Source: www.theguardian.com – Author: Presented by Nosheen Iqbal with Alex Hern and Jon DiMaggio; produced by Ned Carter Miles; executive editor Homa Khaleeli A ransomware site...
Russia-based LockBit ransomware hackers attempt comeback – Source: www.theguardian.com
Source: www.theguardian.com – Author: Dan Milmo Global business editor The LockBit ransomware gang is attempting a comeback days after its operations were severely disrupted by a...
A penny per email could curb our enormous data use | Letters – Source: www.theguardian.com
Source: www.theguardian.com – Author: Guardian Staff The long read (Power grab: the hidden costs of Ireland’s datacentre boom, 15 February) highlights the enormous cost in terms...
Seized ransomware network LockBit rewired to expose hackers to world – Source: www.theguardian.com
Source: www.theguardian.com – Author: Alex Hern The entire “command and control” apparatus for the ransomware group LockBit is now in possession of law enforcement, the UK’s...
Prolific cybercrime gang disrupted by joint UK, US and EU operation – Source: www.theguardian.com
Source: www.theguardian.com – Author: Reuters LockBit, a notorious cybercrime gang that holds its victims’ data to ransom, has been disrupted in a rare international law enforcement...
Hackers got nearly 7 million people’s data from 23andMe. The firm blamed users in ‘very dumb’ move – Source: www.theguardian.com
Source: www.theguardian.com – Author: Mack DeGeurin Three years ago, a man in Florida named JL decided, on a whim, to send a tube of his spit...
Power grab: the hidden costs of Ireland’s datacentre boom – Source: www.theguardian.com
Source: www.theguardian.com – Author: Jessica Traynor In the doldrum days between Christmas and New Year, we take a family trip to see a datacentre. Over the...
Ex-Post Office boss ‘gave Fujitsu bonus contract despite warnings’ – Source: www.theguardian.com
Source: www.theguardian.com – Author: Daniel Boffey Chief reporter The former Post Office boss Paula Vennells gave Fujitsu a bonus contract in 2013 to take over an...
Man arrested in Malta in global operation to shut down cybercrime network targeting Australians – Source: www.theguardian.com
Source: www.theguardian.com – Author: Daisy Dumas A man has been arrested as part of an international operation to shut down a global cybercrime network targeting Australians...
Hardware Vulnerability in Apple’s M-Series Chips – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier It’s yet another hardware side-channel attack: The threat resides in the chips’ data memory-dependent prefetcher, a hardware optimization that predicts...
Security Vulnerability in Saflok’s RFID-Based Keycard Locks – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier It’s pretty devastating: Today, Ian Carroll, Lennert Wouters, and a team of other security researchers are revealing a hotel keycard...
On Secure Voting Systems – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Andrew Appel shepherded a public comment—signed by twenty election cybersecurity experts, including myself—on best practices for ballot marking devices and...
Licensing AI Engineers – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Licensing AI Engineers The debate over professionalizing software engineers is decades old. (The basic idea is that, like lawyers and...
Implementing ZTA: Benefits and Best Practices – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Eric Sugar, President, ProServeIT In an era defined by the relentless advance of digitalization and the ever-expanding interconnectivity of...
Attackers Keep Evolving: Lessons from Expel’s Q2 2023 Quarterly Threat Report – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Cyberdefenders plug the holes, so attackers innovate to try to stay ahead. By Aaron Walton, Threat Intel Analyst, Expel Most...
New Darcula phishing service targets iPhone users via iMessage – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new phishing-as-a-service (PhaaS) named ‘Darcula’ uses 20,000 domains to spoof brands and steal credentials from Android and iPhone users...
Indicators of Compromise
Effectively apply threat information The document provides insights into Indicators of Compromise (IoCs) and their significance in detecting threats within networks. It emphasizes the importance of...
Windows 11 KB5035942 update enables Moment 5 features for everyone – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has released the March 2024 non-security KB5035942 preview update for Windows 11 23H2, which enables Moment 5 features by...
NTIA Pushes for Independent Audits of AI Systems – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific Accountability Needed to Unleah Full Potential of AI, Says NTIA Administrator...
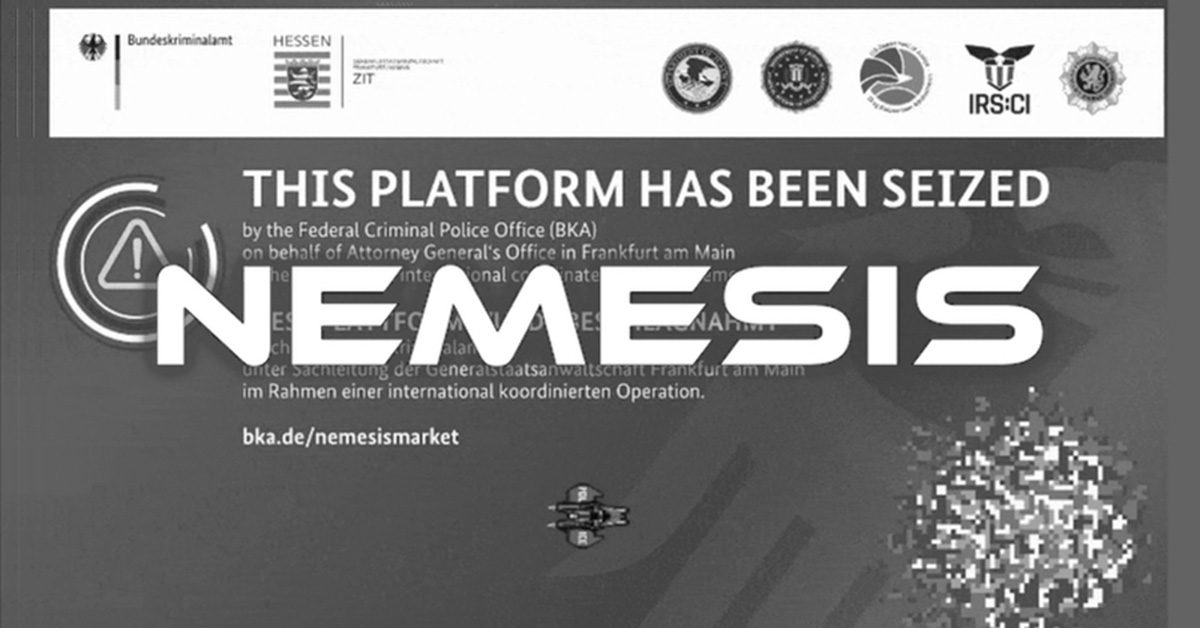
Notorious Nemesis Market zapped by video game-loving German police – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley Nemesis Market, a notorious corner of the darknet beloved by cybercriminals and drug dealers, has been suddenly shut down after...
Estudio de análisis de firmware en dispositivos industriales
La presente guía pretende explicar en mayor medida todo sobre el firmware de dispositivos IoT, tanto a nivel teórico-técnico como una explicación práctica sobre como analizar...
IMPORTANT ACTIVE DIRECTORY ATTRIBUTE
The document provides insights into various attributes, privileges, and attack vectors related to Active Directory security. It discusses the importance of analyzing Group Policy Objects (GPOs)...
GETTING STARTED IN INDUSTRIAL (ICS/OT) CYBER SECURITY
Mike Holcomb is the Fellow of Cybersecurity and the ICS/OT Cybersecurity Global Lead for Fluor, one of the world’s largest engineering, procurement, and construction companies. His...
What are the Essential Skills for Cyber Security Professionals in 2024? – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Where should you invest time and resources to drive success when it comes to the must-have skills and tools for...
Enhancing The Nation’s Cybersecurity Workforce – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Supporting Critical Infrastructure Resilience with Skill-Based Labor By Randall Sandone, Executive Director, Critical Infrastructure Resilience Institute at The Grainger College...
Riding the Waves of Compliance
Navigating PCI DSS v4.0 The document provides detailed information on the PCI DSS v4.0 requirements and best practices for compliance until March 31, 2025. It outlines...
US fines man $9.9 million for thousands of disturbing robocalls – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A U.S. federal court has issued a $9,918,000 penalty and an injunction against an individual named Scott Rhodes for making...
Panera Bread experiencing nationwide IT outage since Saturday – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Since Saturday, U.S. food chain giant Panera Bread has been experiencing a nationwide outage that has impacted its IT systems,...
It’s not just you: ChatGPT is down for many worldwide – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Update added to the bottom of the article. OpenAI’s ChatGPT is down for many people worldwide, with users facing multiple...
US sanctions crypto exchanges used by Russian darknet market, banks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) has sanctioned three cryptocurrency exchanges for working with OFAC-designated Russian...