Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Former Amazon security engineer Shakeeb Ahmed was sentenced to three years in prison for hacking two cryptocurrency exchanges in July...
Former AT&T customers get $6.3 million in data throttling refunds – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Federal Trade Commission (FTC) is sending out $6,300,000 in partial refunds to 267,000 former AT&T Wireless customers as part...
Roku warns 576,000 accounts hacked in new credential stuffing attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Roku warns that 576,000 accounts were hacked in new credential stuffing attacks after disclosing another incident that compromised 15,000 accounts...
Palo Alto Networks warns of PAN-OS firewall zero-day used in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Today, Palo Alto Networks warns that an unpatched critical command injection vulnerability in its PAN-OS firewall is being actively exploited...
Zero Trust Access for Dummies Fortinet
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Zero Trust Implementation Strategy
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Your Business and Cyber Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Xeno RAT- A New Remote Access Trojan
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Windows Persistence COM Hijacking MITRE T1546 015
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Windows Exploitation Rundll32
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Checklist: Securing Digital Information – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Digital information is generally the lifeblood of any given organization, containing essential company data needed to run the business. Paperless offices have...
Windows Exploitation Msbuild
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Web LLM Attacks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Trended Protocols for Security Stuff
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Transferencia Internacional de Datos Personales – Guia de Implementación
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TRACKING RANSOMWARE January 2024
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
East Central University suffers BlackSuit ransomware attack – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley The East Central University (ECU) of Ada, Oklahoma, has revealed that a ransomware gang launched an attack against its systems...
DragonForce ransomware – what you need to know – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley What’s going on? A relatively new strain of ransomware called DragonForce has making the headlines after a series of high-profile...
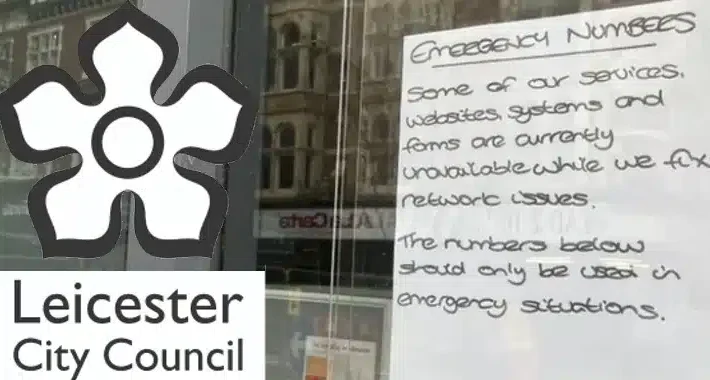
When a breach goes from 25 documents to 1.3 terabytes… – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Ouch. On 7 March 2024, the UK’s Leicester City Council had its systems disrupted by a devastating cyber attack, forcing...
Backdoor in XZ Utils That Almost Happened – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Last week, the internet dodged a major nation-state attack that would have had catastrophic cybersecurity repercussions worldwide. It’s a catastrophe...
How One Industry Exemplifies the Importance Of Cybersecurity In Critical Infrastructure Assurance – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin And What We Can Learn From It By Brian Hesse, Co-Owner, President, and Chief Executive Officer of PerenniAL Summary Cybersecurity professionals,...
XZ backdoor story – Initial analysis – Source: securelist.com
Source: securelist.com – Author: GReAT On March 29, 2024, a single message on the Openwall OSS-security mailing list marked an important discovery for the information security,...
CISA: Russian Hackers Stole Emails Between U.S. Agencies and Microsoft – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Russian state-sponsored hackers who broke into Microsoft’s corporate email accounts during the monthslong hack stole email messages between the enterprise...
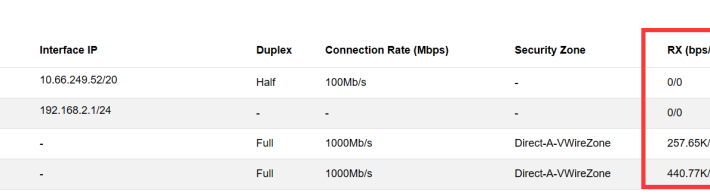
NIPS Troubleshooting Steps for No Log – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS NIPS aims to accurately monitor abnormal network traffic, automatically blocking various types of aggressive traffic in real-time, particularly application layer threats....
Sisense Data Breach Notice for Hyperproof Customers – Source: securityboulevard.com
Source: securityboulevard.com – Author: Hyperproof Team At Hyperproof, safeguarding our customers’ data is our utmost priority. We understand the importance of trust and transparency, especially in...
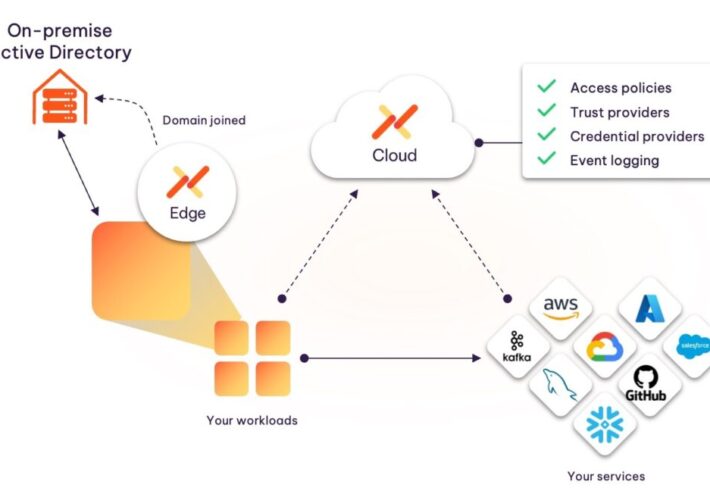
Introducing the Aembit Kerberos Trust Provider – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ashur Kanoon Today’s development environments have evolved greatly, with a high dependence on cloud-deployed SaaS tools. However, most organizations are still running...
Google Extends Generative AI Reach Deeper into Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Google this week extended its effort to apply generative artificial intelligence (AI) to cybersecurity by adding an ability to summarize...
Simbian Unveils Generative AI Platform to Automate Cybersecurity Tasks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Simbian today launched a cybersecurity platform that leverages generative artificial intelligence (AI) to automate tasks that can increase in complexity...
Are you prepared for Google’s 90-day validity period on TLS certificates? – Source: securityboulevard.com
Source: securityboulevard.com – Author: AnneMarie Avalon Google’s proposal for a 90-day validity period on TLS certificates is a game-changer for digital certificate management. It’s not just...
How to Create a Cybersecurity Incident Response Plan – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Kelly Editor’s note: With the increased prevalence of ransomware and other cyberattacks, now is the time to take a moment to...