujita, Takahiro Kasama, Koji Nakao, Daisuke Inoue Many thanks to USENIX for...
Cybersecurity and the Law: Taking Proactive Steps Before Needing Legal Action – Source: securityboulevard.com
Source: securityboulevard.com – Author: Digital Defense by Fortra How the justice system deals with cybercrime is still relatively new and finding its footing. How cybercriminals are...
Breaking Bitlocker – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rick It was only a matter of time before someone did this. Bitlocker is Microsoft’s technique for encrypting a desktop, laptop, or...
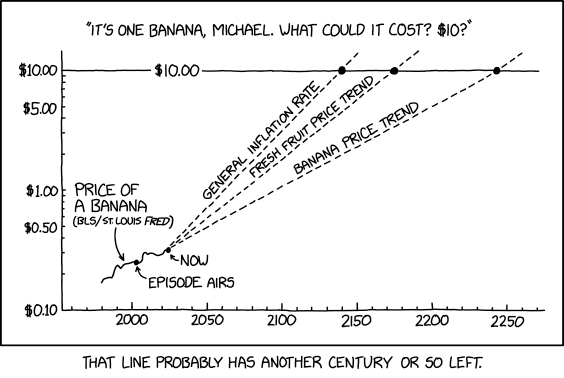
Randall Munroe’s XKCD ‘Banana Prices’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...