Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: ronstik via Alamy Stock Photo Japanese lens manufacturer Hoya is investigating a cyber incident that...
Author: CISO2CISO Editor 2
How CISOs Can Make Cybersecurity a Long-Term Priority for Boards – Source: www.darkreading.com
Source: www.darkreading.com – Author: Shaun McAlmont 5 Min Read Source: Lev Dolgachov via Alamy Stock Photo COMMENTARY Cybersecurity has never been more critical for responsible corporate...
AI’s Dual Role in SMB Brand Spoofing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Bulat Silvia via Alamy Stock Photo Artificial intelligence (AI) is simultaneously making it easier for adversaries to...
Singapore Sets High Bar in Cybersecurity Preparedness – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Cristophe Coat via Alamy Stock Photo Singapore is leaving other countries in the dust when it comes...
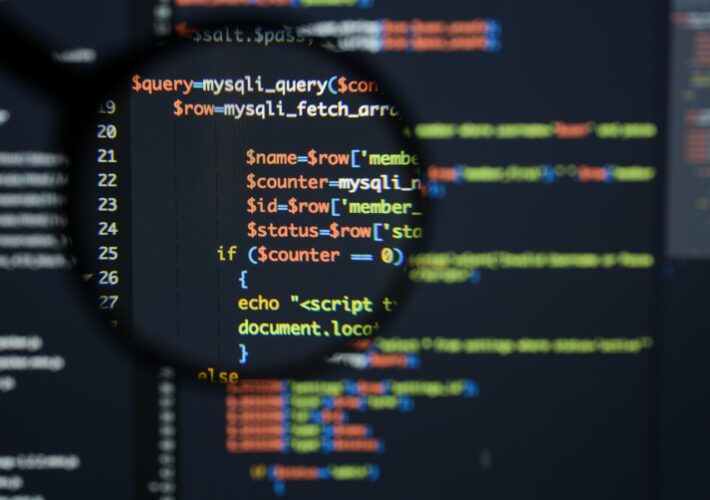
How to Tame SQL Injection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Casimiro PT via Shutterstock For more than a decade, injection vulnerabilities have literally topped the charts of...
Omni Hotel IT Outage Disrupts Reservations, Digital Key Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 2 Min Read Source: Andrew Shurtleff via Alamy Stock Photo Omni Hotels & Resorts last week reportedly experienced an...
The Biggest Mistake Security Teams Make When Buying Tools – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ahmad Sadeddin 4 Min Read Source: Panther Media GmbH via Alamy Stock Photo COMMENTARY I’ve had the pleasure of speaking to hundreds...
Feds to Microsoft: Clean Up Your Cloud Security Act Now – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Wachirawit Lemlerkchai via Alamy Stock Photo A federal review board has called on Microsoft to prioritize its...
Why Cybersecurity Is a Whole-of-Society Issue – Source: www.darkreading.com
Source: www.darkreading.com – Author: Adam Maruyama 4 Min Read Source: Anatolyi Deryenko via Alamy Stock Phot It’s clear from the comments by Jen Easterly, director of...
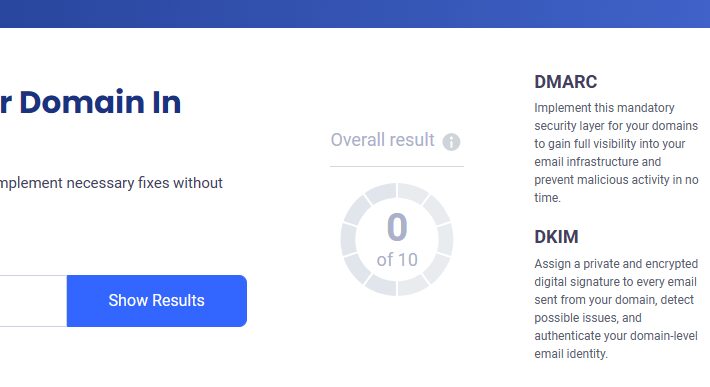
How to Avoid Email Blacklists and Improve Your Deliverability – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeremy Moser Email marketing is a mighty tool for connecting with your target audience. But its effectiveness depends on your emails actually...
Building Trust in Finance: Challenges & Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: sparsh Building trust in the financial industry, from the customer’s point of view. It’s widely accepted that trust is the cornerstone of...
Broadcast Network Finds Multiple Solutions with Votiro – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro This Faith-based Broadcast Network shares its messages via TV and new media in the East Coast market. The Network does this...
Top Signs Your Ad Campaigns Are Being Sabotaged by Bots & How to Stop Them – Source: securityboulevard.com
Source: securityboulevard.com – Author: DataDome There’s plenty of money in advertising, and bots want a piece. As online advertising has risen in prominence and popularity among...
What You Need to Know About Hugging Face – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeff Martin The risk both to and from AI models is a topic so hot it’s left the confines of security conferences...
Biden Review Board Gives Microsoft a Big, Fat Raspberry – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Last year’s Chinese hack of federal agencies’ email is still a mystery, and “should never have occurred,” says CISA. Storm-0558 Forecast...
NIST Proposes Public-Private Group to Help with NVD Backlog – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt An embattled National Institute of Standards and Technology (NIST), hobbled by budget cuts, is looking for more help from both...
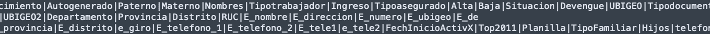
Analyzing Peru’s Cybersecurity Crisis – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alberto Casares In an era where digital integration is pervasive, cybersecurity crisis and the threat of cybersecurity breaches has emerged as a...
Streamlining Third-Party Risk Management: The Top Findings from the 2024 Benchmark Survey Report – Source: securityboulevard.com
Source: securityboulevard.com – Author: Courtney Chatterton As businesses grow and expand their operations, their third-party risk management program grows with them. This growth leads to increased...
Taking the Long View: GitGuardian’s Approach to Market Relevance in Cyber – Source: securityboulevard.com
Source: securityboulevard.com – Author: Eric Fourrier The landscape of appsec is more competitive than ever, but rushing to stay ahead isn’t always the best strategy. In...
Google Proposes Method for Stopping Multifactor Runaround – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Identity & Access Management , Security Operations Device Bound Session Credentials Tie Authentication Cookies to Specific Computers Mihir Bagwe (MihirBagwe) ,...
The US or the UK: Where Should You Get a Cybersecurity Job? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Professional Certifications & Continuous Training , Recruitment & Reskilling Strategy , Training & Security Leadership Differences in How the United States...
Remote Desktop Protocol: An Active Adversary Special Report – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Network Detection & Response , Network Firewalls, Network Access Control What is RDP, why is it...
Deploying Cyber Applications on Your Security Data Lake – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Microsoft still unsure how hackers stole MSA key in 2023 Exchange attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ionut Ilascu The U.S. Department of Homeland Security’s Cyber Safety Review Board (CSRB) has released a scathing report on how Microsoft handled...
SurveyLama data breach exposes info of 4.4 million users – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Data breach alerting service Have I Been Pwned (HIBP) warns that SurveyLama suffered a data breach in February 2024, which...
Omni Hotels confirms cyberattack behind ongoing IT outage – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Omni Hotels & Resorts has confirmed a cyberattack caused a nationwide IT outage that is still affecting its locations. In...
Hosting firm’s VMware ESXi servers hit by new SEXi ransomware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Chilean data center and hosting provider IxMetro Powerhost has suffered a cyberattack at the hands of a new ransomware gang...
Jackson County in state of emergency after ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Jackson County, Missouri, is in a state of emergency after a ransomware attack took down some county services on Tuesday....
US State Department investigates alleged theft of government data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The U.S. Department of State is investigating claims of a cyber incident after a threat actor leaked documents allegedly stolen...
Critical flaw in LayerSlider WordPress plugin impacts 1 million sites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A premium WordPress plugin named LayerSlider, used in over one million sites, is vulnerable to unauthenticated SQL injection, requiring admins...