Source: www.bleepingcomputer.com – Author: Sergiu Gatlan IT security software company Ivanti has released patches to fix multiple security vulnerabilities impacting its Connect Secure and Policy Secure...
Author: CISO2CISO Editor 2
Google fixes one more Chrome zero-day exploited at Pwn2Own – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Google has fixed another zero-day vulnerability in the Chrome browser, which was exploited by security researchers during the Pwn2Own hacking...
AT&T faces lawsuits over data breach affecting 73 million customers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas AT&T is facing multiple class-action lawsuits following the company’s admission to a massive data breach that exposed the sensitive data...
LockBit Ransomware Takedown Strikes Deep Into Brand’s Viability – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Jan Zwoliński via Alamy Stock Photo Despite the LockBit ransomware-as-a-service (RaaS) gang claiming to...
More Than Half of Organizations Plan to Adopt AI Solutions in Coming Year, Reports Cloud Security Alliance and Google Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SEATTLE – April 3, 2024 – A new survey from the Cloud Security Alliance (CSA), the world’s leading organization dedicated...
CyberRatings.org Announces Test Results for Cloud Network Firewall – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Austin, TX – April 3, 2024 – CyberRatings.org (CyberRatings), the non-profit entity dedicated to providing confidence in cybersecurity products and services...
TAG Report Reveals Endpoint Backup Is Essential to Improving Data Resiliency – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE MINNEAPOLIS, April 2, 2024 – Businesses are facing a critical gap when it comes to protecting endpoint data, according to...
TruCentive Enhances Privacy With HIPAA Compliant Personal Information De-identification – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE PALO ALTO, Calif., April 2, 2024/PRNewswire-PRWeb/ — TruCentive, a leader in incentive automation solutions, announced a significant enhancement to its...
How Soccer’s 2022 World Cup in Qatar Was Nearly Hacked – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: rarrarorro via Shutterstock About six months before the 2022 FIFA World Cup soccer tournament in Qatar, a...
Oil & Gas Sector Falls for Fake Car Accident Phishing Emails – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Frode Koppang via Alamy Stock Photo An updated version of the Rhadamanthys malware-as-a-service (MaaS) is...
Omni Hotel IT Outage Disrupts Reservations, Digital Key Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 2 Min Read Source: Andrew Shurtleff via Alamy Stock Photo Omni Hotels & Resorts last week reportedly experienced an...
Streamlining supply chains | The impact of IoT on transportation and logistics – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Antoinette Hodes, a Check Point Global Solutions Architect and Evangelist with the Check Point Office of the CTO. IoT is...
U.S. Treasury warns financial sector, AI threats “outpacing” security – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: According to a new U.S. Treasury Department report, the financial services industry is extremely vulnerable to cyber threats that...
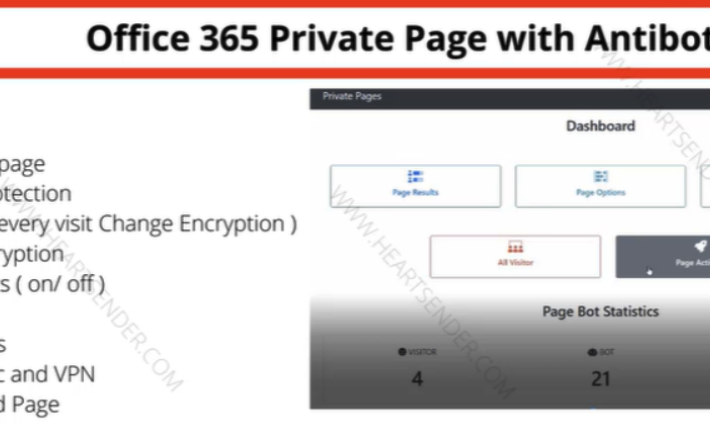
‘The Manipulaters’ Improve Phishing, Still Fail at Opsec – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Roughly nine years ago, KrebsOnSecurity profiled a Pakistan-based cybercrime group called “The Manipulaters,” a sprawling web hosting network of phishing and...
Cyber Safety Review Board Report Slams Microsoft Security Failures in Government Email Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft has been blamed for “cascade of security failures” that enabled Chinese threat actors to access US government officials’ emails in...
Prudential Financial Notifies 36,000 Individuals of Data Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Prudential Financial last Friday commenced the process of informing over 36,000 individuals about a data breach that occurred in early February...
Infostealers Prevalent in Retail Sector Cybercrime Trends – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Infostealers, IoT botnets and remote access tools have been identified as the primary weapons employed by cyber-attackers targeting retail organizations over...
Bridging IT and OT Cybersecurity with AI – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Reduce Alerts by 57% with Difenda AIRO By Andrew Hodges, VP Service Delivery & Product Development, Difenda In a technology-driven...
Accelerate the path to PCI DSS 4.0 adoption – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Héctor Guillermo Martínez, President of GM Sectec With the release of a new version of the PCI DSS 4.0...
Microsoft warns Gmail blocks some Outlook email as spam, shares fix – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has confirmed that some Outlook.com users are experiencing issues with emails being blocked and marked as spam when trying...
Winnti’s new UNAPIMON tool hides malware from security software – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Chinese ‘Winnti’ hacking group was found using a previously undocumented malware called UNAPIMON to let malicous processes run without...
Omni Hotels experiencing nationwide IT outage since Friday – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Omni Hotels & Resorts has been experiencing a chain-wide outage that brought down its IT systems on Friday, impacting reservation,...
New Chrome feature aims to stop hackers from using stolen cookies – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Google announced a new Chrome security feature called ‘Device Bound Session Credentials’ that ties cookies to a specific device, blocking...
Google agrees to delete Chrome browsing data of 136 million users – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Google has agreed to delete billions of data records collected from 136 million Chrome users in the United States, as...
Block Ads And Free Up The Internet For An Extra 20% Off – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published April 3, 2024 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...
xz Utils Backdoor – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier xz Utils Backdoor The cybersecurity world got really lucky last week. An intentionally placed backdoor in xz Utils, an open-source...
Declassified NSA Newsletters – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Through a 2010 FOIA request (yes, it took that long), we have copies of the NSA’s KRYPTOS Society Newsletter, “Tales...
Customer Story | Content Filter Protects Student Safety, Data Security, and CIPA Compliance At Azusa Unified School District – Source: securityboulevard.com
Source: securityboulevard.com – Author: Katie Fritchen How Azusa’s technology team makes web filtering and online safety for students easy with Content Filter by ManagedMethods Like many...
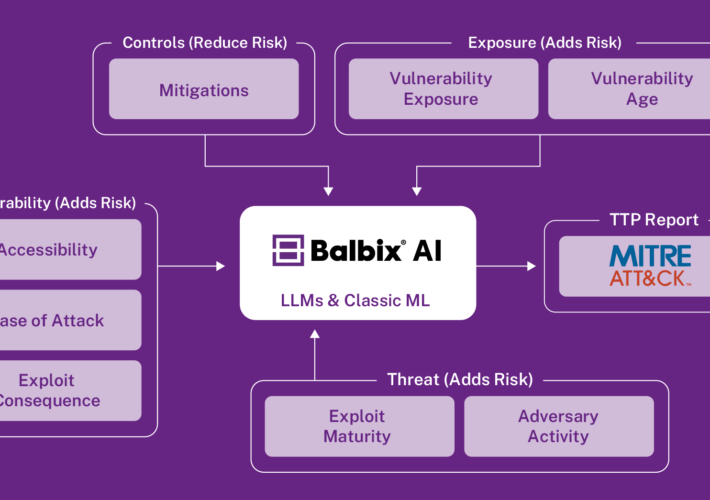
Prioritizing Cyber Risk: Get a leg up with AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aravind Iyengar In the previous blog post, we described how Balbix leverages AI to provide a unified and comprehensive visibility into your...
Guide to New CSRD Regulation for Data Center Operators – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rajan Sodhi In the ever-evolving landscape of corporate sustainability, the European Union’s Corporate Sustainability Reporting Directive (CSRD) stands as a landmark regulation,...